In recent weeks, the volume of malicious email carrying attachments has increased substantially. To entice recipients into opening those attachments, attackers are employing pitches across a wide range of subjects. In doing so, they are defeating the often doled out advice to not open attachments in email received unexpectedly.
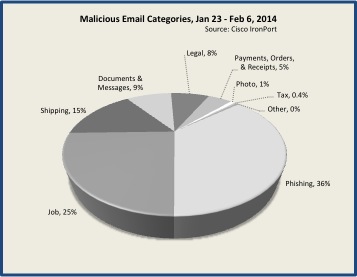
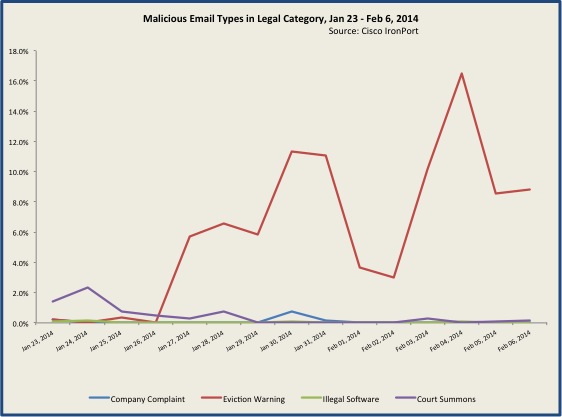
One of the more striking examples of this is malicious email exploiting bad economic conditions, job loss, and potential loss of home. The combined legal and job categories comprised 33% of malicious email attachments over the past two weeks, with pitches ranging from bogus employment opportunities to court summons for evictions due to overdue payments.
Other legal-oriented email includes warnings of illegal use of software, copyright infringement, and criminal complaints for alleged non-payment of accounts.
Assuming you were in dire financial straits, it’s not difficult to imagine you would react to an eviction notice such as the following:
Eviction notification,
You are hereby given notice that you are in breach
of your tenancy of the premises you currently occupy.To remedy the breach you have to quit
the premises within the following four weeks.If you fail to comply you will be physically removed
and fined for up to 100 minimum monthly wages.Detailed information is attached herewith.
Of course, the promised ‘detailed attachment’ is cleverly named “Lawsuit_Details _Copy_ID504-62.zip”.
Certainly those who are gainfully employed and current on their bills may not find these pitches believable. However, attackers are playing a pure numbers game – making the guess that some percent of recipients will be unemployed, some will be financially behind in payments, and, sadly, some will be in danger of facing eviction from their homes. For these users, the email pitch becomes very believable and ‘expected’. And attackers have an additional edge as well – few of us can imagine that anyone would want to target and harm a person who is already down on their luck and suffering. Yet that is exactly what this category of malicious email is designed to do.
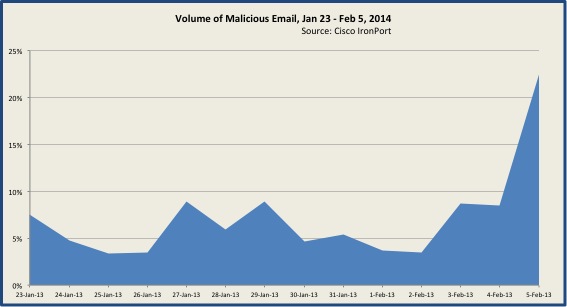
At 36%, phishing scams employing malicious attachments also factored significantly over the past two weeks, mainly due to an outbreak beginning Feb 4th. This increase was significant enough to affect overall volume of malicious email, as seen in the chart below.
To up the believability quotient, many of the phish are disguised as year-end summary statements from credit card providers – at a time when many legitimate such statements are indeed being emailed to users. As with the legal scams, phishers don’t expect to net 100% of recipients; they are simply hoping that a certain percent will be anticipating such a summary statement and thus be more likely to react.
Dear Valued CardMember,
We are pleased to confirm that your 2013 Year-End Summary for charges on your American Express(R) Card(s) is now ready to view online.
Your online Summary provides a categorized snapshot of your total spend for the past year, allowing you to view your charges and better manage your future spending. You may also download a PDF copy of this summary.
The email helpfully provides instructions:
To continue, We have sent you an attached HTML Web Page.**
* **See e-mail attachement **
* **Download and save it**
* **Open the attached document
Of course, following these instructions sends your credentials, credit card details and other sensitive financial information directly to the attackers.
Also abundant over the past two weeks were malicious email disguised as fax and voice messages, shipping and parcel claims, purchase orders and invoices, photographs alleging you or a friend were captured in a provocative pose, and a small handful of tax-related scams. Many of these were delivering variants of Zbot/Zeus downloaders that employ the GameOver Zeus encryption bypass reported by Gary Warner in early February.
While the above applies only to email carrying malicious attachments, the same broad range of subjects can be found with email harboring malicious links. For example, email claiming to pertain to funeral invitations has been distributing links to malware-infested sites since mid-January. In December, wedding invitation pitches were equally prolific.
In short, attackers are using the definition of ‘expected’ against us. While today’s pitch may not be relevant to events in our life today, tomorrow’s pitch may very well be. In other words, even if an email passes the ‘expected’ test, it may still very well be malicious.






and they are using credit reports claiming free srevices
Hi folks,
I am a presales working in ST Electronics (Info Comm Systems) Pte Ltd, a partner with CISCO. However, my email had delivery issue when I send to any CISCO personnel. Please kindly help to resolve my email issue with your side. Thanks.
Error as followed:
The following message to was undeliverable.
The reason for the problem:
5.1.0 – Unknown address error 550-‘Connections from the host mengtze.stee.com.sg (61.8.252.34), originating from SenderBase Network Owner ID: 88377, are being rejected due to a low SenderBase Reputation Score. See http://www.senderbase.org for more information or contact your IT support team.’