Bring real time web application attack data into Threat Response
Signal Sciences is a leading web application security company, with a next-gen web application firewall (WAF) and runtime application self-protection (RASP) solution. Signal Sciences protects over 10,000 applications, with over a trillion production requests per month. Signal Sciences’ patented dual module-agent architecture provides organizations working in a modern development environment with comprehensive, scalable threat protection and security visibility.
In late February 2019, the Signal Sciences team was connected by Cisco Security Business Development with the Cisco Threat Response(CTR) ecosystem group. After an initial conference call about technology and APIs, it was clear the engineers should get together to build something. Using the Swagger documentation and a little guidance on which API endpoints to use, the Signal Sciences crew were able to design, build, test, document and show a functional integration within 10 days. It was demonstrated at Cisco Live Melbourne and RSA Conference, simultaneously in the Signal Sciences and Cisco booths.
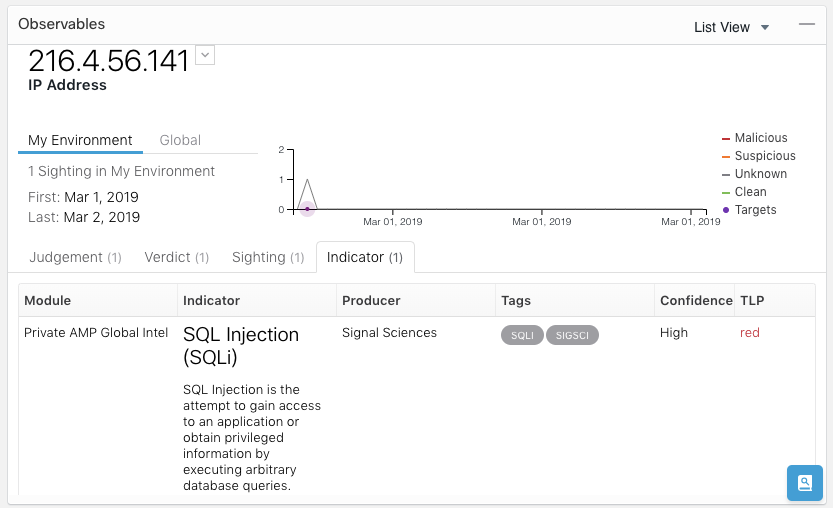
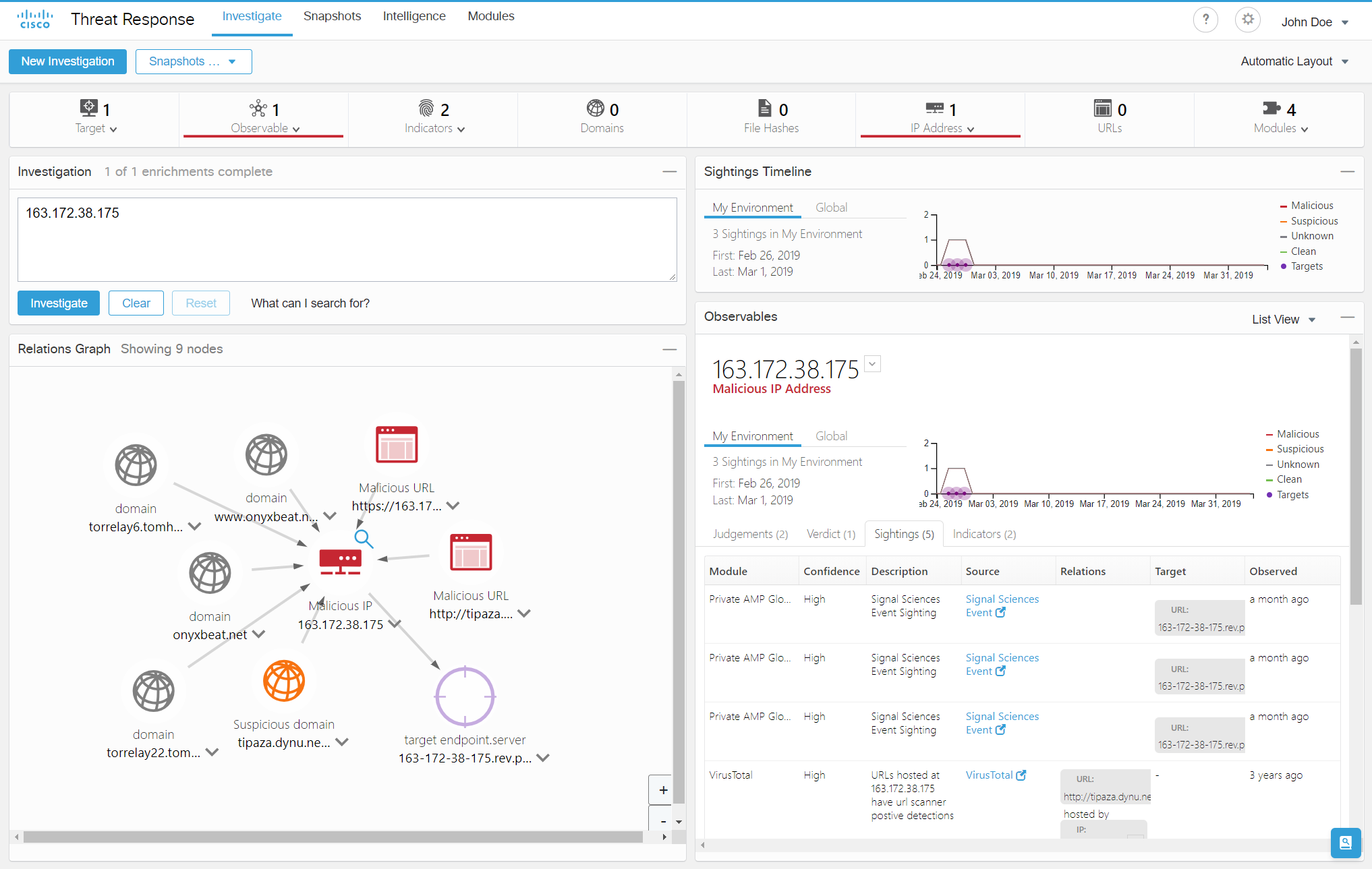
As attacks are detected and blocked, Signal Sciences next-gen WAF sends relevant attack data to Cisco Threat Response; including IP address, indicators and additional metadata. Within Threat Response a sighting of the offending IP address is created and linked to the indicator, which can then be aggregated with all other sightings across Threat Response.
An incident responder can then open a casebook on the observable and initiate a cross-functional investigation. At the same time, a workflow can be initiated within Threat Response to take any corrective actions needed. If more details are needed, the investigator can jump straight to the event in Signal Sciences from Threat Response at the click of a button.
Through the integration, your Security Operations team will have immediate visibility into attacks across all web application workloads.
With the integration, you can take immediate action, including:
- Analyze and correlate event data using context from integrated Cisco Security products and industry leading threat intelligence from Cisco Talos
- Open a case to collect and store key investigative information, orchestrate resources for incident response, and manage and document your progress and findings
- Take corrective actions in other Cisco products to remediate and address the threats across your security stack by monitoring, filtering, and blocking known attackers
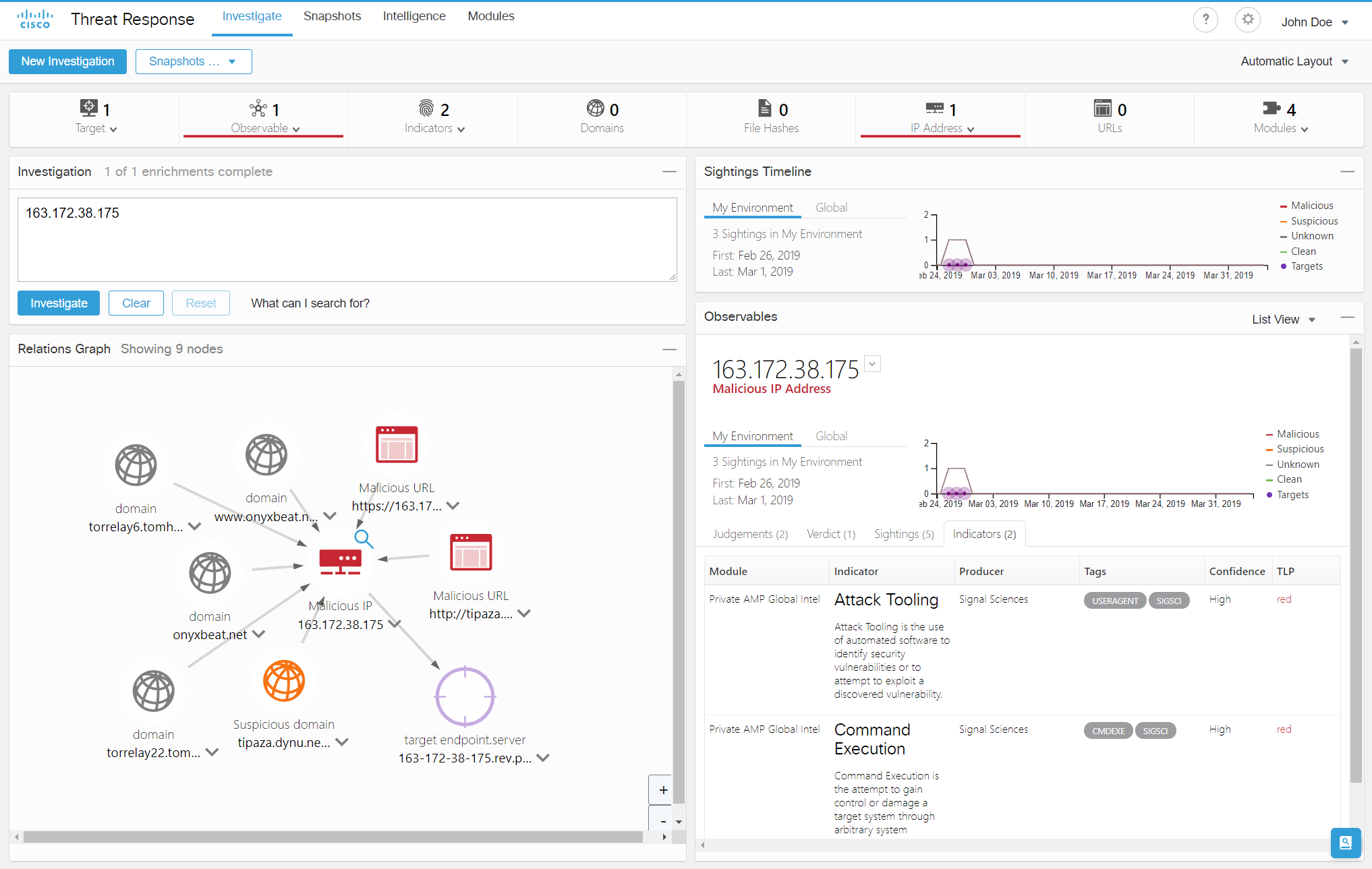
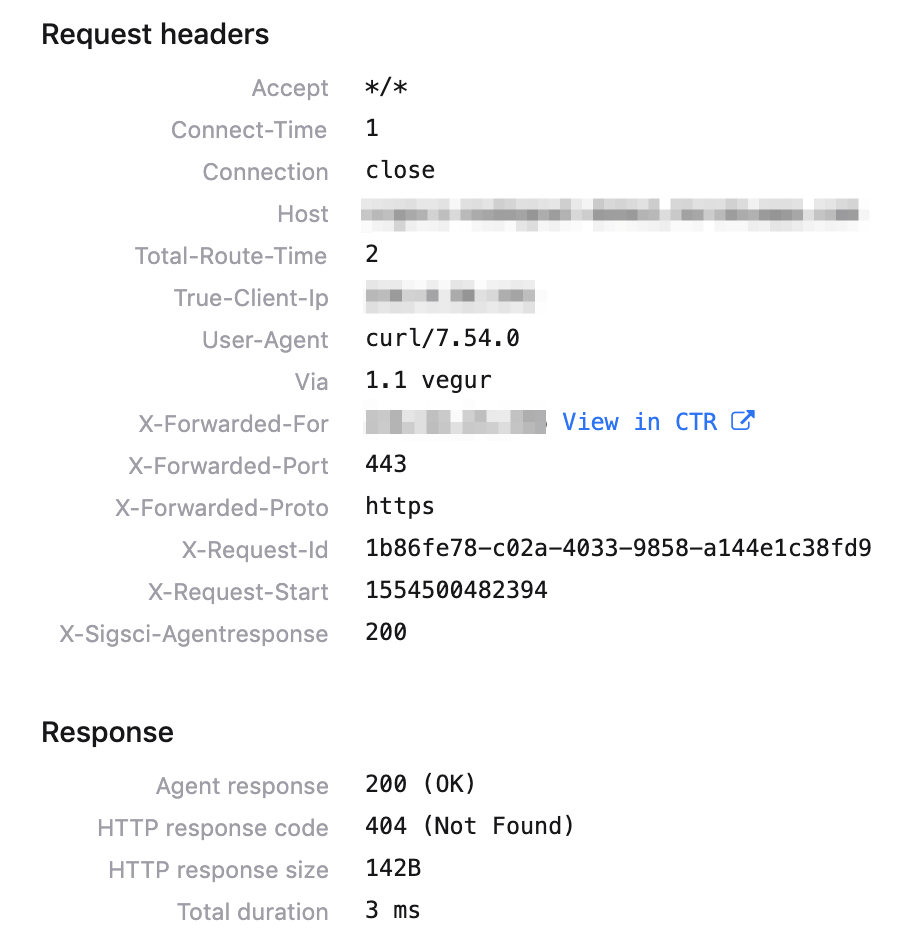
Additionally, when looking at suspicious or blocked requests within Signal Sciences, the incident responder can pivot directly into Threat Response and look up any observables related to the attacker’s source IP address.
Businesses constantly innovate and find new ways to attract, engage, and transact with their customers through web and mobile applications. As a result, a dramatic shift has occurred in how applications are developed and deployed. Now more than ever, security teams need a solution that can protect modern application workloads and provide actionable insights to the professionals responsible for investigating and responding to threats. Cisco Threat Response combined with Signal Sciences next-gen WAF redefines expectations for addressing this challenge.
Signal Sciences is now part of the Cisco Security Technical Alliance.
You can request a demo of Signal Sciences here.
Acknowledgments: Thank you to Michael Auger of Cisco Security and Brendon Macaraeg & Tom Chang of Signal Sciences for their contributions to this blog.
Want to keep up to date on Cisco Threat Response? Now you can! Subscribe here to receive alerts every time a new blog is posted.






This is great work Jessica – the integration highlights the value of importing events into the private CTIA and the flexibility and power of the API. Really great work by you and Michael!
Thanks Martin,
We are diligently working to expand the ecosystem, by having an open architecture: https://developer.cisco.com/threat-response
Best,
Jessica