Effective Security requires three essential pillars: Simple to use, Open architecture and Automated workflows. The collaboration with RSA NetWitness Packets and Cisco AMP Threat Grid, in the RSA Conference 2017 Security Operations Center, exemplified the power of a four year partnership that provides an effective solution for network forensics and malware analysis.
The SOC team placed NetWitness Packets into Continuous monitoring mode, where .exe, .dll and other potentially malicious payloads were carved out of the network stream and underwent Static analysis, Network intelligence and Community lookup; before sent to Threat Grid for additional static and dynamic malware analysis. Threat Grid provides a ‘Glovebox’ function to safely interact with samples. This was especially useful to click on pop-ups for installers, warning dialog boxes and checks for user interaction.
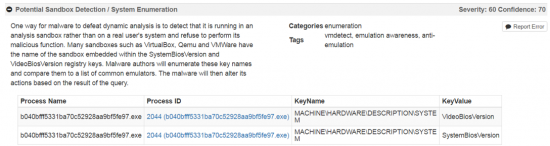
Because Threat Grid has no instrumentation or hooks into the virtual environment, there is no presence to indicate to the samples that they are in a sandbox environment, in fact checking for that is an additional behavior upon which to alert.
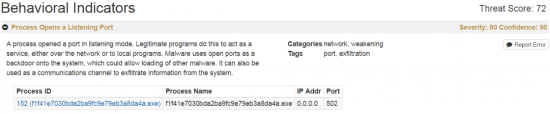
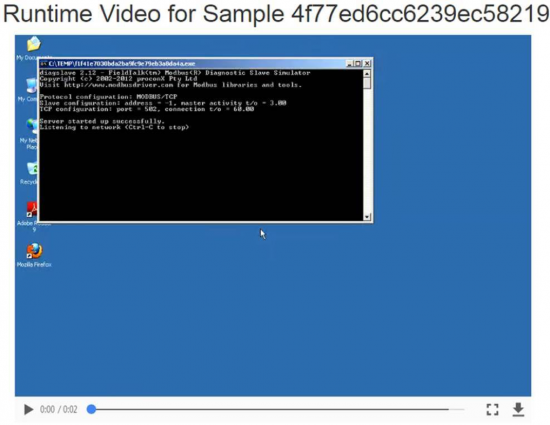
The power of behavior indicators helped identify a lot of installers being downloaded, including host based firewalls, antivirus, messaging apps; which not inherently malicious, could be out of policy in a production environment. An example was a SCADA diagnostics and monitoring app, which opened up a listening port.
Reviewing the analysis video of the sample while running provided greater context. We then traced the session in NetWitness Packets to identify the user, source and destination; confirming it was from a SCADA security vendor at the conference, setting up a demo machine.
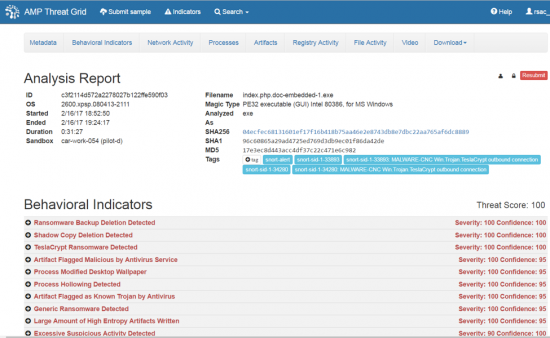
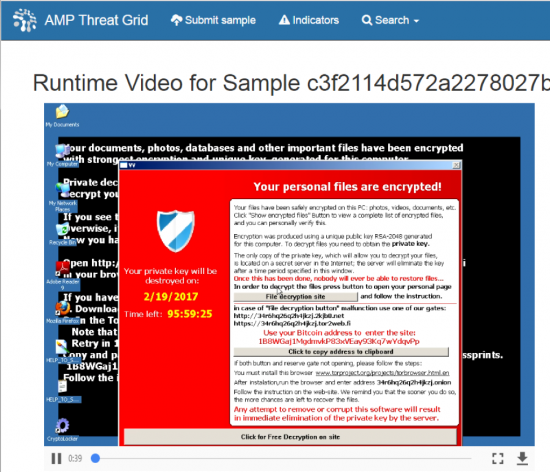
Unlike the Wild West of BlackHat, attendees in general were not using the network as an attack platform. However, very malicious samples were discovered as they were downloaded into the network, including this ransomware sample. The full PCAP of the command and control communication between the sample and the attack servers was automatically analyzed with SNORT rules as well, resulting in the SNORT alert tags.
The sample was identified as TeslaCrypt by its behavior and CnC. If it was a an unknown variant, it still would have been detected by the combination of behavioral indicators such as Shadow Copy Deletion Detected (so the user cannot recover to a system restore point), Process Modified Desktop Wallpaper (ransom note displayed) and Large Amount off High Entropy Artifacts Written (encrypting the user files on disk).
Over the course of RSAC 2017, the RSA and Cisco SOC team delivered 15 tours of the SOC, for over 600 attendees, where we showed real time traffic; plus advanced malware analysis, sandboxing and threat intelligence from Threat Grid, with time for Q&A with RSA and Cisco engineers.
Here is the Facebook Live interview from the SOC. See you at RSAC 2018!








Cisco security architecture empowers businesses and their customers!
• Inside the SOC Video: https://www.youtube.com/watch?v=M5FiUBvZNQA&sns=em
• Wrap-Up Video: https://www.youtube.com/watch?v=ULnxnzS160w&sns=em
• Destruction of the Hard Drives: https://m.facebook.com/story.php?story_fbid=1525970954082936&id=126911630655549&refsrc=http%3A%2F%2Ft.co%2FQib29CYTgW&_rdr
Well Done !
This is informative!
Thankx