Update 9/21: Be sure to check out Ben Greenbaum’s blog and video speedrun to see just how easy it is to add relay modules to SecureX. Click to view how he added 10 free threat intelligence modules in under 3 minutes or continue reading the blog below to learn more about how easily customizable SecureX can be.
SecureX turns one year old next month. It has been quite a journey from the first announcement at RSA Conference 2020, when there was one 3rd party integration (VirusTotal), to the release of SecureX the summer of 2020 with a large ecosystem. When SecureX was launched, we had several turnkey partner integrations into SecureX, like the Splunk add-on and QRadar extension. However, for all other SecureX threat response 3rd party modules, there was a requirement to deploy code from GitHub to a relay server (self-hosted by the user or a cloud, like AWS) so the APIs could communicate with each other and translate the threat intelligence.
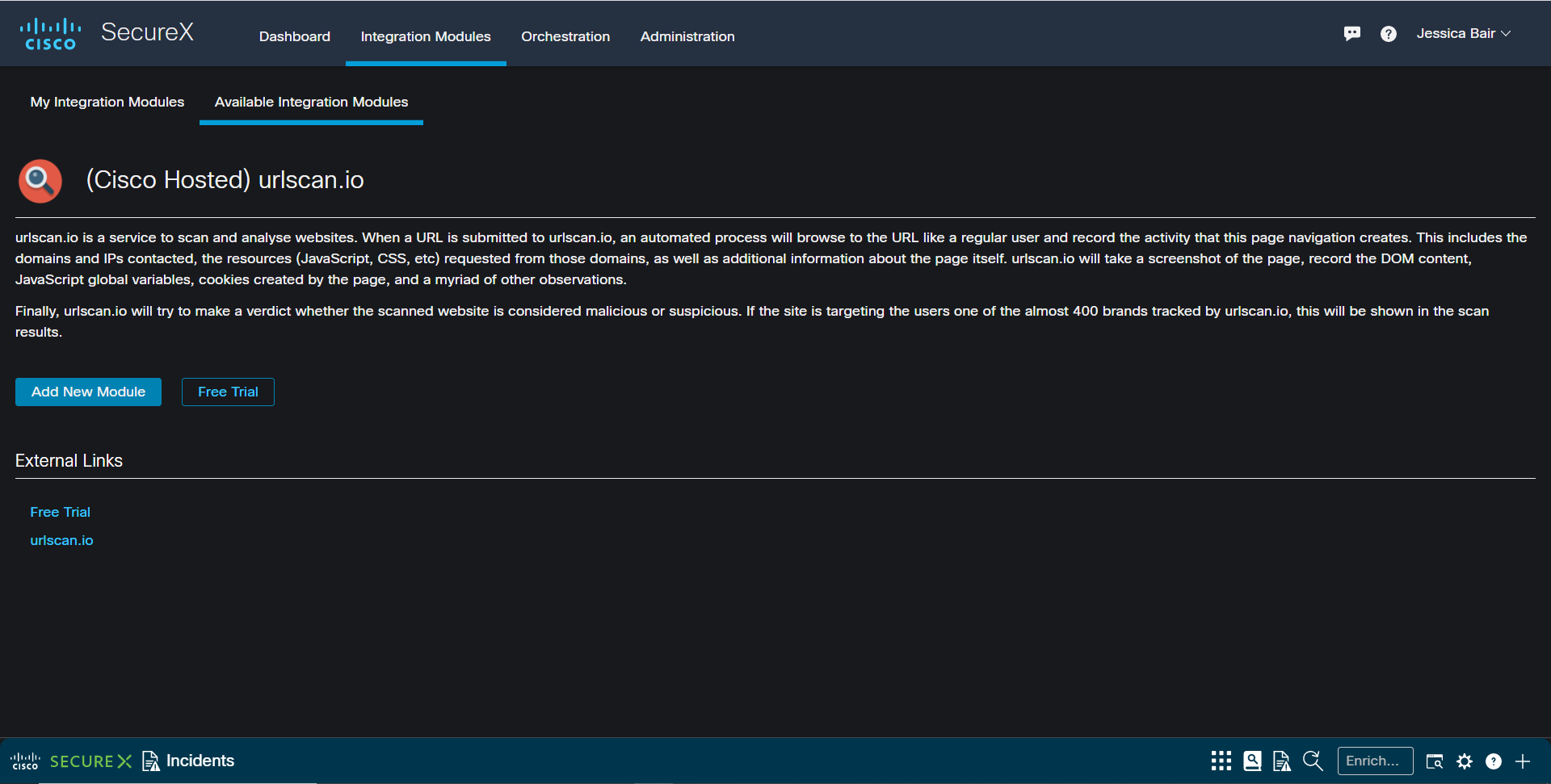
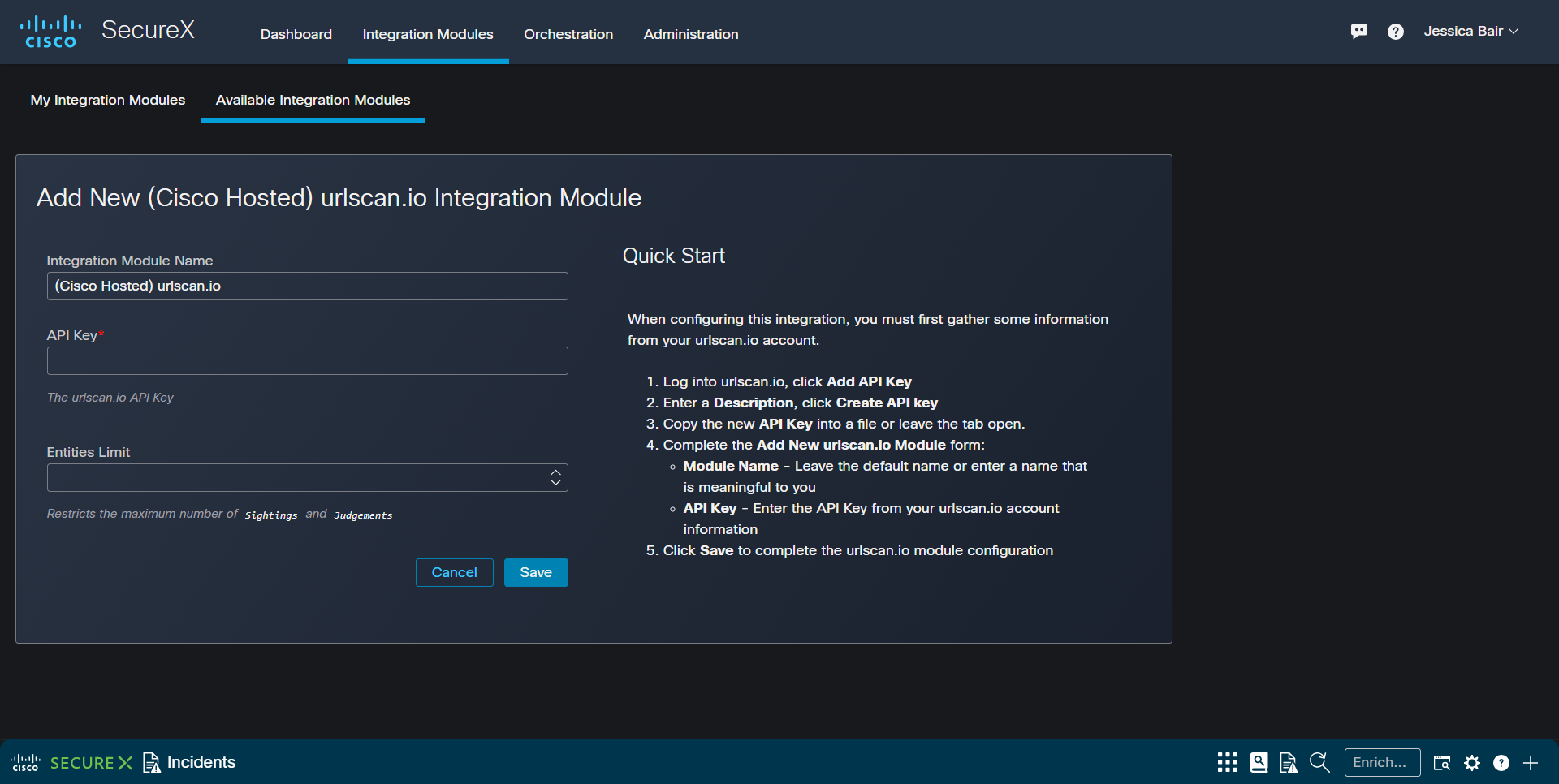
Now, all Cisco-supported integrations in SecureX are turnkey/out-of-the-box. No configuration is required, just enter your API key. For those who would like to host their own integrations, tinker/hack around some code and/or build your own integrations, we continue to post the code to GitHub for educational purposes. The training and documentation resources of DevNet remain available. Cisco Secure is committed to an open and robust ecosystem, as explored in the ESG Showcase paper.
