This post was authored by Sanjay Raja from Digital Defense, Inc
When determining risk, IT security often has a gaping hole around the assessment of mobile devices. It is challenging to include them in regular vulnerability management (VM) programs for a few reasons, including the fact that they frequently connect and disconnect with networks.
However, it is critical that these devices be included in any security assessment. Threat actors continue to develop new malware designed to exploit even the smallest flaws in mobile devices. In addition, most legacy vulnerability assessment solutions, unfortunately, are not able to assess vulnerability and threat risk before these devices can connect to the network.
Also, leveraging Network Access Control (NAC) with a solution that can provide a real-time understanding of risk can take advantage of policies that restrict access to high-risk or under attack assets. The ability to share greater contextual information, risk posture, and endpoint detection across security and network management platforms can provide IT security and network administrators with better controlling access to sensitive resources.
Effectively Assessing Risk for Mobile Devices Without Agents
One of the most significant challenges to securing mobile devices is installing agents on the device. Too many agents claim to be “lightweight” but end up with a significant negative impact on device performance. Many vulnerability management providers talk about how their agent is stripped down or customized to work on mobile devices. However, they are do not have comprehensive coverage and are still intrusive. This also does not change the fact you are managing yet another agent. Effective scanning of these devices for vulnerabilities and threats requires an agentless design that tracks devices even as they continually connect and disconnect from the network.
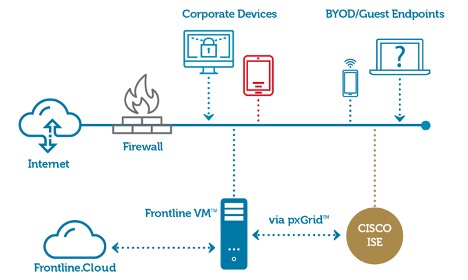
Digital Defense offers agentless vulnerability and threat management via the Frontline.CloudTM platform. Through an integration with Cisco Identity Services Engine (ISE) and leveraging the Cisco Platform Exchange Grid (pxGrid) framework, Frontline.Cloud can perform automated risk and threat posture assessment across multiple platforms, including dynamic assets and mobile devices, to limit the impact of high-risk or infected systems onto the network.
How it Works
Frontline.Cloud consumes mobile device information from Cisco ISE and combines it with vulnerability information already in the platform. Cisco ISE works with major MDM vendors and queries customer MDM servers for the necessary device attributes to create ACLs that provide network access control. In doing so, Cisco can make decisions on whether to deny or allow mobile devices access to the network based on authorized access policy. Cisco ISE can even classify mobile devices with limited access to certain network resources.
Cisco ISE can also obtain needed information from automatic scanning when a device connects to the network for the first time. Cisco ISE validates the information against existing device profiles and applies the appropriate security policies.
Proactive Device Scanning
The Cisco ISE/Frontline.Cloud integration offers a policy to allow Cisco ISE to request an immediate vulnerability scan when a new mobile device comes onto the network. That same policy can restrict access for the given device until Cisco ISE has received the data from Frontline.Cloud. It would then fall to other policies to determine what actions to take based on the findings. With Cisco ISE and Frontline. Cloud, real-time scanning intelligence data adds a level of granularity that allows the system to restrict access of a mobile device that may potentially introduce risk into the network.
To learn more about Cisco ISE/Frontline.Cloud and how it can help you with identifying and managing mobile device security risks click here.
 Sanjay Raja runs field marketing and strategic technical partnerships for Digital Defense, Inc, a provider of next generation SaaS vulnerability management and threat assessment solutions. Prior to Digital Defense, Sanjay was Chief Marketing Officer for Lumeta Corporation, where he led the company to a successful acquisition in two years. Sanjay brings over 20 years of marketing, product management, partnerships, and engineering experience in cybersecurity, networking, performance management and cloud technologies. Sanjay has also held leadership roles in product marketing, product management, strategic alliances and engineering at RSA Netwitness, Cisco, HP Enterprise Security, Crossbeam Systems (acquired by Bluecoat Systems), Top Layer Networks, Caw Networks (acquired by Spirent Communications), Nexsi Systems, 3Com, and Cabletron Systems. Sanjay holds a B.S.E.E and an MBA from Worcester Polytechnic Institute. Sanjay is also a CISSP and Certified Product Manager via Pragmatic Marketing.
Sanjay Raja runs field marketing and strategic technical partnerships for Digital Defense, Inc, a provider of next generation SaaS vulnerability management and threat assessment solutions. Prior to Digital Defense, Sanjay was Chief Marketing Officer for Lumeta Corporation, where he led the company to a successful acquisition in two years. Sanjay brings over 20 years of marketing, product management, partnerships, and engineering experience in cybersecurity, networking, performance management and cloud technologies. Sanjay has also held leadership roles in product marketing, product management, strategic alliances and engineering at RSA Netwitness, Cisco, HP Enterprise Security, Crossbeam Systems (acquired by Bluecoat Systems), Top Layer Networks, Caw Networks (acquired by Spirent Communications), Nexsi Systems, 3Com, and Cabletron Systems. Sanjay holds a B.S.E.E and an MBA from Worcester Polytechnic Institute. Sanjay is also a CISSP and Certified Product Manager via Pragmatic Marketing.





