When faced with an either/or situation, people typically prefer not to choose. We want the best of both worlds. Rarely does someone want peanut butter OR jelly. Have cake? You probably want to eat it, too.
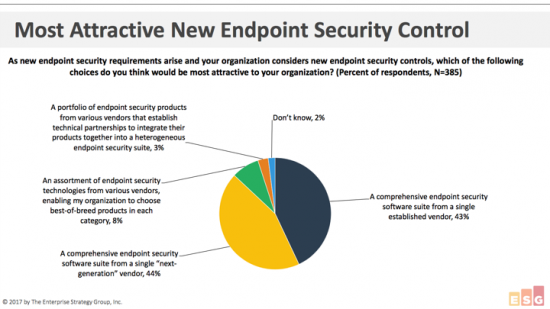
So, it’s surprising to find new research from ESG shows that while 87% of organizations want a comprehensive endpoint security software suite, 43% want that suite to come from an “established” vendor, and 44% want to purchase from a “next-generation” vendor. (Source: ESG Master Survey Results, The Evolution of Endpoint Security Controls and Suites, November 2017.)
Why should anyone have to choose between next-generation technology and working with a well-established vendor with long-lasting customer partnerships?
With Cisco, you don’t have to compromise between next-generation and established – you get both. Cisco’s AMP for Endpoints provides the advanced protection of next-generation technology, backed by an established, proven organization.
What people really want
At the end of the day, what people really want is a comprehensive endpoint security tool they can rely on to do its job effectively. They want:
- Fewer tools to manage
- Protection from advanced threats
- Automatic remediation upon discovery
- Comprehensive investigation capabilities
Solely implementing point products from niche “next-generation” vendors creates a lack of integration across your security infrastructure and an environment that’s near-impossible to manage. Many of these vendors are still seeking rounds of funding, with no guarantee you’ll be working with the same organization a year from now. You’re left with an environment full of security products that don’t work together, scalability issues, and inefficiencies.
AMP solves these challenges and provides next-generation features, including:
- Continuous monitoring: Continuously watches, analyzes, and records all activity of clean and unknown files on a system. Watch Continuous analysis in 4 minutes.
- Retrospective security: The ability to look back in time and trace processes, file activities, and communications in order to understand the full extent of an infection, establish root causes, and perform remediation. Watch retrospective security feature overview.
- Machine Learning: Breaks down every file and analyzes it against over 400 attributes, constantly training our algorithms to detect never before seen threats.
- Exploit Prevention: Protects against threats targeting unpatched applications, those using legitimate processes, and prevents fileless or memory only malware.
- Antivirus Engine: Performs offline and system-based detections, including rootkit scanning.
- File analysis and sandboxing: Highly-secure environment automatically analyzes suspicious files in order to discover previously unknown threats. Watch file analysis feature overview.
These next-generation features and capabilities are all backed by Cisco’s established, world-leading security research team, Cisco Talos. With over 250 full-time threat researchers, 1,100+ decoy systems and threat traps, and millions of telemetry agents, Talos represents the industry’s largest collection of real-time threat intelligence. Talos’ threat intelligence flows to every Cisco security solution in real-time, so your tools are always equipped with the latest threat intelligence.
Have your cake and eat it, too
The beauty of a comprehensive next-generation endpoint security solution like AMP for Endpoints is that it offers solutions to your most common challenges and integrates with other products across your environment. We integrate these next-generation features on the endpoint with our web, email, network and cloud security solutions, creating an environment of products that continuously share threat intelligence and learn from one another.
If you like having your cake and eating it too, start your AMP for Endpoints free trial on your own endpoints now.