Long before becoming a part of Cisco, the Sourcefire team was aggressively addressing the advanced malware challenges our customers face daily. We believe that the most effective way to address these challenges is a continuous Advanced Malware Protection (AMP) approach that does more than just track malware at a point in time, but is also unrelenting in both monitoring and applying protection. Cisco shares this vision, which is why the combination of our technologies is so powerful. It’s not just about the network, or just about the endpoint— it’s about connecting these and everything in between for complete protection.
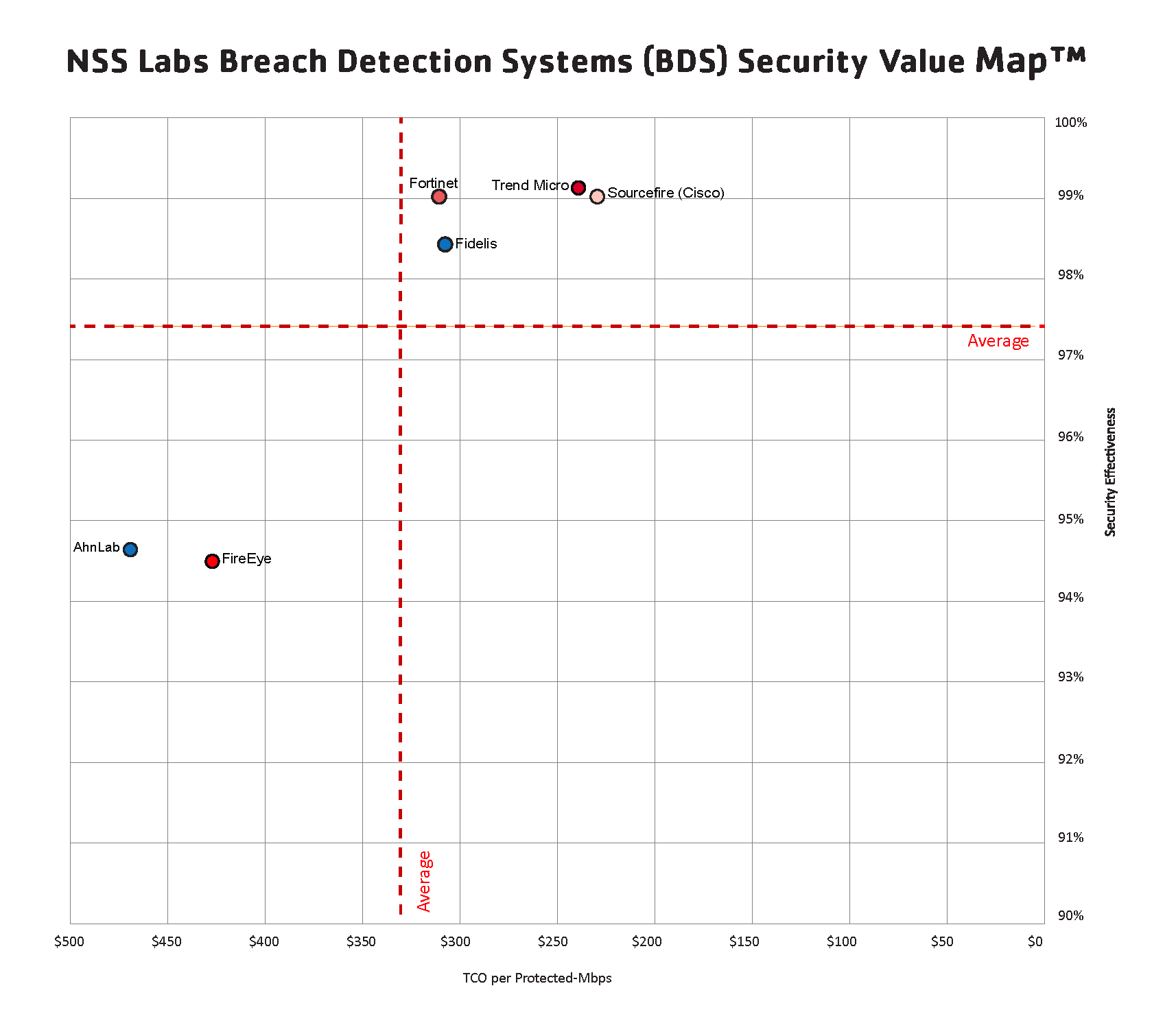
While our customers knew it and we knew it, the industry at large can now be certain that this continuous approach is the most effective for addressing advanced threats. NSS Labs tested AMP along with other security solutions for its 2014 Breach Detection System Security Value Map (SVM) and Product Analysis Report (PAR). NSS Labs defines Breach Detection Systems as solutions that provide enhanced detection of advanced malware, zero-day and targeted attacks that could bypass traditional defenses. The SVM results speak for themselves:
The SVM is a unique graphical representation of the security effectiveness and value of tested products. It’s no surprise to us that AMP scored as high as it did, but the results are great validation of our commitment to delivering this leading protection with the best total cost of ownership (TCO).
