Cisco’s Advanced Services has been performing penetration tests for our customers since the acquisition of the Wheel Group in 1998. We call them Security Posture Assessments, or SPA for short, and I’ve been pen testing for just about as long. I’ll let you in on a little secret about penetration testing: it gets messy!
During our typical assessments we may analyze anywhere between 2,000 and 10,000 hosts for vulnerabilities, perform various exploitation methods such as account enumeration and password attempts, buffer/stack overflows, administrative bypasses, and others. We then have to collect and document our results within the one or two weeks we are on site and prepare a report.
How can anyone keep track of all this data, let alone work together as a team? Are you sure you really found the holy grail of customer data and adequately documented it? What if you’re writing the report but you weren’t the one who did the exploit?
 The answer is to build a data management application that works for you. The first iterations the SPA team created were a mixture of shell, awk, sed, tcl, perl, expect, python and whatever else engineers felt comfortable programming in. If you remember the Cisco Secure Scanner product (aka NetSonar) then our early tools were this with extra goodies.
The answer is to build a data management application that works for you. The first iterations the SPA team created were a mixture of shell, awk, sed, tcl, perl, expect, python and whatever else engineers felt comfortable programming in. If you remember the Cisco Secure Scanner product (aka NetSonar) then our early tools were this with extra goodies.
Welcome to the 21st Century
As time moved on our tools became unfriendly to larger data sets, inter-team interaction, and support of new data types were difficult. The number of issues detected by vulnerability scanners started to increase and while we have always been able to support very large environments, the edges were starting to bulge.
We don’t believe this scenario is unique to us. We also don’t believe current publicly available solutions really help. Most teams we’ve talked with have used a variant of issue tracking software (TRAC, Redmine) or just let Metasploit Pro handle everything.
We think this isn’t good enough which is why we are releasing our tool, Kvasir, as open source for you to analyze, integrate, update, or ignore. We like the tool a lot and we think it fills a missing key part of penetration testing. It’s not perfect but it’s grown up a lot and will improve.
What’s Kvasir?
Kvasir is a web-based application with its goal to assist “at-a-glance” penetration testing. Disparate information sources such as vulnerability scanners, exploitation frameworks, and other tools are homogenized into a unified database structure. This allows security testers to accurately view the data and make good decisions on the next attack steps.
Multiple testers can work together on the same data allowing them to share important collected information. There’s nothing worse than seeing an account name pass by and finding out your co-worker cracked it two days ago but didn’t find anything “important” so it was never fully documented.
Supported Data Sources
At current release, Kvasir directly supports the following tools:
- Rapid7 Nexpose Vulnerability Scanner
- Nmap Security Scanner
- Metasploit Pro (limited support for Express/Framework data)
- ShodanHQ
- ImmunitySec CANVAS
- THC-Hydra
- Foofus Medusa
- John The Ripper
- …and more!
There are obviously some gaps here but these are the primary tools we use. Support for scanners such as Nessus, QualysGuard, SAINT, and others are in various stages of development already, just not completed at this time.
Nexpose and Metasploit Pro Integration
Since the SPA team generally uses Rapid7’s Nexpose and Metasploit Pro Kvasir integrates the use of these tools via their API. We purposefully did not incorporate some features but may have future plans for others.
The importation of Nexpose site reports is fully automated. Just pick a site and let Kvasir generate the XML report, download, and parse it! After parsing, the scan file can be imported into a Metasploit Pro instance.
For Metasploit Pro results you must first generate an XML report but after that is done Kvasir will download and parse it automatically. Kvasir also supports the db_creds output and will automatically import pwdump and screenshots through the Metasploit Pro API.
Metasploit Pro’s automatic Bruteforce and Exploit features can be called directly from Kvasir. Simply select your list of target addresses, click a few buttons, and go take a rest! You’ve earned it!
From Vulnerability to Exploit
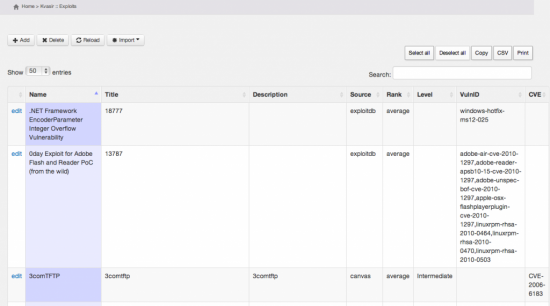
So you have a host with a list of vulnerabilities, but what is exploitable? Exploit frameworks such as Metasploit Pro and CANVAS as well as the Exploit Database archive from Offensive Security are mapped to vulnerability and CVE entries granting the user an immediate view of potential exploitation methods. CORE Impact’s list of exploits is being researched for inclusion.
Screenshots!
The initial screen of Kvasir shows two bar graphs detailing the distribution of vulnerabilities based on severity level count and host/severity count as well as additional statistical data:
A tag-cloud based on high-level severities (level 8 and above) is included which may help pinpoint the highest risk vulnerabilities. This is based solely on vulnerability count.
Kvasir’s Host Listing page displays details such as services, vulnerability counts, operating systems, assigned groups, and engineers:
Kvasir supports importing exploit data from Nexpose (Exploit Database and Metasploit) and CANVAS. Link to exploits from vulnerabilities and CVE assignments are made so you can get an immediate glance at what hosts/services have exploitable vulnerabilities:
The host detail page provides an immediate overview of valuable information such as services, vulnerability mapping, user accounts, and notes, all shared between testing engineers:
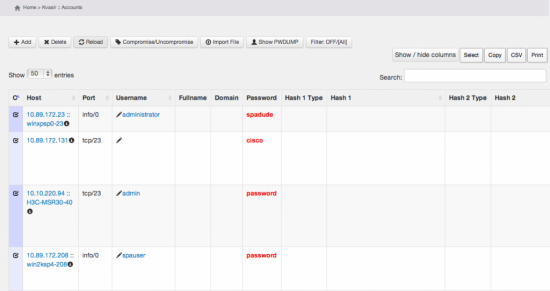
Of course as you collect user accounts and passwords it’s nice to be able to correlate them to hosts, services, hashes and hash types, and sources:
Features not shown:
- Windows Domain information management
- Evidence management (screenshots, documents, password files)
- XML and Microsoft XLSX export of data
- Detailed vulnerability, service and password statistics
- Use of Common Platform Enumeration for Operating Systems
- Vulnerability Circles (development in-progress) for a graphical view of exploitable risks
- Third-party credential management (John the Ripper .pot files, hydra and medusa output files, and other structured file imports)
- Long-running scheduler tasks
- Terminal launching for elite haxx0ring and audit trails
Show Me the Code!
The source code is available now at https://github.com/KvasirSecurity/Kvasir. Fork, Install, Review, Contribute!






I found this , as a layman, informative and useful
Nice to see the next generation of “AutoSPA” 😉
Long live AutoSPA!
Dear Kurt Grutzmacher,
thank you for putting this on GitHub, but please reconsider your “mugshot”, I am sure you are a nice guy ..
So along the same lines of Denim Groups — ThreadFix Open Source Software Vulnerability Management Tool.. just different and similar tools supported.
Exactly: https://code.google.com/p/threadfix/
It would be perhaps better if the 2 project combine time and resources to create 1 good project/tool instead of 2 projects who still have to work on supporting most of the known vulnerability scanners.
(I see that Threadfix got most of them already covered – not OpenVAS yet)
Anyhow, good news that there is a big vendor or someone of a big vendor also looking into this.
Great job Kurt! It is very cool to see the new generation of tools y’all are using.
Great work!! Good luck.
Really nice tool, not production ready as threadfix, that we already use, but nice to have a choice! We also sent you some bug reports on https://github.com/KvasirSecurity/Kvasir/issues
Francesco “ascii” Ongaro
http://www.isgroup.biz / http://www.easyaudit.org
To be honest I see ThreadFix and Kvasir working towards different overall purposes. There are things we can learn from each other, no doubt, but if you’re looking for a comprehensive Vulnerability Management tool by all means Kvasir may not be the right tool at this time.
If you want a quick and adaptive penetration data management tool, that’s what Kvasir is all about.
I look forward to seeing it in action!
hi sir.. i ;ve downloaded and configured kvasir to run … but i cannot integrate my metasploit framework … please can you release a usermanual to install !!
Thank you! I know the documentation is a bit lacking but we’re putting a lot of information in the wiki at https://github.com/KvasirSecurity/Kvasir/wiki
I will be giving a presentation at ToorCon about using Kvasir and the slides and recording will be made available.
Great job and good luck 🙂 🙂
Looks great but the installation instructions are confusing;
Different here https://github.com/KvasirSecurity/Kvasir
to here https://github.com/KvasirSecurity/Kvasir/wiki/Installation
and even on the wiki installation page they tell you to clone from https://github.com/CiscoSystems/kvasir.git Kvasir and https://github.com/KvasirSecurity/kvasir.git
So clearer instructions (or a VM) would be nice
Other than that keep up the good work and thanks for sharing
Thanks for catching the error, I’ve corrected the wiki entry.
After I shore up the Nessus support I’ll focus on a more screenshot-heavy installation wiki as well as other documentation.
Great job, thanks for the sharing of this article.
When i try to access the wiki link, it redirects me to /kvasir/default/wiki/_create/index and just shows a “401 UNAUTHORIZED” page. Do you have any suggestions on how I can this functionality working?
All wiki links open fine for me. Which specific link is broken for you? In any event the GitHub wiki’s main page for Kvasir is @ https://github.com/KvasirSecurity/Kvasir/wiki
I shouldve specified. I’m referring to having difficulties the wiki built into Kvasir, not the documentation wiki.
Very Interesting!
Great work Kurt!!!
Really nice.
I used this on a pentest recently and it’s been very useful. I have a few issues that I’d like to submit code to improve – but do you have a rough roadmap for where you are taking the tool – eg user comments?
I want to make sure I’m not coding something that you are already working on 🙂