Ransomware has been all over the news since 2015. You’d think we would all know how to deal with it and the fad would be dying by now. Well, that’s what I would think. It turns out that ransomware generates a lot of cash for criminals, an estimated $1 billion in 2016. It also has a low cost structure (so, very profitable) and the victim directly sends the perpetrator money.
What is ransomware?
In short, ransomware is malware that prevents you from accessing data on your PC. This either by encrypting as much of your personal data on your PC as it can find or by locking your screen. Then it issues a demand for ransom to you – give the bad guys money and they will let you access your data. Most commonly, ransomware infects your PC when you click a link in an infected e-mail. For more details, let’s go to the experts. The Cisco 2016 Midyear Cybersecurity Report and a detailed study from Talos give a good analysis of ransomware and trends and directions we can expect from crimeware operators pushing ransomware. For a nice infographic summary of the problem, check here. Cyber security specialists should read it, although I suggest everyone have a look at the executive summary at the least.
A Ponemon survey of companies who were affected by malware includes cautionary facts for those who might be thinking they will just pay the ransom and go on. Most of the companies who paid, paid over $1,000 per PC to recover their data. But only 55% of the companies that paid the ransom received the decryption keys to get their data back. The cheapest ways out of a ransomware attack are: try hard to avoid the social engineering tricks (don’t let it happen) and keep backups of data you value. Please don’t pay the ransom.
How does it spread?
Speaking broadly, the most common method of spreading ransomware is by social engineering. Social engineering works by tricking you into infecting your own computer by falling for a trick the malware author tries to play on. This is usually by e-mail, but it could be a malicious ad on a web page or a malicious web page. The trick is usually some enticement to click on an attachment or a link to a document, picture or video. Microsoft Office files, PDFs and multimedia files can all be the carriers for the ransomware program. Once you click, the ransomware finds your files on the computer and encrypts them. Then it demands a ransom if you want them back.
For more details, start with a nice, concise video looking at the anatomy of a ransomware attack. Talos will carry on from there with a detailed study of ransomware, how it spreads and provides links for what you can do about it. This discussion is best suited to an audience with some technical skills – admins, software engineers and other IT folk.
How do I know I have been infected?
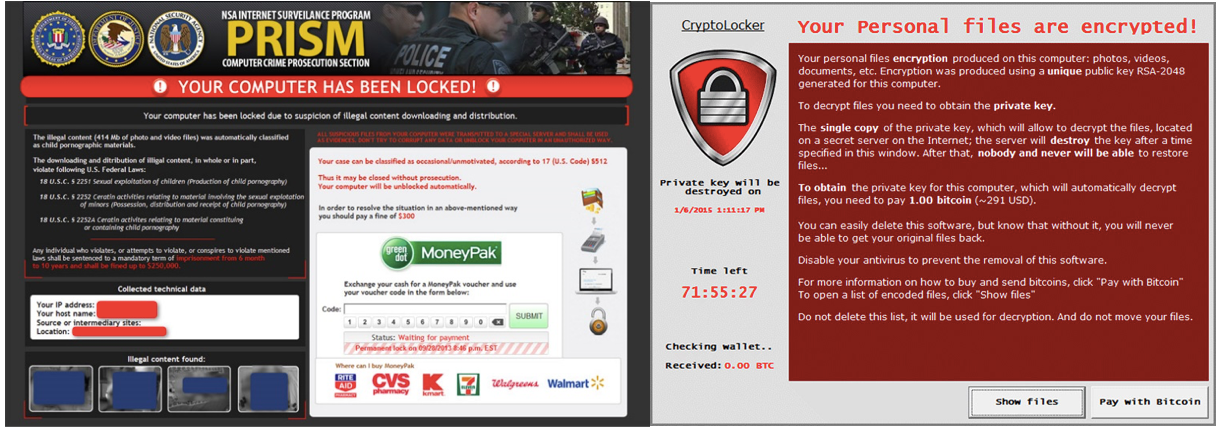
That’s easy, your screen will be taken over by something that looks like these screen images captured by Hyphenet.
When you look through the images on the Hyphenet page or do a Google images search on ransomware screenshots, you will see a lot that claim to represent action taken by a government agency. This is social engineering in an effort to create fear of government reprisal for failure to cooperate.
Best practices to NOT get infected by ransomware
Here are a couple of a great resources for businesses – This one if you are just starting a project to defend against ransomware and a useful 10 point checklist of defensive actions that will help.
What about for those of us at home? Some of the best advice for us as private individuals is as follows:
- Don’t click links or open attachments in an e-mail, unless you know who sent it. Even then, consider contacting the person to see if they really did send it.
- Be suspicious of directives to “click this patch” for Adobe, Flash and some other common tools – there is a high chance this is malware. If you want an Adobe patch, go to the adobe site and get it yourself.
- Be alert for news that there are new methods of infection. For example, malvertising may become a popular method of infection.
What can I do if I am affected?
Sometimes, no matter what you do, stuff happens and now you are wondering what a bitcoin is and how are you going to buy one so you can pay off the ransomware and have your files back.
If you really are at this point, you have three choices:
- Pay the ransom. Hey, there’s a 45% chance you’ll actually get your data back! Just kidding, please, do not fund criminals by giving them your money. All of us loose when any of us do that.
- Lose your data. Hey, there’s a 55% chance you won’t get it back even if you pay!
- Restore your system to a factory image, then restore your data from an offline backup sitting on a USB drive you keep in a drawer in your desk.
Remember I said above that even if you pay the ransom and get your system back, it may now be full of badness that will make your life miserable. The only way to avoid that is to wipe it out with a full reset to a factory image. Really, you have to do this, whether you pay the ransom or not. If you pay the ransom and get your files back, copy them to a USB drive before you reset Windows. One more piece of bad news – it is possible that your data is now contaminated with malware also. This is another reason not to pay. If you pay and actually get your files back, you could find yourself immediately held for ransom again because copies of the ransomware were left like landmines in your data. It is much better to make a backup before you get infected.
Let’s talk about backups. Maybe your employer backs up your data. Mine does. Even so, I have rolling backups of my data on USB drives that are only used for backups. I also have backups of personal data kept on my home PCs. USB drives can be bought for less than $100 from most retail outlets that offer laptops or desktops. My backup drives live in a drawer. I pull one out once a week, attach it, copy all my personal data onto that drive, then put it away. Each drive has at least three full backups.
If ransomware strikes and you have a backup, restore your system, restore your data from a backup and move on. And next time, remember not to click the link in that e-mail!
For more information on ransomware and how best to stay protected, visit cisco.com/go/ransomware.
October is Cyber Security Awareness Month, and Cisco is a Champion Sponsor of this annual campaign to help people recognize the importance of cybersecurity. For the latest resources and events, visit cisco.com/go/cybersecuritymonth.






Another lame problem: the “un-subscibe” link doesn’t always works for spam mail!
But doesn’t your browser warn you if you are about to open a file that can hold executable code? Examples of such files, I believe, are flash, pdf and the Microsoft office files. What others are there? How do you configure your browser to warn about such files?
Very much useful information. I will aware other people about it.
Thank you for your comment, Jakob.
I did some checking into Firefox and Chrome options for phishing protection. The firefox support page I looked at is here: https://support.mozilla.org/en-US/kb/how-does-phishing-and-malware-protection-work
And the chrome page is here: https://www.quora.com/How-does-Google-Chrome-protect-my-devices-from-dangerous-sites
Both use site reputation to determine whether anything you download might be harmful to you. “Site reputation” is based on statistics the browser companies gather from users like us. The browser companies track where we go and notice if bad things happen to us as a consequence of visiting a site. The site which is hurting people acquires Bad Karma (technical term, that) from the browser companies. Enough bad karma and the browser companies may label the site as malicious and start warning visitors that this site can’t be trusted and downloads should not be done.
No matter what we think of reputation-based protection, there are ways around it. For example, many legitimate sites host advertising. If you click on an ad, the host site gets paid. If the ad is corrupt (“malvertising” https://en.wikipedia.org/wiki/Malvertising ), then by clicking on the ad, you could become the victim of ransomware or other malware. In this case, the website that infected you could have a 100% golden reputation. That site serves up the malvertising ad, which itself is not hosted by the serving website, it is taken from some other website by the serving website and shown to you.
As a further level of indirection, the cybercriminal may have hacked the ad hosting site, and replaced a legitimate ad with an infected copy. Now both the ad hosting site and the ad serving site can have perfect reputations and you still end up looking at a ransomware screen. Incidentally, as people get infected, what sites start taking the reputation hits?
Best advice I have for mavertising? Don’t click the link. If you see an ad that you really want to pursue, type the relevant keywords (company name, product name, etc) into a search engine and find it that way.
Stacy