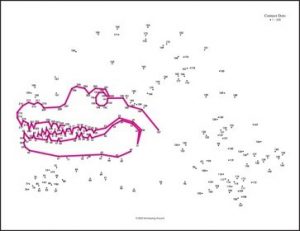
 When I was a kid, I used to love dot-to-dot books. I enjoyed formulating a guess of what the picture was, the hunt in finding all the dots, the satisfaction of connecting them all together, and the excitement of the final picture coming into view to either confirm, or deny, my suspicions of what I was drawing.
When I was a kid, I used to love dot-to-dot books. I enjoyed formulating a guess of what the picture was, the hunt in finding all the dots, the satisfaction of connecting them all together, and the excitement of the final picture coming into view to either confirm, or deny, my suspicions of what I was drawing.
Connecting the dots for better threat protection
Cisco is taking that same approach in connecting the dots across endpoint, network, and cloud, particularly cloud email, for a more effective security posture that sees a threat once and protects against it everywhere. Connecting these dots enables organizations to develop a true picture of accurate threat protection.
AMP has capabilities that enable a threat seen by a firewall, endpoint or email gateway, to be instantly shared to the AMP cloud. Now, with Unity, AMP has a global view of all of the various threats across all of the threat vectors. Unifying the ability to see the commonality between threat vectors.
Unity is a dashboard within the AMP console that connects all the dots of endpoint, network and cloud email together. It allows shared threat intelligence to be able to be correlated across all of these potential threat vectors. A unified dashboard for all correlated and connected devices automates threat sharing throughout the ecosystem. Unity allows you to see the commonality between network, endpoint and email and create a global block across all of the threat vectors.
All of the queries and data within the AMP Cloud from all enabled devices across endpoint, firewall and email are correlated together. This means that if a file that is a potential threat comes across any of these devices on the network, a global trajectory of the files can be provided as it traverses across the network, for better threat detection and faster time to resolution.

With Unity now you can:
Use global outbreak control to create a custom whitelist and blacklist for endpoint, firewall and email to compare files against and coordinate what is blocked and what is not.
Common file policies around indicators of compromise can also be created and all endpoint, network and email gateways that are AMP enabled can be set to adhere to those lists and policies
Set common file policies around indicators of compromise for enhanced threat defense.
Enhance email threat protection by enabling inbound and outbound file trajectory monitoring. This means you can not only ensure that a threat does not enter an environment, but also ensure a threat does not leave via an outbound email, and protect against any inadvertent data leakage from outbound email.
Connecting these dots within a single management console allows for faster threat detection and identification as the ability to better protect against future threats by coordinating your threat defense across multiple threat vectors. AMP Unity enables deep visibility into potential threats, a clear picture of what happened when a threat is detected, and a wide field of view capturing every aspect of what happened from your endpoint to your email gateway and firewall. Unity connects all the dots to give you a true picture of threat defense for your network.
For more information about Cisco Email Security and AMP go to www.cisco.com/go/cloudsecurity
Watch this video about file trajectory and device trajectory features in AMP:
https://youtu.be/8SHwegqD8bY





