The Cisco PSIRT openVuln API is a RESTful API that allows customers to obtain Cisco security vulnerability information in different machine-consumable formats. It supports industrywide security standards such as the Common Vulnerability Reporting Framework (CVRF), Open Vulnerability and Assessment Language (OVAL), Common Vulnerability and Exposure (CVE) identifiers, Common Weakness Enumeration (CWE), and the Common Vulnerability Scoring System (CVSS).
This API allows technical staff and programmers to build tools that help them do their job more effectively. In this case, it enables them to easily keep up with security vulnerability information specific to their network. That frees up more time for them to manage their network and deploy new capabilities in their infrastructure.
Since we launched the Cisco PSIRT openVuln API a year ago, numerous customers, partners, and Cisco employees have used it to build tools, keep up with security vulnerability information specific to their network and assess the impact of such vulnerabilities.
We have just made this API even better! The following enhancements have been introduced:
- Integration with Cisco IOS Software Checker
- Ability to query security advisories per product
- Querying using a date range
- Additional fields displayed by default in the results
Integration with Cisco IOS Software Checker
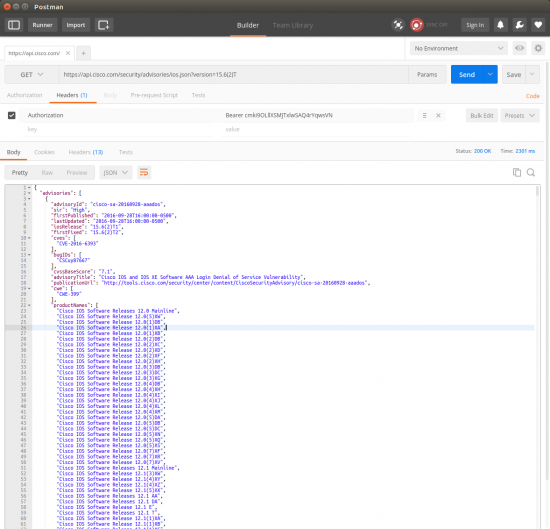
The Cisco IOS Software Checker is a tool that allows you to search security advisories that apply to a given Cisco IOS or Cisco IOS XE Software release. You can now use the Cisco PSIRT openVuln API to perform these queries. You can search for Cisco security advisories that apply to specific Cisco IOS and Cisco IOS XE Software releases and have a Security Impact Rating (SIR) of Critical or High. This feature allows you to obtain the first fixed release, as well as the details for each advisory that applies to the specific Cisco IOS and Cisco IOS XE Software release.
The following figure illustrates an API call to query all advisories that affect Cisco IOS Software version 15.6(2)T using Postman.
Querying Security Advisories Using Product Keywords
You can obtain all security advisories that affect a given product by searching using a keyword for such product name. The following is an example using the openVulnQuery python client to search security advisories using the keyword “asa”.

Querying Using a Date Range
You can query advisories (CVRF) and OVAL definitions using a “first published” or a “last updated” date range. The following example shows how to query all security advisories published from 2017-01-01 until 2017-01-24.

The following example shows how to query all security advisories published between 2017-01-01 and 2017-01-24 that had a critical security impact rating.

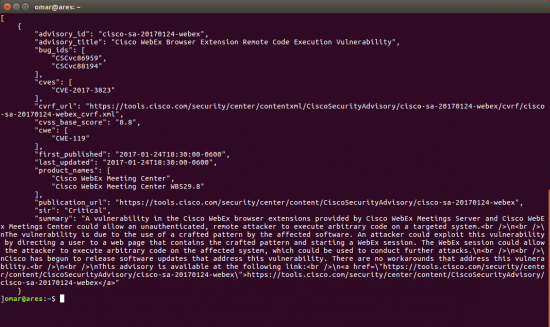
Additional Fields Displayed by Default
We have added several additional fields in the default results without the need of parsing a given CVRF file. These include:
- product names
- Cisco bug IDs
- advisory title
- publication and update dates
- CWE identifiers
- CVSS scores
- in addition to the previously existing fields (CVE, advisory IDs, SIR, publication URLs, OVAL and CVRF URLs, etc.).
The following figure shows all the fields within the results of an openVuln API call.
Technical Details and How to Access the API
You can learn how to access the openVuln API and the technical details about each feature at the Cisco PSIRT DevNet site at: http://cs.co/openvuln-get-started
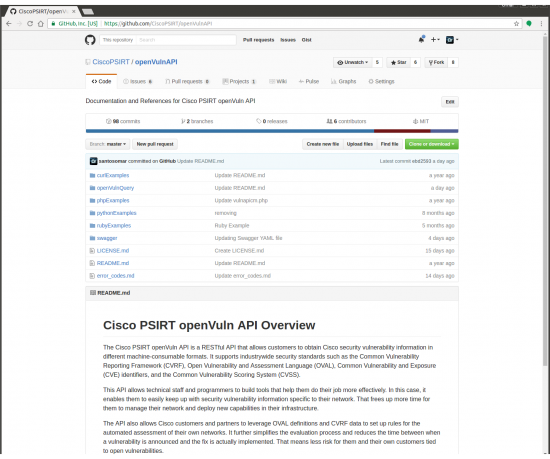
Cisco PSIRT GitHub
Check out our GitHub Repository to view example client code, additional documentation, and to download the python-based openVulnQuery client.
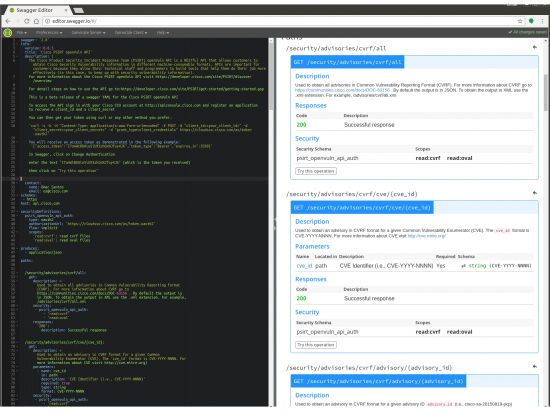
Swagger
Cisco PSIRT released a beta Swagger YAML file to help you learn, test, and integrate with the Cisco PSIRT openVuln API. Swagger is a very powerful open source framework vb for RESTful APIs that was developed by the folks at SmartBear and was contributed to the Open API Initiative (OAI).
The Open API Initiative (OAI) was created by a consortium of forward-looking industry experts who recognize the immense value of standardizing on how REST APIs are described. As an open governance structure under the Linux Foundation, the OAI is focused on creating, evolving and promoting a vendor neutral description format.
The Swagger / Open API Initiative specification provides numerous capabilities that provide interactive documentation, client SDK generation.
You can use the Swagger Editor to obtain sample code to interact with the Cisco openVuln API in numerous programming languages (including Python, Ruby, Java, etc.).
The beta YAML file can be downloaded from Cisco PSIRT’s openVuln GitHub Repository. The technical documentation and specs can be accessed at the following URL: https://github.com/OAI/OpenAPI-Specification
The following is an example of the Swagger editor.
Please feel free to engage with us at the DevNet Community or via GitHub.