Some questions may never be answered: Tea or Coffee? Cricket or Baseball? Should I implement segmentation in my application environment with or without an agent? Well, if you’ve ever struggled with that last question, I have some good news for you in this blog.
If you study the segmentation products market, you will find a significant bifurcation in approach: segmentation via an agent residing within the workload (e.g., host-based firewalls) or by a device that sits in the network (e.g., network firewalls or cloud provider security groups).
Products and vendors that align to one or the other camp will argue their benefits and drawbacks, often creating a circular line of reasoning where there can never be one clear winner. The truth, I will let you in on, is that neither approach is perfect. The solution? Why not both.
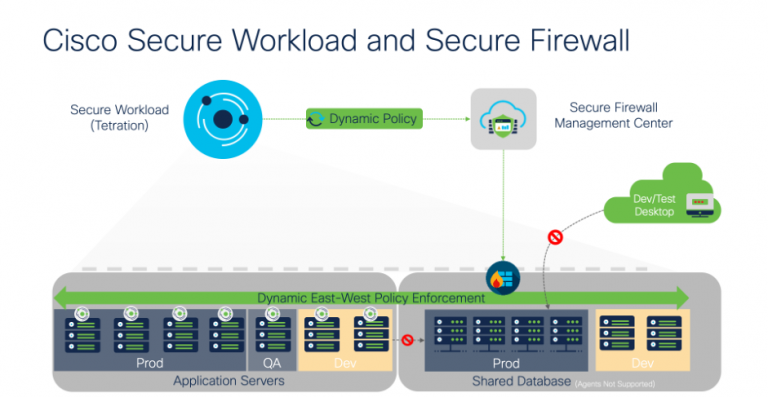
Cisco Secure Workload (agent-based) and Cisco Secure Firewall (network-based) have teamed up to create a unified segmentation layer that combines the benefits of both approaches while simultaneously reducing or removing many of the drawbacks typically associated with their standalone methods.
How is this achieved?
When we sat down to design this feature, we had two goals in mind:
1) Bring the best of the worlds together
2) Simplify the segmentation experience
To meet our goals, we consulted with many of our fantastic joint customers to understand their current issues with how they achieve segmentation in their environment, regardless of whether segmenting through agents or network devices. If we were to brings these two worlds together, how could we do it in a way that simplifies their operational burden while improving their defense in depth?
We ultimately settled on an architecture that we find to be powerful in capability yet simple to implement, operate, and troubleshoot.
The major components of the architecture are:
(1) Cisco Secure Workload (formerly Tetration)
As the “brain” of the setup, Secure Workload is where the segmentation policy is discovered through traffic analysis and integration into orchestration systems, cloud providers, and software build pipelines such as Kubernetes, AWS, and Jenkins.
Policies are simulated to ensure correctness, optimized to fit into workloads and firewalls, then pushed in parallel to hosts (through the Secure Workload agent) and the network (through Secure Firewall Management Center).
All user interaction happens here; this is the “single pane of glass” into the whole system.
(2) Firewall Management Center (FMC)
The FMC is the intermediary between Secure Workload and Secure Firewall and receives dynamic updates with the latest set of policies to enforce. The dynamic component is the key here, this enables the system to react to that natural ebb and flow of workloads in a production environment: workloads are spun up, spun down, migrated, code is deployed, rolled back, upgraded and more, all of which require constant and dynamic micro-adjustments to policies which come through as a stream of updates from Secure Workload.
(3) Firewall Threat Defense (FTD)
For the enforcement point in the network, pick any FTD flavor you like. Container, virtual, or physical, deployed on-premises or in a cloud. Choose locations in your network where it makes logical sense to apply network security controls, but don’t worry about bending over backwards to route all traffic through a firewall. It’s the best of both worlds!
(4) Workloads
The solution is targeted at the segmentation of workloads, whether in an on-premises datacenter or a cloud provider like AWS, Azure, or Oracle. We support all workload types with no limitation ranging from modern operating systems with agent support such as RedHat or Windows Server all the way through to legacy and untouchable mainframes (yes, those systems that still process many of the world’s most important transactions).
How can I get this?
Everything described in this blog is available today and at no extra charge to all Cisco Secure Workload and Cisco Secure Firewall customers. We’ve created a detailed configuration guide to help you get up and running in your environment, or if you’re just starting, check out this ThreatWise TV episode or reach out to your Cisco representative to get a live demonstration.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels





