As various private organizations and high-value government bodies figure out the blast radius of the recent state-sponsored SolarWinds attack, with Cisco Endpoint Security Analytics (CESA) in your toolkit you could quickly assess your own exposure…like the CESA customer noted below.
CESA brings together the unparalleled endpoint behavioral visibility of Cisco’s AnyConnect Network Visibility Module (NVM) and the data transformation power of the Splunk analytics platform to help address the endpoint visibility gap left behind by traditional EDR/EPP solutions and network security analytics platforms.
So how does CESA accomplish this for the SolarWinds breach? Well, it’s actually in its wheelhouse.
CESA’s ability to associate what endpoint accessed what domain, as well as what software processes and protocols were used, enables immediate visibility to what endpoints are exposed—for both on-net and off-net endpoints—within minutes. How do we know? Our CESA users have told us.
Here’s an excerpt from a customer email we received:
“(IR analyst) brought up a great point today while digging out of this Solarwinds mess. We were able to connect local Windows processes to domains that were reported in the IOC lists.
With this information we could quickly understand what our endpoint exposure was for all managed hosts from their NVM logs. It also gave us a view into other domains that might have been associated with this attack, but not yet publicly published.
We likely never would have seen this data and could not explain our exposure to this severe threat. (AnyConnect) NVM logs in Splunk once again helped to save the day.”
If you want to get deep on this, below is a sample CESA Splunk query tuned for this scenario that the customer used to discover stage-2 C&C activities from SolarWinds that their malware solution missed.
CESA Splunk-query:
earliest=-365d index=anyconnect (avsvmcloud OR digitalcollege OR freescanonline OR deftsecurity OR thedoccloud OR virtualdataserver OR websitetheme OR panhardware OR zupertech.com OR highdatabase OR incomeupdate OR databasegalore) | fields *
Below is an actual sample result from this simple query showing details of an endpoint exposed:
pr=”6″ sa=”192.168.30.243″ sp=”59422″ da=”13.59.205.66″ dp=”443″ fst=”Sat May 16 19:38:31 2020″ fet=”Sat May 16 19:38:32 2020″ udid=”3AECA…<redacted>…2504C3A66″ liuid=”<REDACTED>\<redacted>” liuida=”<REDACTED>” liuidp=”<redacted>” liuat=”32770″ pa=”NT AUTHORITY\SYSTEM” paa=”NT AUTHORITY” pap=”SYSTEM” puat=”2″ pn=”SolarWinds.BusinessLayerHost.exe” ph=”A650DE5170E4A1D6EB1DADE89BDE7215A30CD4C005BEC9C3241865B40220B9D0″ ppa=”NT AUTHORITY\SYSTEM” ppuat=”2″ ppn=”services.exe” pph=”9090E0E24E14709FB09B23B98572E0E61C810189E2DE8F7156021BC81C3B1BB6″ ibc=”445″ obc=”570″ ds=”<redacted>.com” dh=”yykr55grenarianna67g.appsync-api.us-west-2.avsvmcloud.com” iid=”246″ mnl=””” mhl=”””
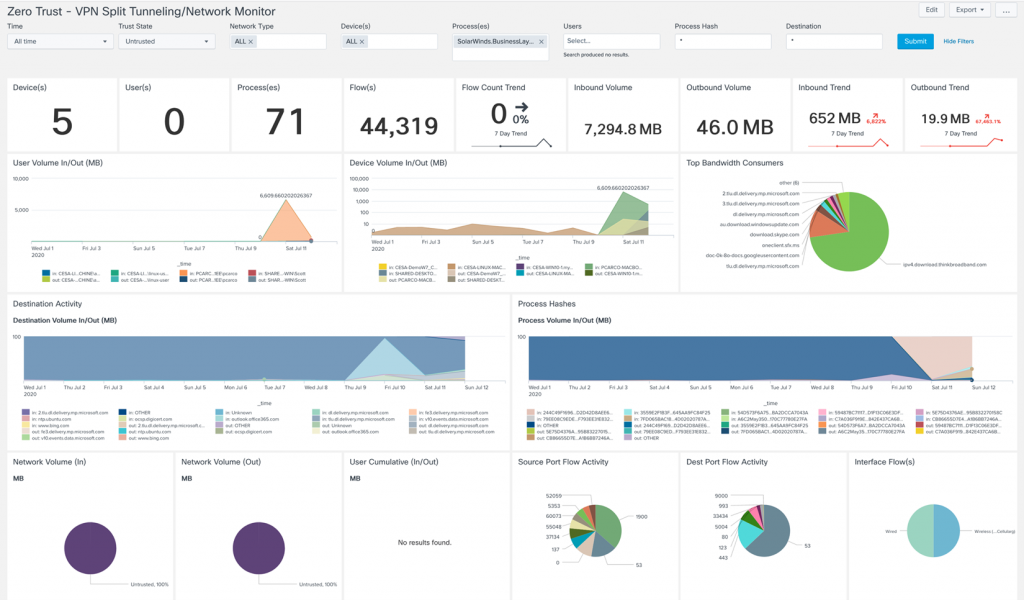
CESA dashboard example: Monitoring endpoint traffic going across split VPN tunnels
CESA closes the endpoint visibility gap for events like this one with SolarWinds. But there are many other bad things that happen in this endpoint gap. CESA addresses endpoint security visibility use cases such as:
- Unapproved applications and SaaS visibility
- Endpoint security evasion
- Attribution of user to device to application to traffic and destination
- Zero-trust monitoring
- Data loss detection
- Day-zero malware and threat hunting
- Asset inventory
In addition to the many benefits that CESA provides to close the endpoint visibility gap, Cisco Secure offers a platform approach with Cisco SecureX, a cloud-native, built-in platform experience. With the Cisco Secure platform approach, you will be able to provide greater visibility, faster response and more efficient security operations. Explore our integrated approach to find out how you can identify and contain 70% more malicious intent and risk exposure with 85% less dwell time.
Learn more about how CESA can protect your network and its endpoints.







I am curious what this decodes to: yykr55grenarianna67g.appsync-api.us-west-2.avsvmcloud.com