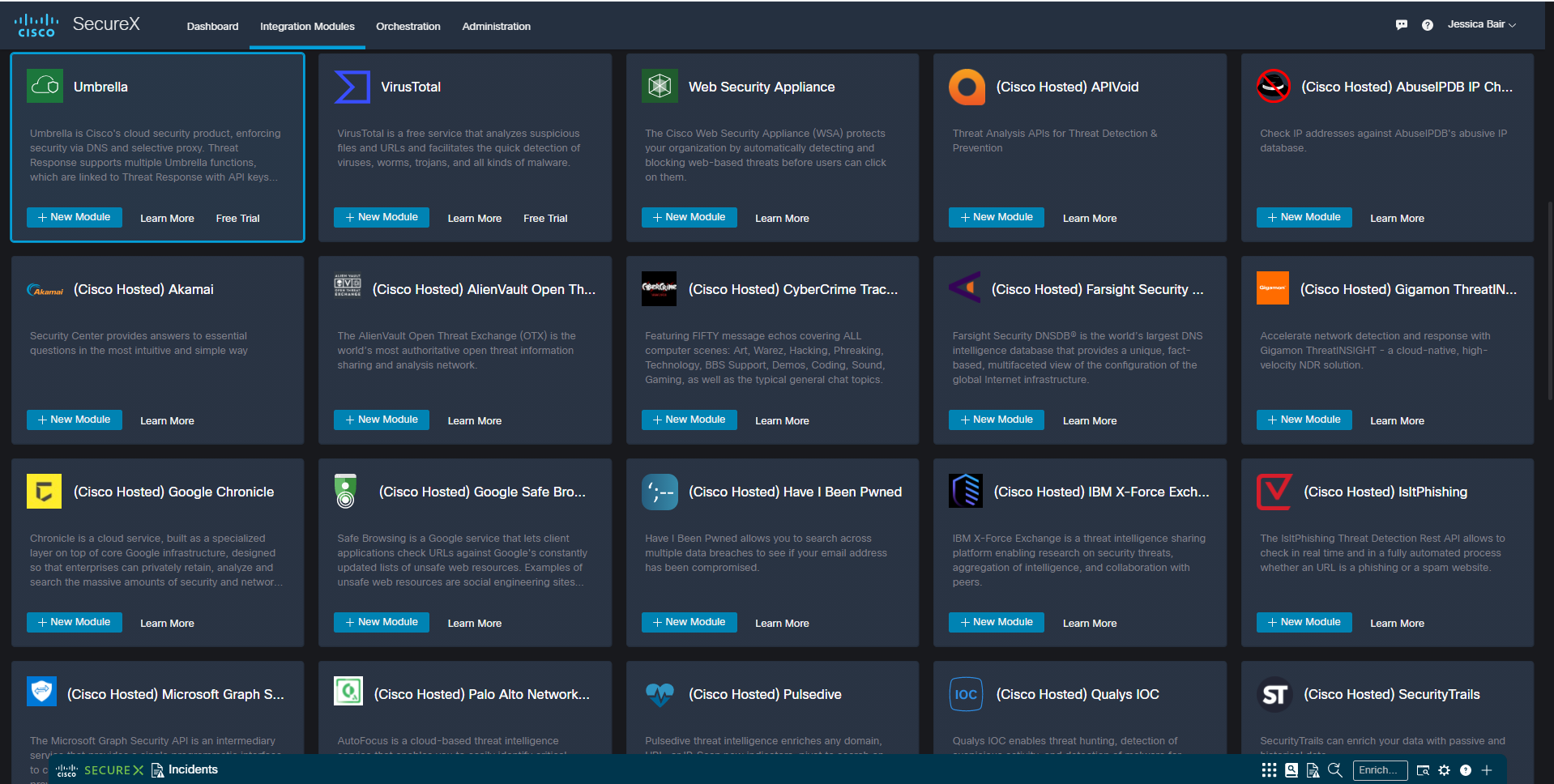
Nearly a dozen free/community security technology integrations are included, with details on how to set up your own free account.
And, then just paste in the API key and click Save.