The SVM is also further proof that solutions marketed at addressing targeted advanced persistent threats (APT) and zero-day attacks can’t stop at only offering point-in-time detection. Advanced Malware Protection is the only solution to offer continuous analysis, retrospective security, and multi-source Indicators of Compromise (IoC) for protection before, during and after attacks across the extended network. These capabilities address an important gap that exists in all point-in-time products. Our AMP solution provides the continuous capability to “go back in time” and retrospectively identify and then remediate files that initially evade defenses.
Some highlights from testing:
- AMP has the lowest TCO of any product tested
- AMP is a leader in security effectiveness achieving detection of 99 percent of all tested attacks
- AMP excelled in time-to-detection, catching threats faster than competing Breach Detection Systems
When we talk about AMP with our customers, we call it “AMP Everywhere” because it can protect from the cloud to the network to the endpoint. It has been available as a connector for endpoints and mobile devices, a standalone appliance, and as part of Next-Generation Firewall and Next-Generation IPS for the last two years. It has also recently been integrated into Cisco’s portfolio of Web and Email Security Appliances and Cloud Web Security. With web and email interactions remaining one of the primary vectors for malware infection in organizations, AMP integration on our leading email appliance and web security gateways provides our customers with even stronger protection wherever a threat can manifest itself.
“AMP Everywhere” is a reality. An extremely effective one, at that. I encourage you to see the results for yourself. Download a free copy of the 2014 NSS Labs Breach Detection Systems SVM and PAR for Advanced Malware Protection.






Hi Jason,
Speciall for you – Real world vs Lab testing.
http://www.fireeye.com/blog/corporate/2014/04/real-world-vs-lab-testing-the-fireeye-response-to-nss-labs-breach-detection-systems-report.html
Hi Nikolay,
I believe Advanced Malware Protection (AMP) – (http://www.sourcefire.com/solutions/advanced-malware-protection) is a superior solution for addressing malware and advanced threats. I also believe these results are representative of the strength of AMP in doing so. There is a lot more than a sandbox looking at web and email traffic necessary to address these threats and that is apparent. Addressing the problem in an efficient, scalable, managed, cost effective way should be the goal.
Do I believe that there is a perfect solution to all problems, no. The bottom line here though is that if you can’t detect live exploitation in a lab, you can’t detect it in field either.
Hi,
1 questions need all to be ask , the below statistics have been achieved by FireEye in 2013 , so what the achievement for the other vendors ??!!! 🙂
>>>>> Found 11 exploitable zero day vulnerabilities, with two uncovered so far in 2014. (By comparison, among the top 10 cyber security companies ranked by security-related revenue, only 2 other zero-day vulnerability were reported in 2013.)
>>>>> Tracked more than 40 million callbacks.
>>>>> Tracked more than 300 separate APT campaigns.
>>>>> Deployed more than 2 million virtual machines globally.
Maybe the answer is, it is not 2013 anymore…
here is a synopsis of the other half of the story…
https://www.nsslabs.com/blog/dont-shoot-messengerMessenger
I think it’s worth including NSS Labs’ response, too. Adds a nice touch of color to the whole debate about “real world testing.”
https://www.nsslabs.com/blog/dont-shoot-messenger
Can you shed some light on what Sourcefire products NSS Labs actually tested? Did they test the FireAMP endpoint agent? Did they test the malware license for the IPS/NGFW? If they tested just the endpoint agent, how did they determine performance numbers?
Thanks,
SK
Sam the NSSLAB metodology is public. https://www.nsslabs.com/reports/categories/methodologies
Hi Enrico, I read through the methodology and our company purchased the NSS Labs reports. I’m having trouble finding what product or products were actually used for testing. The NSS Labs report states they tested “Sourcefire Advanced Malware Protection v4.5.2” According to Sourcefire’s public IPS documentation, AMP for FirePOWER is supported on IPS sensors running version v5.1 or newer. AMP v4.5.2 refers to FireAMP Cloud which is currently at v4.5.20. So my question again is, what Sourcefire product(s) did NSS Labs test? I assume it was a combination of IPS sensors and FireAMP Windows connectors. Is that correct? How else could Sourcefire participate in performance testing without a network sensor and be able to submit files to the cloud sandbox for analysis (not just file hash lookup) without FireAMP connector?