More than 25,000 attendees visited Cisco Live in Orlando this year. While this large concentration of network and security professionals was learning about our latest innovations, Cisco Security was busy catching bad guys! Of course we protect our own show, but this year was special… More than 170 command and control events, 553 exfiltrations and loads of encrypted malware hiding in 103 million HTTPS flows from iPhones, Androids, demo stations and laptops.
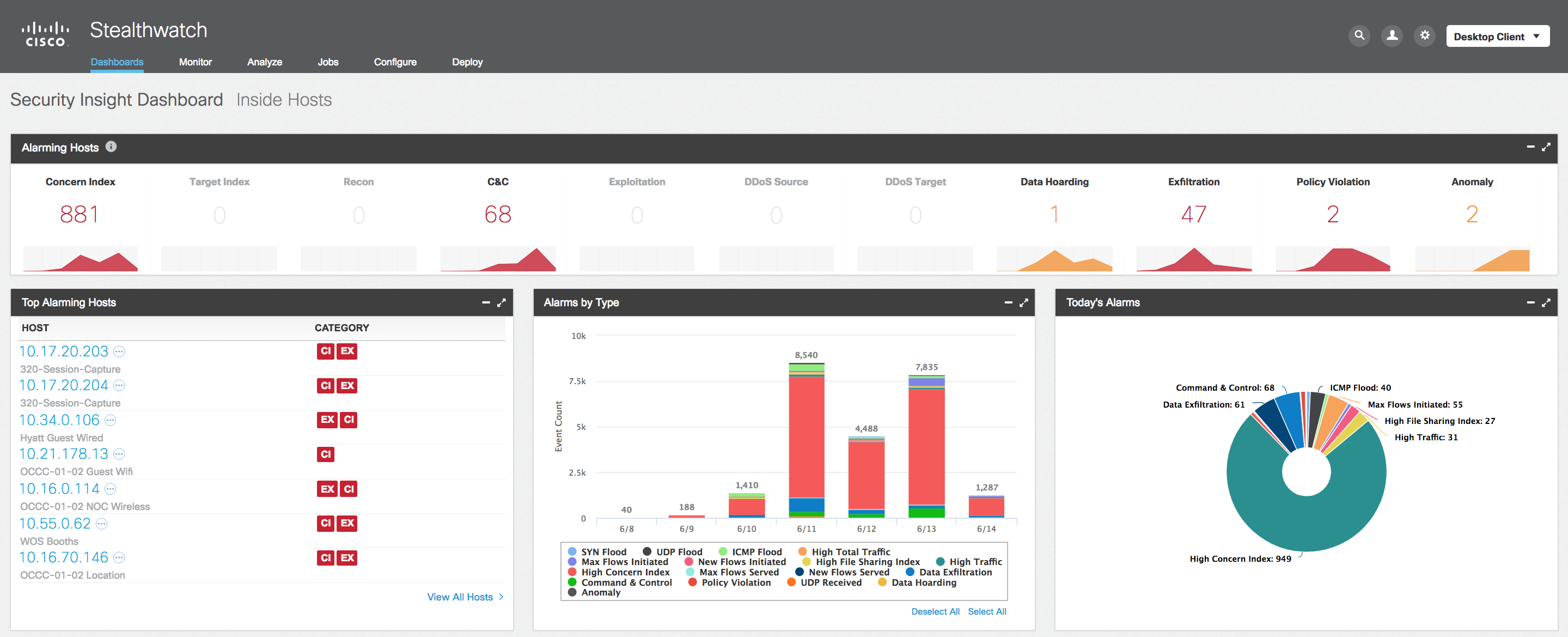
This is a massive public network. Cisco used numerous security products to see threats real-time, including Cisco Stealthwatch with Cisco Encrypted Traffic Analytics. Throughout the course of the event, Cisco identified a number of threats and vulnerable traffic.
Here are some of the highlights:
Eighty-eight percent of web traffic flows were encrypted
Over the course of the event, we observed 103 million HTTPS flows versus 13.5 million HTTP flows, coming out to 88 percent encrypted versus 12 percent unencrypted mix. During peak hours, Encrypted Traffic Analytics with the Cisco ASR 1000 series generated more than 50,000 flows per second.
In addition, we detected several applications using TLS 1.0, an outdated cryptographic protocol with known vulnerabilities. The Payment Card Industry Security Standards Council (PCI SSC) suggests organizations migrate from TLS 1.0 to TLS 1.1 or higher by June 30, 2018.
More than 5000 events reduced to 398 security detections, including 7 critical and high risks
We detected more than 5000 individual security events, including numerous data exfiltration and command-and-control events. Using cloud-based machine learning and global risk maps, Stealthwatch automatically reduced that number to 398 significant security detections, including 7 that ranked as critical- and high-risk detections.
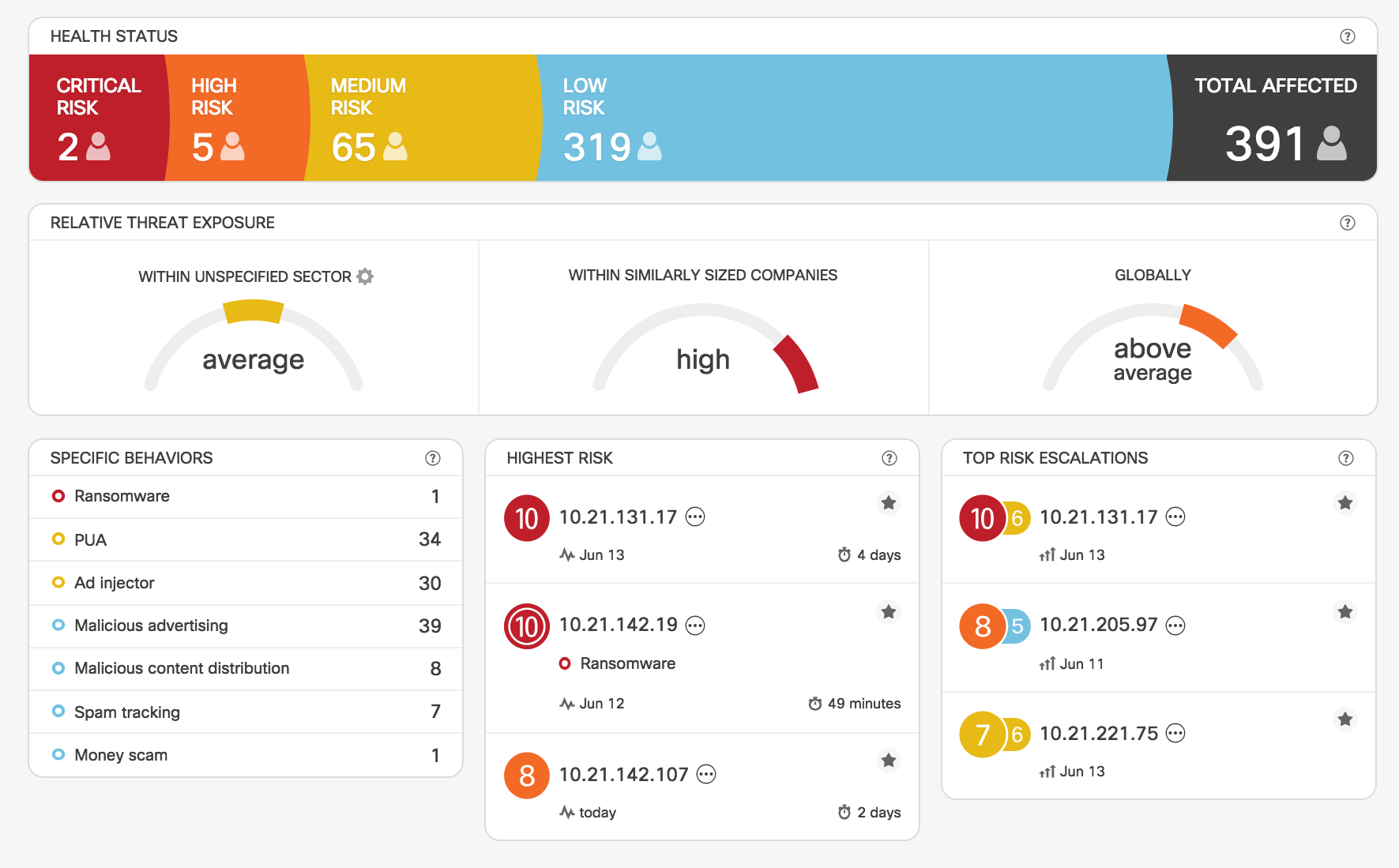
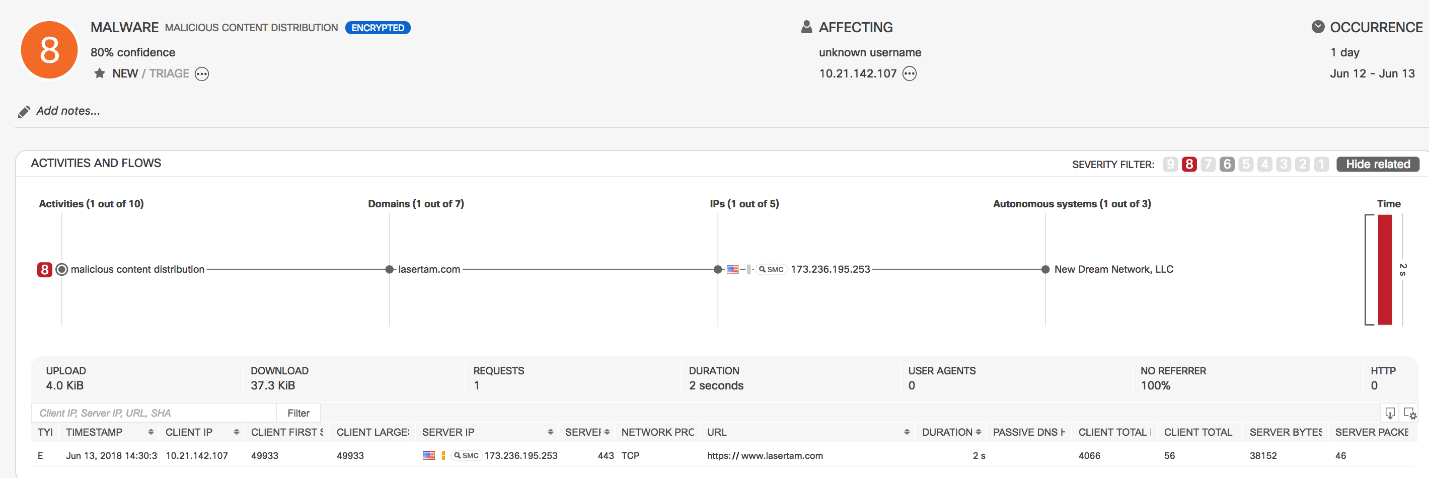
Encrypted Traffic Analytics detected several instances of malware that were injecting encrypted adware into webpages. A few instances of cryptomining were also detected.
Other detections include:
- Encrypted botnet activity
- AdInjector infections
- Excessive DNS usage
- Tor activity
- BitTorrent activity
- Several instances of other malware or potentially unwanted applications using encryption
Learn more
The activity observed at Cisco Live U.S. falls in line with a larger trend we are seeing. A significant portion of the traffic was encrypted, creating a potential blind spot for security analysts. While not every threat we observed used encryption traffic, a number of them did, including malicious adware injection malware. Fortunately, Cisco Encrypted Traffic Analytics helped detects these threats – without the use of decryption.
Don’t want to take our word for it? Read an independent analysis that found Cisco Encrypted Traffic Analytics delivers impressively fast, efficient, and intelligent threat detection.





