The Challenge of implementing SPF and DKIM
It’s no surprise that email authentication standards such as Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM) have not been widely adopted. However, organizations must take advantage of them to tackle two of the most pressing email security problems: lack of visibility into who uses your domains to send email on your behalf and not knowing whether unauthorized email is being rejected accurately.
Consider the following SPF record example, where you have authorized a single IP address “123.123.5.5” to send on your organization’s behalf “youorganization.com”. yourorganization.com TXT “vspf1 ip4:123.123.5.5 -all”
First, while the policy is set to reject messages that fail authentication, you have no ability to confirm that the policy is being enforced. Receiving hosts can choose to ignore the policy or enforce a different action, and this can leave your customers exposed to the threat. Worst yet, if you inadvertently replace “-all” with “~all”, messages failing authentication are now delivered without you being alerted.
Second, while the policy is restricted to a single sending IP address, email can take different paths to the final destination. If you are not aware of the full path and email is first forwarded to a different host prior to the final destination, SPF verification will fail. In order for SPF authentication to work correctly, all authorized sender hosts in the email path must be defined.
Finally, while you as the email administrator may have authorized a single sending IP to control what leaves your infrastructure, other business groups may not be aware of your restriction. It would be common practice for your marketing team to use a 3rd party sender such as Sendgrid or Constant Contact to send email related to a marketing or sales campaign. However, the restriction in place would reject these legitimate messages, compromising the success of the campaign.
Advantages to Using DMARC
Using DMARC (Domain-based Message Authentication, Reporting, and Conformance) solves these issues and enables your organization to harness SPF and DKIM to protect your customers, partners, and employees against phishing attacks. DMARC employs several key improvements missing in the existing email authentication standards, but the two key advantages are that:
- DMARC provides a more flexible policy that allows you to instruct the receiver to enforce different actions for top-level and sub-domains, such as “do nothing”, “quarantine the message”, or “reject the message” if SPF or DKIM authentication fail. Management of a single policy across your SPF and DKIM records eliminates user error.
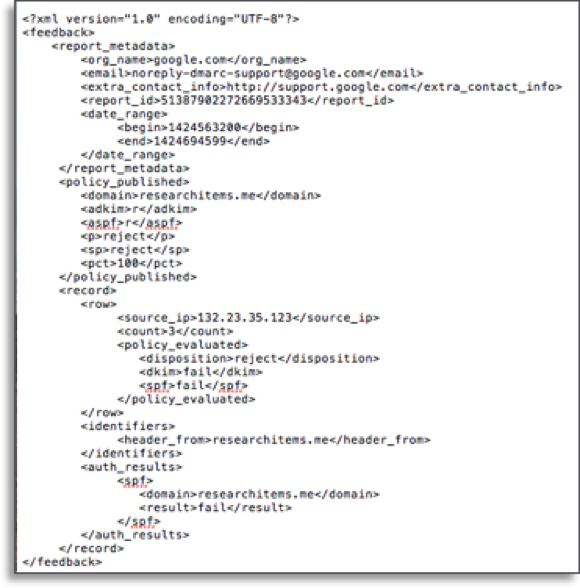
- DMARC instructs receiving hosts to provide feedback regarding your domains’ email authentication results. The results provide a holistic view into your cyberattack risk and helps you to identify and authorize only the senders you know, ultimately protecting customers from phishing and improving your authorized email deliverability rates.
Unfortunately, most organizations do not have the expertise, time, or resources to properly implement, parse, and make sense of the data. Imagine having to consume, interpret, and implement the necessary changes that result from the hundreds of daily DMARC aggregate and forensic reports received. Most organizations would need a dedicated team to accomplish this feat!
How Cisco Domain Protection Makes DMARC Easier
Cisco Domain Protection automates this process, as we mentioned in our last blog on why phishing attacks win and what you can do about it.
It can quickly consume DMARC aggregate and forensic reports to visually display the email authentication results for every message sent on behalf of your domains. Furthermore, coupling the results with insights from our global telemetry network that includes trillions of emails, we’ll automatically build a sender inventory that can tell you if the sender is malicious, a legitimate organization, or a well-known 3rd party sender such as MailChimp or Marketo. With this visibility, you’ll know exactly who should be allowed to send email on your behalf and be able to follow a workflow that tells you how properly build your SPF and DKIM records. You’ll get to a DMARC enforcement policy faster and with less resources than with any other solution. For a demo of this technology in action, watch this 10-minute Threatwise TV Episode on Cisco Domain Protection.
Subscribe to email security blogs for an alert when we release the upcoming part 3 of this series. We’ll discuss how Cisco enhances employee protection with new advanced anti-phishing capabilities.






To the point, concise. Thanks.
Thanks. Stay tuned for part 3!!!
Extremely informative and engaging! Thanks!