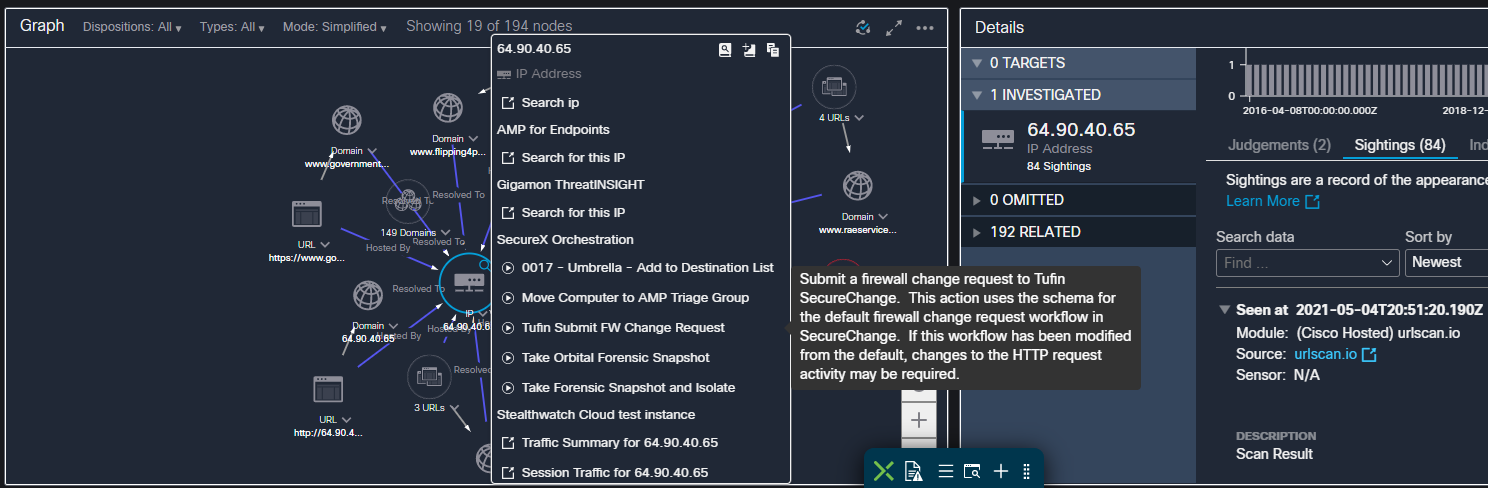
In just a few moments, you will have the new integration available to you in an investigation, with critical context visualized, such as related malicious URLs and hash values, and if your network is affected (if you have Target information from Cisco Secure Endpoint, Secure Firewall or other target sources).
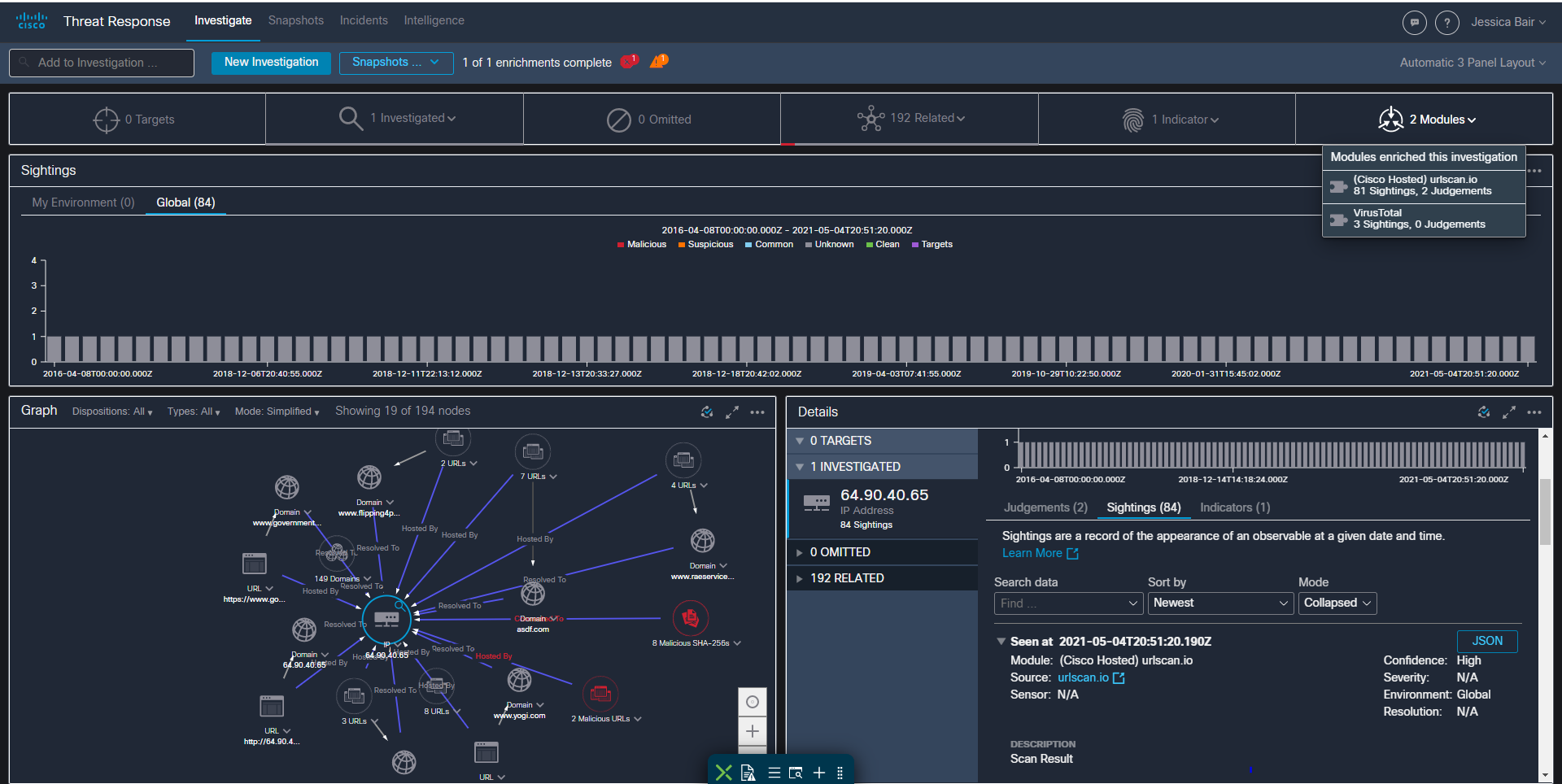
From there, you will be able to take immediate response action, such as blocking an IP address on your firewall.
In case you missed it, here are some of the latest integrations with SecureX:
Splunk CESA
 |
Cisco Endpoint Security Analytics (CESA) delivers Cisco AnyConnect endpoint data to prebuilt Splunk analytics and dashboards. This add-on enables SecureX threat response investigations to access telemetry that has been generated by the AnyConnect Network Visibility Module. Supported observable types include IPv4 addresses, IPv6 addresses, domains, file names and SHA256 file hashes. The extension for Splunk is also available for download. |
IBM X-Force Exchange
 |
IBM X-Force Exchange integration in SecureX enables an investigator to query X-Force Exchange for observables (IP, IPV6, Domain, URL, MD5, SHA1, SHA256) and return verdicts to SecureX threat response, based on the Risk Score. Be sure to view our demo video of IBM QRadar – SecureX – IBM X-Force Exchange for additional information. |
Bastille Networks
 |
Radio frequency (RF) network and device data collected by Bastille Networks are available in SecureX threat response as an integrated source. Data includes: RF Device location information RF Device packet information RF Network connectivity Data is available on a number of RF protocols including Cellular, Bluetooth, Bluetooth Low Energy, Wi-Fi, and IEEE 802.15.4 RF information can be cross-referenced back to an endpoint on your network using the SecureX Threat Response Bastille integration. |
