On June 6, 2013, malwaretracker.com released an analysis of Microsoft Office-based malware that was exploiting a previously unknown vulnerability that was patched by MS12-060. The samples provided were alleged to be targeting Tibetan and Chinese Pro-Democracy Activists. On June 7, 2013, Rapid7 released an analysis of malware dubbed ‘KeyBoy,’ also exploiting unknown vulnerabilities in Microsoft Office, similarly patched by MS12-060, but allegedly targeting interests in Vietnam and India. The indicators of compromise (IoCs) listed by Rapid7 match some of the indicators of compromise listed previously by malwaretracker.com.
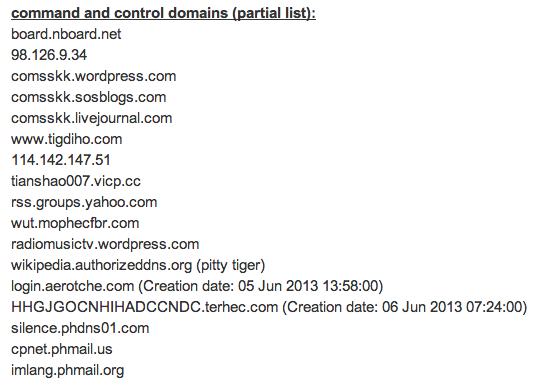
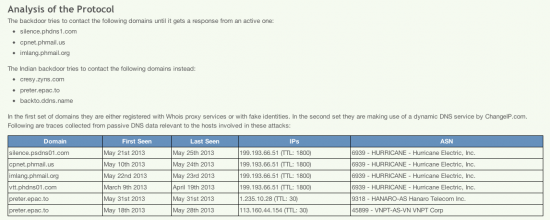
As we have seen in some previous targeted malware attacks, the attackers in this incident are taking advantage of services like changeip.com to establish free subdomains in their infrastructure. While TRAC is sure that many subdomains used at changeip.com have no malicious purpose, there is no denying the fact that attackers mounting targeted attacks are also attracted to these ‘free’ services. Blending in with legitimate traffic is a common tactic used by attackers to help fly under the radar. Not many professional organizations have valid reasons to allow traffic to domains offered by changeip.com, so blacklisting these domains is an option.
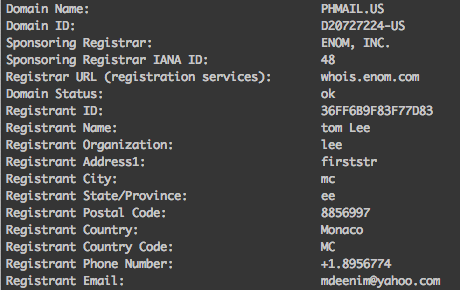
One of the second-level domains listed as an IoC is phmail.us. Subdomains at phmail.us have been linked to malicious activity dating back as far as December 2011. Based on the patterns of subdomain registration over time in DNS, TRAC believes this is an example where the attackers registered their own second-level domain. The WHOIS data, including the address, postal code and telephone number, is obviously forged.
An eclectic group of subdomains has been used at phmail.us, including the following:
cpnet.phmail.us
dnd.phmail.us
hoasen.phmail.us
inquirer.phmail.us
phattai.phmail.us
rfa.phmail.us
sscdtt.phmail.us
ttbc.phmail.us
www.phmail.us
yah00.phmail.us
yl.phmail.us
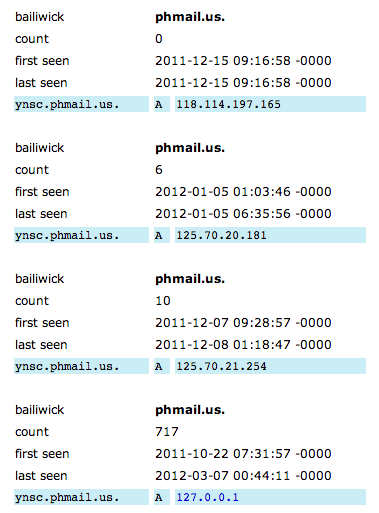
ynsc.phmail.us
While watching some of these domains using passive DNS a peculiar pattern emerges. For a long period of time, many of the DNS responses for a hostname will return 127.0.0.1, but every so often, presumably when a likely target is on-the-hook, the domain name servers return a routable IP. Perhaps this is a tactic designed to evade or postpone eventual detection and assist in staying below the radar. Note in the following graphic the DNS server replied 717 times with 127.0.0.1; however during that same time, the real routable IPs were also offered to certain requesters.
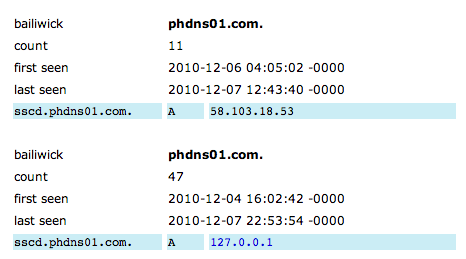
Another IoC second-level domain from this group (phdns01.com) exhibits exactly the same WHOIS and passive DNS patterns:
silence.phdns01.com
symantec.phdns01.com
www.phdns01.com
hanoihcm.phdns01.com
sscd.phdns01.com
TRAC recommends analyzing DNS traffic for these IoCs on your own networks. In this case, maintaining the latest patches would also have thwarted the attacks, and is always an excellent idea. Additionally, blacklisting the domains offered by changeip.com using local RPZs, firewalls, Cisco IronPort Web Security Appliance (WSA), or Cloud Web Security (CWS) are additional options that can help add an extra level of security.
Thanks to Craig Williams and Emmanuel Tacheau for their assistance in co-writing this blog post.






Hello Jaeson,
I like the analysis and the value of pDNS – however something still puzzles me in your analysis.
Looking at
http://blogs.cisco.com/wp-content/uploads/Screen-Shot-2013-06-12-at-3.43.54-PM.png . If the malware originators were using changeip.com for roaming IP address, what is shown in screenshot seems more like time based sensing gap. Changeip.com does not provide you location/based or source based answers. It looks like it is most likely the gaps in sensing time based (2011-10-22 to 2012-0307 blanket time that did not captured the shorter time period in which ynsc.phmail.us was actually providing answers for those 3 valid routable IP addresses).
You have more context with the name servers during that time and various other factors which I am missing. Your response will surely be enlightening.
Vijay
Hi Vijay,
Thanks for your question. Please allow me to clarify. The IoCs from these attacks included domains from both changeip.com and domains we believe the attackers registered themselves.
In this particular case the domain names zyns.com, ddns.name, and epac.to are all domains available for free third-level subdomain registration by changeip.com. They are listed as IoCs in the analysis by Rapid7. A full list of the second-level domains available at changeip.com can be found here: http://www.changeip.com/freedomains.asp
The phmail.us and phdns01.com domains were different because these domains were both registered back in 2009 using similar fraudulent WHOIS registration data. We believe the attackers registered and controlled these domains themselves, and this makes the patterns we see in the passive DNS data both relevant and interesting. The pattern of the DNS server returning 127.0.0.1 much of the time and only returning routable IPs for small durations was consistent with other subdomains we investigated as well.
Hope this helps,
Jaeson
Got it Jaeson.
For those registered domain,
It seems to me like they are using short window periods to update their A records and then reverting back to a 127.0.0.1 for their nefarious delivery system. Basically making it impossible to find these hosts unless one where sensing DNS infrastructure used by the victim/target.
Good work and thanks for the explanation!
Vijay