Probably not a day goes by without someone telling you about a new vulnerability or threat to your network and your data. These threats are seemingly everywhere. In order to protect against these threats, we use strong passwords and encryption. Unfortunately, our adversaries are getting the same messages as they continue to scoop up our passwords and use encryption against us. As pointed out by Cisco Technical Leader Blake Anderson in his 2016 blog post “It is fairly straightforward for malware to plug into existing TLS libraries, and in some cases include an entire implementation in its own source code.”.
Earlier this year Cisco announced a new solution called Encrypted Traffic Analytics (ETA). ETA is the result of several years of research and development team led by Blake and Cisco Fellow David McGrew. Blake, David and team sought not to weaken the defense offered by encryption but instead to use negotiated parameters better examine it. ETA creates new meta data based on information exchanged during the process of creating an encrypted communication; defined a new way of observing an encrypted communication; and used intelligence about the nature of the Internet itself in order to risk score encrypted communications. This risk score provides new information to security analysts helping them to determine what hosts and communications to investigate.
It is important to point out that ETA extracts and builds this new meta data without capturing the user’s packets and without decrypting the communication channel. That’s important in that it preserves the data privacy that the user sought by encrypting the communication channel in the first place.
The capability of examining encrypted communications using ETA has now been incorporated into other security features in Cisco IOS-XE operating system. This means that new devices starting with the Cisco Catalyst 9000 family of switches and including the Cisco Aggregated Services Router (ASR) and Integrated Services Routers (ISR) have the capability of generating ETA meta data and exporting that data along with additional telemetry to a Cisco Stealthwatch Enterprise Edition Flow Collector.
Along with this new meta data the team developed a machine learning algorithm that uses that meta data to evaluate and report on the likelihood that a particular encrypted communication between two hosts might contain malware. The Stealthwatch Flow Collector sends meta data about connections that travel between a protected network and the Internet to the Internet based Cisco Cognitive Threat Analytics data center. The Cognitive Threat Analytics team has adapted this research to work within their production system and the resulting risk scores are returned to and appear as a feature of the Stealthwatch Management Console.
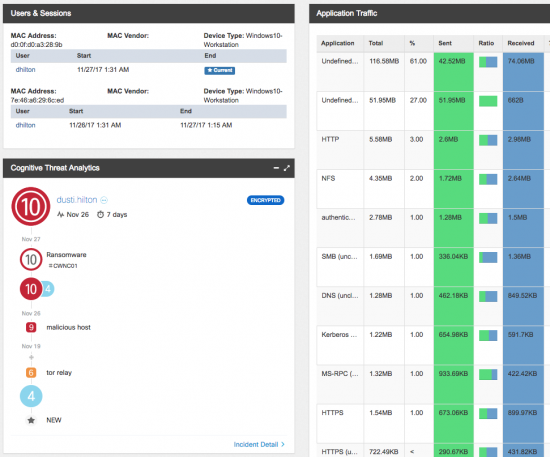
The power of ETA in finding malware is that it provides network defenders with added local intelligence. As the defender examines traffic entering and leaving the protected networks though encrypted channels; they now have access to the parameters used to negotiate the encrypted session and a risk score that provides network security staff guidance about which connections to investigate first. How should they investigate that communication? From the start, the Cognitive Threat Analytics functions in Stealthwatch provide a timeline describing the communications. Next the Cognitive portal reports details about the Internet end of the encrypted communication, including the peers IP address, domain, and autonomous system number. Armed with this information, the defender can respond and contain the threat before it affects the rest of the network.
To learn more about Encrypted Traffic Analytics see: www.cisco.com/go/eta.






Isn't capturing and building metadata exactly what Lancope's Stealthwatch does? I know Cisco bought them recently. I worked for a year and a half as an installer and implementer with that product. It was great. From what I have seen, Cisco is just appropriating the technology and slapping their name on a lot of it. This looks like the same information that I trained companies on when they adopted the StealthWatch solution. What have you done that makes it different?
Kerry,
You are correct that Stealthwatch is all about processing, analyzing meta data, and behavioral analytics. There are many cross product integrations in the ETA project. For ETA a cross Cisco team has developed new network meta data about TLS connections and created new NetFlow data elements in both routers and switches to transport that data (extending NetFlow). In Stealthwatch we added integration with Cognitive Threat Analytics; delivering new cross customer data classifier algorithms to risk score those TLS connections looking for malware. This expands Stealthwatch behavioral analytics adding the ability to report on potential outbreak behavior from other sites and customers.
Brian