The Cisco Product Security Incident Response Team (PSIRT) is now scoring all security advisories addressing security vulnerabilities that affect Cisco products and multivendor vulnerability alerts using the Common Vulnerability Scoring System version 3 (CVSSv3).
The stakeholders at the Forum of Incident Response and Security Teams (FIRST) have done a great job in this new version to address some of the challenges we faced with its predecessor (CVSSv2). The new enhancements allow incident response, IT security, and cyber security teams to analyze the impact of security vulnerabilities to determine the urgency of response. CVSSv3 analyzes the scope of a vulnerability and identifies the privileges an attacker needs to exploit it. The new changes introduced in CVSSv3 allow vendors, such as Cisco, to better analyze security vulnerability impact.
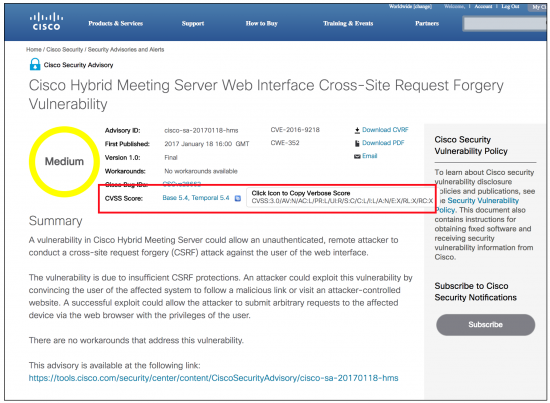
The following figure illustrates the CVSSv3 score in a Cisco Security Advisory:
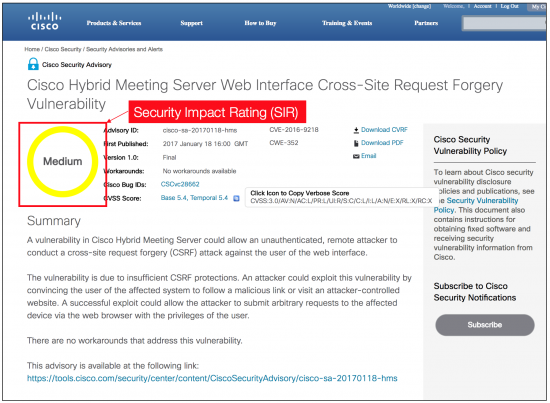
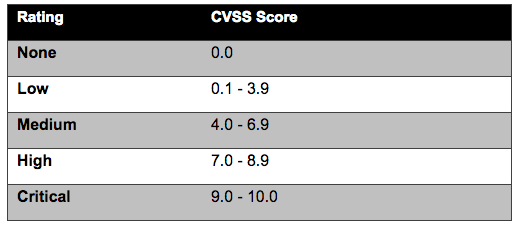
Cisco adopted a Security Impact Rating (SIR) in 2015, which uses basically the same scale as the new CVSSv3 qualitative severity rating scale. The scale is described in the following table:
The following figure highlights the SIR in the same Cisco Security Advisory:
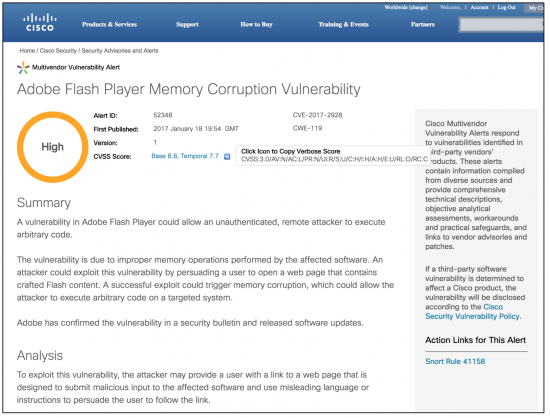
Cisco is also using CVSSv3 in all multivendor vulnerability alerts, as shown in the following figure:
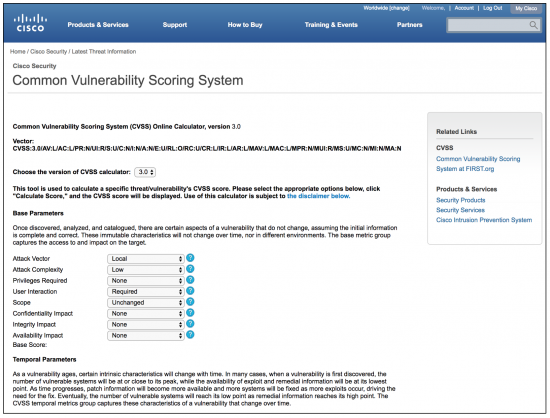
Cisco also updated its CVSS calculator to support CVSSv3, as illustrated by the following figure:
Cisco PSIRT will continue to adapt to enable our customers to quickly assess and mitigate any risks in their networks. To learn about Cisco security vulnerability disclosure policies and publications, see the Security Vulnerability Policy. This document also contains instructions for obtaining fixed software and receiving security vulnerability information from Cisco.