Blog 2 of the CISO Experience series
This year Cisco hosted their first CISO Experience at CiscoLive Barcelona, on 29 and 30 January. The event attracted over 60 Chief Information Security Officers (CISOs) and other senior security leaders, who discussed the topics that are shaping cybersecurity in 2018. In the second blog of the CISO Experience series, we broke down recent large-scale attacks and how hackers take advantage of weak security processes and bad user behaviour to get in. Read our first post in the series here.
In 2017, large-scale ransomware attacks have brought cybersecurity to the headlines once again. What was a tough year for CISOs was, in fact, an exciting year for threat researchers such as Warren Mercer, Technical Leader at Cisco Talos and one of the presenters at Cisco’s CISO Experience event in Barcelona.
Mercer observed that over the years there has been a decline in the “low hanging fruits”, the easy attacks such as guessing network passwords, because in general security hygiene has been improving. On the other hand, hackers are becoming bolder and more innovative, and we are experiencing the rise of new devastating attacks, such as WannaCry and Nyetya.
WannaCry, for example, exploited the fact that companies do not patch their networks regularly. It used a known vulnerability, for which a patch had already been released two months prior to the outbreak. Nyetya took advantage of people’s trust in their supply chain; it used a backdoor in a common accounting tool, MeDoc, to infiltrate their targets.
Mercer explained that the majority of complex attacks happen in multiple stages, which is why a layered defence and updated threat intelligence help increase the odds of catching threats earlier.
Are users the weakest link?
How many times have you been to a trade show and got a USB stick as a gift?
Dave Justice, SVP of Global Security and Enterprise Networking Sales at Cisco, believes that the average employee would probably not think twice before plugging an electronic device gifted by a stranger on their corporate computer, which could pose a security risk.
Hackers use people’s trusting nature and social engineering to trick users: they disguise malware into emails and websites in a way that would look legitimate to the untrained eye.
When you pair clever techniques with people’s natural curiosity and lack of security awareness, it makes it very difficult to avoid attacks. Most people do not look at cybersecurity in the same way they look at personal security. With so many things to consider and so little resources and talent available, user awareness often slips down a company’s list of priorities.
Bill O’Connell, Chief Business Security Officer at ADP, believes companies should help increase security awareness not only within their businesses but also in the broader market, by taking a more active role in larger initiatives such as the Cybersecurity Awareness Month.
Justice from Cisco reinforced the importance of stopping threats at the endpoint; he also discussed how Cisco products are able to detect a threat once and enforce changes everywhere across the network, effectively making it stronger after every incident.
Mind the Talent Gap
User awareness is not the only challenge. Companies are overwhelmed with the volume of security alerts they need to manage, not to mention the complexity of having multiple security products from different vendors. In addition to that, there is a shortage of qualified security professionals.
Estimates vary, but some researchers believe that the cybersecurity talent gap may reach 3.5 million unfilled jobs by 2021.
Richard Goodman, Head of Network and Security Services at John Lewis Partnership and one of the presenters at the Cisco event, believes that companies should play a bigger role in forming the next generation of security professionals. He shared that John Lewis runs a talent program that helps educate IT professionals on security. For those employees, it is an opportunity to learn new skills and further their careers, while the business benefits from a regular supply of talented security professionals.
Goodman highlighted that programs like this are only possible if companies stop seeing security as an obstacle and start looking at it from a different perspective, as a growth enabler. For instance, John Lewis is using technology such as the IoT to make customer experience feel seamless, whether they shop online or in store. This type of transformation cannot be truly effective if the technology is not secure. Thanks to this proactive security posture, John Lewis Partnership received a Cisco Circle Security Award for their innovative security operations for Retail.
Freerk Bosscha, Security Officer of NHL University also found a creative way to help fix the talent gap issue and benefit directly from it. Not only does NHL offer cybersecurity courses, but they also encourage their students to help pen test the university’s defences and report their findings. He also says he rewards students with more access privileges when they accept to have security software installed on their devices.
Empower your SecOps team
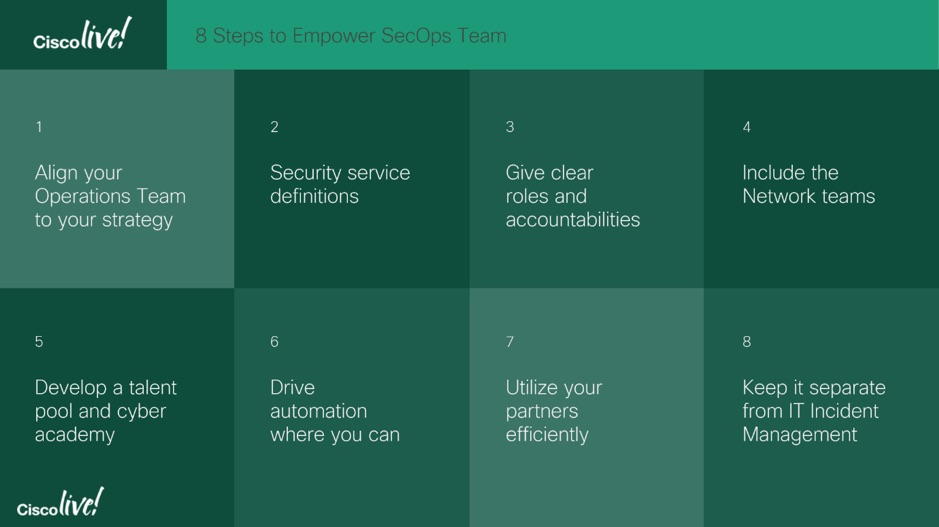
Goodman from John Lewis also highlighted the importance of closing the gaps in communication between CISOs and Security Operations (SecOps) managers. Here are eight steps he recommended to CISO to help empower their SecOps team:
Next in the CISO Experience series:
In our third and final blog, we covered the insights from security leaders at ADP, Enel and Cisco about how to make security a business priority and how regulations such as GDPR help secure investments.