Effectively protecting your assets increasingly involves effective threat intelligence to better understand the types of attackers targeting your sector, and what your vulnerabilities are. Lack of any threat intelligence at all, or even the foresight to use Google and Twitter to spot fake scams trending in top results can result in a company being one of the unfortunate victims paying out to one of the copycat DDoS threats making the rounds early in 2016, or to the even more recent Ranscam encrypting malware found to not release a victim’s files after a ransom is paid.
Recent studies have shown a significant uptrend in the percent of phishing campaigns being used to deliver ransomware. The combination of being used as an entry point for credential-stealing malware, Internet links designed to steal credentials, DDoS threat messages, and ever-increasing amounts of ransomware threat, clearly makes email one of the largest attack surfaces of an enterprise.
Protecting our assets from these threats begins with our Email Security Appliance, (ESA) designed to filter based on email volume, and other heuristics associated with spam and phishing campaigns. ESA is known to be effective in blocking over 99% of spam and phish emails. That leaves enterprise defenders with less than 1% of threats to deal with, but that remaining fraction is getting increasingly effective with more well-crafted spear phishing messages. These spear fishing campaigns target users with accurate branding logos, victim names, and messages that appear to be legitimate.
Instead being content that your spam/phish appliances are blocking 99%+ of phishing threats, and continuing to blindly deal with what may slip past controls, you could be using the data from your spam/phish quarantine to help bolster your defenses. The data in the phishing messages for recipients, subjects, and message bodies could be used to learn more about what type of threats are targeting your company, how to more effectively tune controls, and maybe most importantly, to serve as a method of early warning system for potential breaches of third parties your company is doing business with.
Targeted spear phishing campaigns stay under the radar of the spam controls, often by using smaller lists of valid email addresses purchased for a target organization in a campaign. These lists can be from a variety of sources including data from previous data breaches. Protecting your organization from the remaining 1% of targeted phishing campaigns not caught by blocking appliances requires a defense-in-depth strategy such as the one outlined in this Cisco whitepaper.
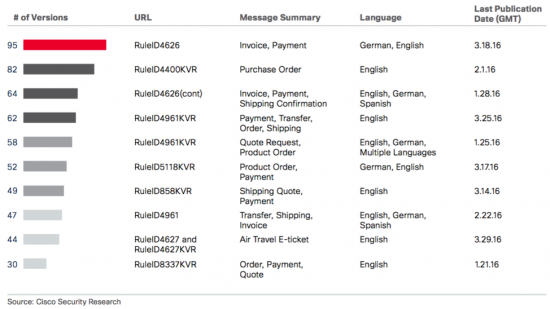
Part of a defense-in-depth strategy for your entire organization can be enriched by better understanding the threats facing you. By knowing more about the attackers’ tactics, you can better inform and prepare users, and by knowing more about who is being targeted in your firm, you can wrap further protections around them. Using spam data sets to generate metrics on the subject line and message body allowed the Cisco Midyear Security Report to show how successful emails with “invoice” themes were so far this year.
If your organization conducts phishing awareness to help employees become more secure, how much value could be added by producing metrics like these to tailor the training to stay ahead of current threats? October is National Cyber Security Awareness Month. If your organization does not have any phishing awareness training in place, you can get started in the right direction using the free online phishing awareness test by Cisco’s OpenDNS to learn about commonly identifiable tactics used by scammers.
What could your organization learn by extracting the recipient data for each phishing campaign noted by subject and message body, or payload similarity? How about if those recipients were bucketed by work group, types of access, or at an even deeper level, by what third parties they have been working with for activities such as closing sales, merger talks, and services?
If the same buckets of employees are ending up in targeted phishing campaigns fairly frequently it might be time to wrap more monitoring around those situations, examine the possibility of a third party they are working with being part of a breach where those employee email addresses could have been learned, or just as a warning that the deals they are working in are the subject of scrutiny by someone willing and able to employ phishing/malware to gain an edge.
Join the National Cyber Security Month conversation on Twitter @CiscoSecurity #CyberAware






Agree 100%. The security awareness is a priority in our Internet nowadays. Thank you for sharing this interesting blog post, with white paper, Cisco Midyear Security Report and phishing awareness test. As I tell my students and colleagues: While I teach, I’m learning, both are a Lifetime process. An every single blog post in this web site, is always teaching me the most important thing. The care, support, collaboration, of every person that share their enthusiasm, knowledge to show us the right path in a collection of the network of everything that belongs to it. Deeply appreciated.
Thank you, this information was very insightful. I am just beginning my focus on network security so your viewpoint and suggestions are very helpful.
Cisco’s technology will be a huge help in stopping these scams; but we also need to help educate our customers on how to address the human element in protecting our #privacy and #security.
To Dr. Jose A. Wong – Perez
As a professional in POS security field, what can you tell me about this POS system device? Is it accountability or not?
http://pos-il.com/
To Dr. Jose A. Wong – Perez
While I am trying to implement Cisco Midyear on this POS device
pos-nj.com/
I got a bug report like this:
“Connecting is failure”
How I can fix it?