Vade Secure IsItPhishing
 |
Vade Secure’s IsItPhishing API provides a quick way to lookup a URL to determine if it is phishing. SecureX threat response user initiates an investigation via the UI or API, and module returns Judgement and Verdict. More details are available. |
Palo Alto Networks AutoFocus
 |
SecureX threat response queries Palo Alto Networks AutoFocus for Sightings, Targets, and Judgements as well as any observable relations (such as name of SHA256, IP hosting a domain, etc.). Investigator has the ability to pivot into AutoFocus for additional context. Take a look at our GitHub page for more information. |
Cybersixgill Darkfeed
 |
Block threats and enrich endpoint protection in real-time, straight from the SecureX dashboard with Darkfeed. Powered by Cybersixgill’s unparalleled deep and dark web automated collection, SecureX users can now:
1. Automatically Enrich IOCs from Cisco Secure X (machine-to-machine) |
As the SecureX ecosystem turns one year old, look for more integrations to be released this summer. If you have a favorite security tool that is not currently integrated in SecureX, encourage them to check out the resources on DevNet and GitHub, and then drop us a note. The Cisco Secure Technical Alliance is comprised of 200+ companies / 350+ integrations, growing and open to those security companies who are working to solve problems and help build a more secure and inclusive future for all.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn






Good
Good