The Public Cloud and Security Responsibility
Across many businesses, leveraging services offered and hosted by public cloud providers such as AWS proves to be extremely advantageous for both improving operational efficiencies, cost savings, scaling, and for security.
For AWS customers, Lambda functions are a great example of this advantage in providing a useful way to execute only the code you need to execute when you need to execute it, saving businesses money on hosting costs and reducing operational overhead. This allows customers to scale to their needs and only pay for what they need to run their tasks and applications that drive their business.
Another business benefit is with security. The infrastructure security for running these services is covered by the cloud provider, which means less overhead and worry for the business using these services. However, this does not mean customers of public cloud providers have zero security responsibility. Per the shared responsibility model from AWS, customers are still responsible for security in the cloud.
Enter Denonia
Denonia is a cryptocurrency mining software that is specifically designed to run on AWS Lambda, recently discovered by Cado Security on April 6th, 2022. It is likely that Denonia has been running prior to this date, so adjust your investigations accordingly.
According to Cado, the software could be delivered by leveraging DNS over HTTPS to avoid detection at the network access layer and using compromised credentials to execute the software designed for Lambda environments.
In the case of this software targeting AWS Lambda, customers are responsible for securing the functions themselves including who and what has access, network connections, and securing the code that runs on the functions.
Analyzing Denonia
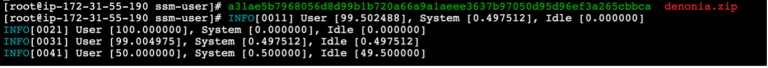
Our research team at Cisco Talos tested the Denonia package using a Lambda Function in our lab. Upon executing we monitored AWS CloudWatch Logs and behavior in Secure Cloud Analytics, we noticed several interesting insights about how it functions:
- Several console log messages that resembled HTTP GET requests were logged to various domains with spoofed user agents including that of the Baidu web spider, Archive.org bot, and Android 4.1.2 browser.
- Running the strings command on the malware binary shows that these system log messages are hard coded in the binary, including the HTTP response codes, and are apparently printed to the console upon execution.
- We found console log messages printed by XMRig, an example of which would be time=”2022-04-13T16:20:44Z” level=info msg=”User [14.705882], System [0.000000], Idle [85.294118]”
- Once we updated the Lambda to use a VPC in our test lab, the function exited with status 1, and the logs showed an error “panic: doh: all query failed”. This potentially indicates that DNS over HTTPS was not supported either by the Lambda or the VPC.
- We found similar results to above when tested on EC2 with root privileges and using lamb-ci’s Docker Lambda project to run the Lambda environment locally in Docker containers, Denonia was successfully executed.
So far, there have not been any known successful deployments, but they key takeaway is attackers are targeting specific resources from cloud providers and becoming increasing sophisticated in the public cloud, so this just may be the start of targeted attacks on serverless functions and other public cloud services
Continuous Monitoring and Threat Detection in the Public Cloud using Cisco Secure Cloud Analytics
Cisco Secure Cloud Analytics is a SaaS based security product that provides broad visibility and detection within public cloud services across AWS, Azure, and GCP leveraging APIs and logs from the providers, all without deployment of agents.
When looking at Denonia as a potential attack targeting services and applications running in the public cloud, Secure Cloud Analytics provides a wide array of detection capabilities to see an attack at many stages of its lifecycle.
Working with our research team at Cisco Talos, we have identified several methods for detecting Denonia and attacks like it in the public cloud using Secure Cloud Analytics.
With Secure Cloud Analytics deep ability to baseline normal behavior, behavior seen by Denonia or other software or malware that triggers an unusually large number of Lambda functions will trigger the alert “AWS Lambda Invocation Spike” due to the typically short default timeouts of a Lambda function and the need for many of those resources to leverage the functions to execute the attack and leverage the resources for the goal.

Additionally, if devices connect with a known bad domain or IP from Denonia, Secure Cloud Analytics will trigger a ““Talos Intelligence Watchlist Hits” alert which indicates a device on the network communicated with a known bad domain or IP from Cisco Talos. Domain or IP matching is not always guaranteed in cases like Denonia where DNS over HTTPS is used, therefore it’s important to look at malicious behavior in conjunction with known IOCs for complete visibility and detection capability.

Domains:
- denonia[.]xyz
- ctrl.denonia[.]xyz
- gw.denonia[.]xyz
- 1.gw.denonia[.]xyz
- www.denonia[.]xyz
- xyz.denonia[.]xyz
- mlcpugw.denonia[.]xyz
IP Addresses:
- 116.203.4[.]0
- 162.55.241[.]99
- 148.251.77[.]55
Further our researchers indicated other common attacker techniques may be seen with the rich behavioral visibility of Secure Cloud Analytics in the public cloud that may be correlated with the above finding for Denonia or other like threats.
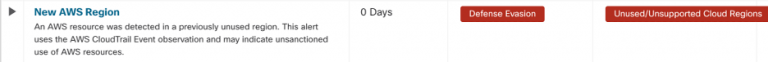
“New AWS Region” alert which can be used to detect defense evasion targeting unused regions.
“Geographically Unusual AWS API Usage” alert which can highlight initial access through valid identity and access management accounts.

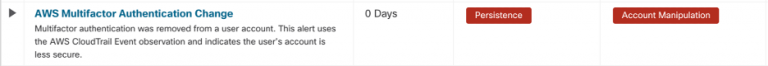
“AWS Mulifactor Authentication Change” alert which can identify disabling MFA.
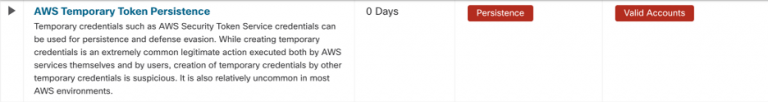
“AWS Temporary Token Persistence” alert which identifies temporary tokens created by other temporary credentials.
Although the above alerts are specific to AWS, we have expanded our coverage to other common cloud providers such as Azure and GCP as customer utilization has grown for similar detection outcomes.
In addition to public cloud specific detection, Secure Cloud Analytics offers a wide range of threat detection across an organization’s private network, all within a single pane of glass.
Protect Your Public Cloud Today
To learn more, go to https://www.cisco.com/go/secure-cloud-analytics and start a free risk free 60 day trial.
For more up to date threat information, follow the Cisco Talos blog, including other recent threats targeting the public cloud by TeamTNT.
References
https://aws.amazon.com/compliance/shared-responsibility-model/
https://www.cadosecurity.com/cado-discovers-denonia-the-first-malware-specifically-targeting-lambda/
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn





