Co-authored by Emily Skahill
“May the odds be ever in your favor…”
It was the irony of this pithy statement that sent the Hunger Games heroine, Katniss Everdeen, to an almost certain death. A dramatic reminder that we should never take “the odds” for granted. Against the backdrop of attacks like Wannacry and NotPetya, a quick survey of the cybercrime landscape will show you that when it comes to your business, leaving security to chance is not an option. And yet, despite concerted attempts to enhance network security, that task remains quite a challenge.
Indeed, picture this: it’s a rainy day, and you’ve been tasked with collecting all the raindrops that fall from the sky. Impossible, right? But for an incident response analyst, that’s essentially the task. With the proliferation of security threats over the past several years, there simply aren’t enough skilled security professionals to manually address the ever-increasing load of threats. And with the rapid deployment of IoT devices and increasing use of cloud services, finite salary budgets and personnel resources will be stretched even thinner as adversaries exploit numerous attack vectors. In fact, a 2017 SANS Institute survey reveals that triage is a substantially or completely manual task for 69% of security operation centers—and as such, the majority of SOCS are calling for greater automation across their prevention, detection, and response tools.
The bottom line? Incident response is too manual and breaches take too long to discover.
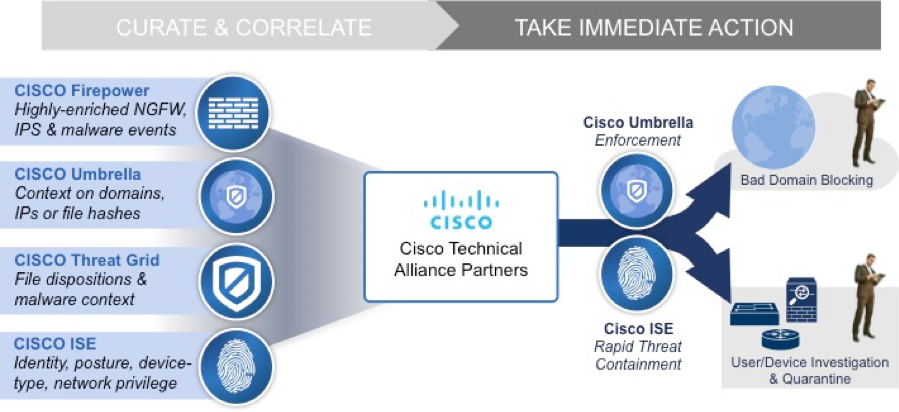
But the age of automation is here. Cisco products deliver network security automation to ensure that the odds are in your favor. Through multi-platform integration and automation, Cisco empowers security professionals to effectively and efficiently investigate and mitigate threats across multiple security technologies, from endpoint to network and across on-prem and cloud infrastructures. By unlocking the power of the Cisco product suite, you enhance the value of all your security investments with unparalleled, closed-loop automation for event curation, analysis, and action. Here’s how…
Automatically Mitigate Threats
On average, SOCs receive nearly 17,000 malware alerts each week, of which only four percent are investigated. More alarmingly, the average time to detection (TTD) of an advanced threat is 170 days. And once investigated, undertaking threat response complicates the situation further.
Cisco Rapid Threat Containment turns this daunting task of threat investigation and mitigation into an efficient channel for threat assessment and containment. Rather than piecing together information from disparate systems, IR analysts can leverage Rapid Threat Containment – which integrates your organization’s security intelligence and response technologies – to identify and contain threats on your enterprise network. More specifically, Rapid Threat Containment utilizes Platform Exchange Grid (pxGrid) to view and share data from all your security technologies across multiple vendors. Having relevant contextual data organized on a single screen allows you to conduct investigations more efficiently. When it comes time to take action on these threats, your threat response can be automated through Identity Services Engine (ISE), which directs the network to set access privileges for users and devices. For example, ISE can reduce the level of network access given to a user/device, or route their traffic through additional security investigation measures, such as packet capture or deeper inspection. Using this real-time network policy capability, integrated vendor-partner technologies on pxGrid can instruct ISE to take actions directly from the vendors’ consoles, thereby making any console a point of threat response or investigation. Thus, Cisco Rapid Threat Containment offers powerful tools to improve threat visibility and expedite detection and mitigation. That way, your business can leverage automation to execute response actions for those threats, bringing new value to your security investments.
But if you consider the extensive use of off-premise cloud applications, you’ll find that it’s insufficient to rely solely on perimeter security, because you won’t have the reach to protect those off-network users. That’s where Cisco Umbrella comes in.
Cisco Umbrella is a cloud-based Secure Internet Gateway that protects users from malware, ransomware, and phishing attacks wherever they go. By processing internet activity data from the Umbrella global network of over 65 million users, Umbrella’s statistical and machine learning models can automatically discover attacker infrastructure and act preemptively to block user traffic destined for malicious domains regardless of the location, device, or user. Umbrella Intelligence leverages its predictive intelligence, in concert with Cisco Talos web reputation and other threat intelligence feeds, to categorize DNS requests as safe, malicious, or risky, and block or allow these requests accordingly. When integrated with a SIEM, user-behavior, or security orchestration platform, this type of intelligence streamlines investigations, incident response, and triage. Additionally, the Umbrella Enforcement API is purpose-built to receive malicious domains from partner platforms in order to block them globally through DNS. In this way, Cisco Umbrella approaches security automation from a different angle, enforcing security policies for traffic destined outside the enterprise network to the internet.
So, with Rapid Threat Containment and Umbrella, you leverage automation for comprehensive threat management. Whether you’re working to identify and contain threats on your network, or to protect users against attacks even when they’re off the network, you can be assured that the odds are in your favor.
Quality Data Goes In, Network-Wide Mitigation Comes Out
Automatically Infuse Security Data with Applicable Threat Intelligence
But automation can be leveraged to do more than mitigate threats. At Cisco, we also use automation to apply threat intelligence to your security data to identify the real attacks among your benign alerts.
Cisco Threat Intelligence Director (CTID) is a capability within Cisco’s Firepower Management Center (FMC) that enables you to enhance your threat management and perimeter security by automatically tagging Firepower event data with relevant threat intelligence. CTID uses third-party threat feeds from partners like AlienVault, Anomaly, EclecticIQ, Infoblox, NC4, Threat Connect, and ThreatQuotient to generate intelligence that accurately identifies indicators of compromise (IOCs). This threat intel is then appended to the associated event within FMC, saving you the effort of manually looking up the IOC in a separate console. This automation enables you to devote your energy to analyzing actual incidents rather than sifting through false alarms.
Automate Identity and Network Awareness through Integrations
Still looking for ways to use automation to its full potential? Through Cisco’s integrations with ecosystem partners, you can also automate network and identity awareness across your security infrastructure.
Think about it this way: in the board game Clue, the object is to ascertain the identity, weapon, and location of the perpetrator. If each Clue player is like a separate security platform, possessing its own, disparate set of clue cards, it’s tricky to deduce the who-what-where-how of the incident itself. Cisco ISE integrates with security technologies of all sorts—SIEM, firewall, threat defense, vulnerability management, identity & access management, IOT and more—to provide IR analysts with ‘all the cards’ to develop a more complete picture of the threat landscape. These security platforms are able to engage in security analytics and event investigation more effectively by integrating the identity, device and network awareness they gather from ISE into their workflows.
Security Automation – You’re Using it Today
Cisco has a deep range of capabilities in security automation, many of which you’re probably already using today. By embracing the Cisco technologies that allow you to automate event curation, analysis, and action, your job becomes vastly more efficient and effective while ensuring that the odds are, indeed, ever in your favor.





