Organizations face a critical challenge today: attackers are exploiting the weakest links in their networks, such as unsecured users, devices, and workloads. This threat landscape is complicated by the shift from traditional data centers to a distributed environment, where protecting dispersed data across multiple touchpoints becomes complex.
To address these threats, many organizations resort to using multiple security tools, leading to siloed teams, tech stacks, and management systems that hinder effective security. This fragmented approach results in unnecessary costs, longer deployment times, inconsistent security, and critical gaps.
Security products that do not integrate or benefit from each other exacerbate these issues. For example, Network Security Admins struggle to navigate disparate teams and tools for effective policy deployment. Additionally, customers often under-utilize security tools, resulting in poor security hygiene and misconfigurations that increase the risk of a breach. Manual monitoring of multiple tools makes it impossible for organizations to proactively predict issues that lead to operational challenges. Consequently, the burden has been pushed onto the customer to understand the gaps and figure out how to best use the tools.
Inconsistent security policies, siloed management, lack of unified visibility, misconfiguration risks, and cybersecurity skills shortage are all significant challenges organizations face. While organizations are facing these challenges, the urgency is underscored by findings from the IBM X-Force Threat Intelligence report. According to the report, the average time from initial access to ransomware deployment has dropped from 1637 hours (about 2 months 1 week) to just 92 hours (less than 4 days) in 2023. This dramatic reduction means organizations now have much less time to respond to threats, making effective and integrated security solutions more critical than ever.
Without a centralized platform, gaining a holistic view of security is challenging. Manual identification of misconfigurations is error-prone and can lead to breaches. There is a lack of skills, time, and resources to fully utilize security features and maximize ROI. Customers must implement best practices, requiring specialized knowledge and time. Resolving access or policy issues is lengthy due to diverse security products. Admins spend excessive time crafting similar policies across different platforms. Operational issues are often addressed reactively, leading to downtime and suboptimal performance. Non-actionable alerts and overwhelming data cause analysis paralysis and hinder decision-making, with a missing sense of urgency. While we will never fully move away from having distributed enforcement points, there is a significant opportunity for the security industry to provide consistent security across these varied touchpoints.
A unified security platform aims to alleviate these issues by providing a comprehensive view of the security landscape, enabling consistent policy enforcement, simplifying troubleshooting, and offering actionable insights with the help of AI. Thus, it reduces the cognitive load and dependency on specialized skills. When considering Unified Security Management (USM), the goal is to have seamless management experience.
To meet the unique needs of various organizations and support diverse network firewall configurations, our strategy focuses on three core objectives: simplifying operations, enhancing security, and improving clarity. We aim to streamline security management processes, strengthen defenses with advanced Zero Trust and vulnerability protection, and offer clear, actionable insights through AI-driven intelligence. These focused efforts are designed to deliver a more intuitive, robust, and user-friendly security solution.
Customer Outcomes with Security Cloud Control

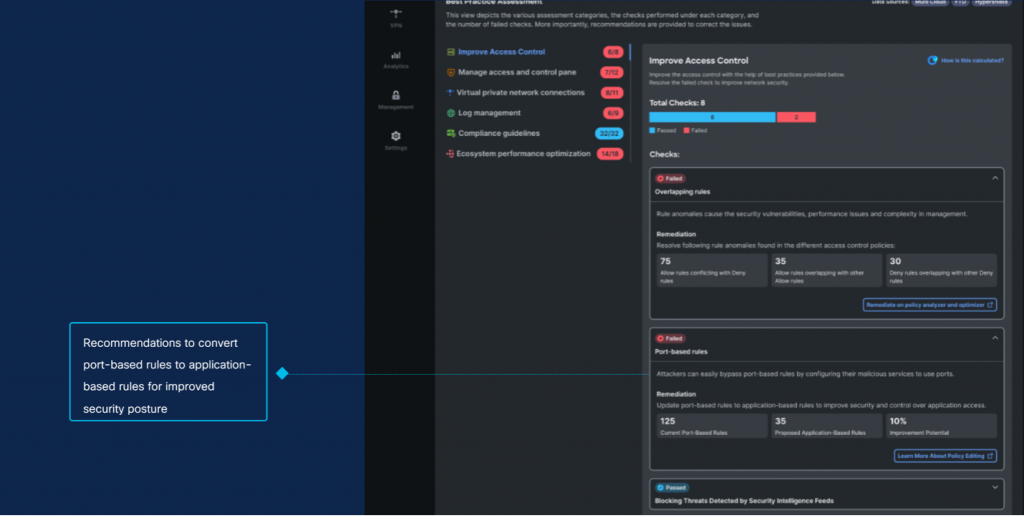
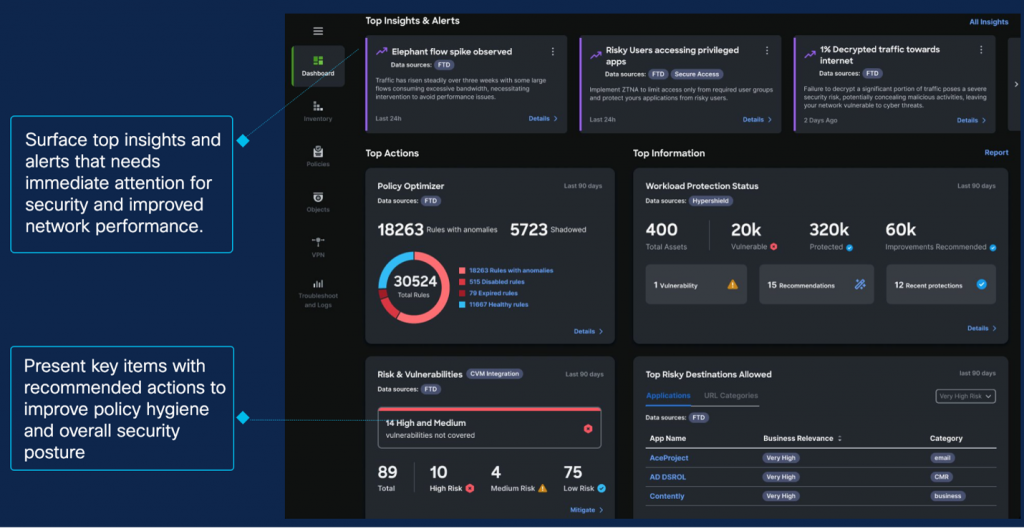
We are excited to launch AIOps, offering a game-changing way to enhance operational efficiency and bolster security. AIOps addresses critical IT challenges such as misconfigurations and traffic spikes, preventing downtime and reinforcing network performance. AIOps provides predictive insights and automation to help administrators improve security and reduce costs. We are introducing key features, such as policy analysis and optimization, best practice recommendations, traffic insights, and capacity forecasting. By incorporating AIOps into our services, we are adopting a more intelligent and proactive methodology to safeguard and optimize the performance and security of your network infrastructure.
To learn more about AIOps, check out: Managing Firewall complexity and Augmenting Effectiveness with AIOps for Cisco Firewall
Best Practice Recommendations: Nudging admins to get to better security state
Predictive Insights with AIOps
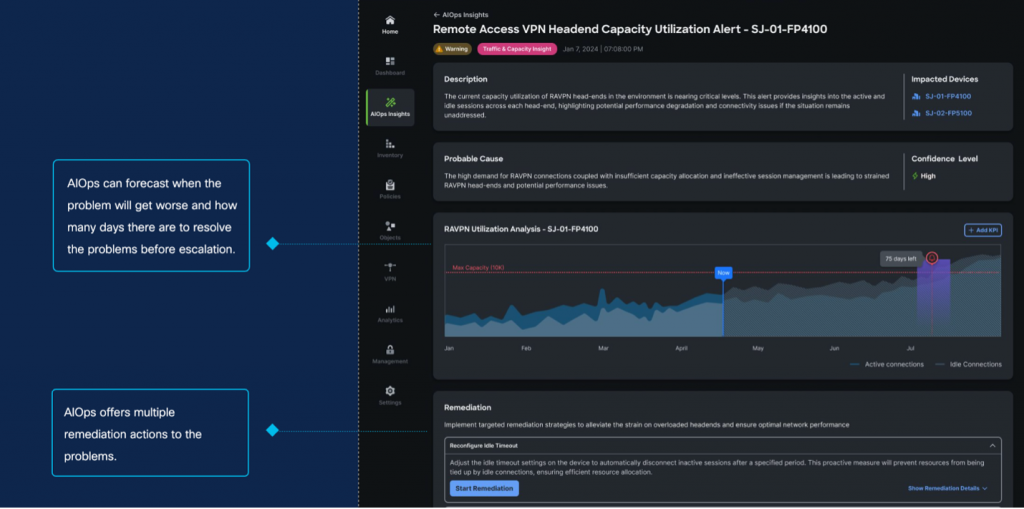
Benefits of AIOps

Our solution is designed to accommodate management of a wide array of form factors of firewalls, ensuring comprehensive security from the ground up to the cloud. It seamlessly integrates with various deployment models, including physical and virtual firewalls (Cisco Secure Firewall Threat Defense), Multicloud Defense, Hypershield, and Adaptive Security Appliances (ASA).
This versatility simplifies the management of your security infrastructure, making it easier to maintain a robust and adaptive defense system across your entire network all from a single place.
Our partnership with Splunk represents a significant leap forward in streamlining security operations. By integrating with Splunk, we enhance the oversight and monitoring capabilities of both cloud-based and on-site firewalls. Utilizing Splunk’s powerful data processing, analytics, and real-time logging strengths, we deliver an enriched, responsive, and comprehensive view of your security posture.
This collaborative effort simplifies the management of security operations, providing Security Operations Center (SOC) teams with a superior, streamlined, and more effective method for protecting their digital landscapes.
We are introducing a unified dashboard that enables our customers to gain a real-time, holistic perspective of their entire network and cloud security ecosystem. Customers can efficiently manage tens of thousands of security devices, coordinating multiple tenants under a centralized global administrator.
Unified Dashboard: A Comprehensive view of firewall and security services
We are further simplifying the operations for our admins with the Firewall AI Assistant. It revolutionizes network security by tackling the complexity of firewall rule management. With many organizations handling over a thousand rules—some outdated or conflicting—firewall maintenance becomes a security risk. Gartner notes that misconfigurations may lead to 99% of firewall breaches through 2023, highlighting the need for this AI-driven simplification. Customers can ask the Assistant to explain the intent of the policies and assist with creating rule.
AI Assistant for Firewall: Rule Analysis
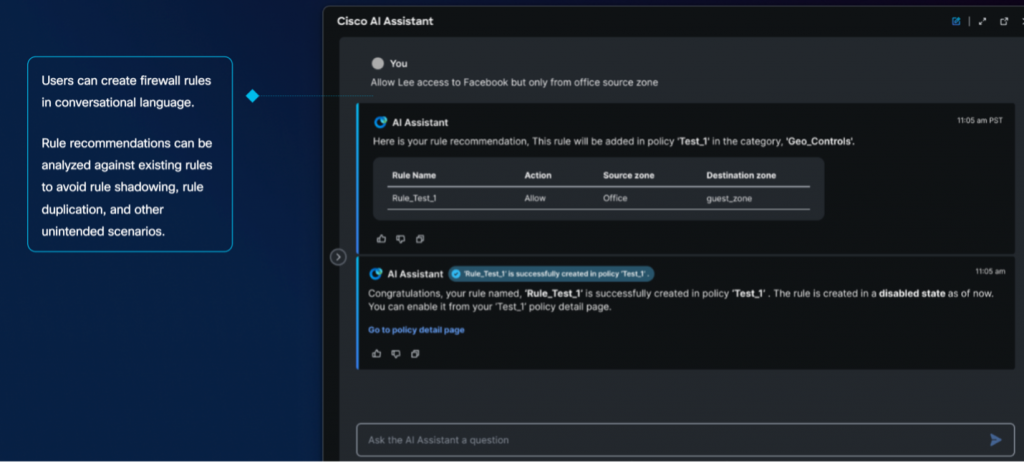
AI Assistant for Firewall: Rule Creation

A key breakthrough in our security strategy is the implementation of seamless object sharing, which plays a pivotal role in maintaining consistent protection across hybrid networks. This feature facilitates the distribution of network objects across both on-premises firewalls and multi-cloud defenses. Its primary objective is safeguarding application and workload data wherever they reside, by enabling our admins to build a consistent policy across different environments. This approach fortifies the security posture of your hybrid environment, and streamlines change management processes, reduce opportunity for errors, thereby, contributing to a more secure, effective, and resilient IT ecosystem.
Consistent Policy Enforcement: Sharing Network Objects across on-prem and Cloud environments

We are committed to continuously enhancing our services and expanding our global footprint to better serve our customers. In conclusion, our vision extends beyond merely supplying tools—we strive to revolutionize the user experience.
Through the fusion of cutting-edge technology and intuitive design, our goal is to foster a supportive environment for administrators, where operations are efficient, and security is strong. We are dedicated to alleviating the customer’s burden by offering a Unified Security Platform that empowers them to achieve the best state of security.
Stay secure!
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels





