Since the earliest days of computing, we’ve endeavored to provide users with efficient, secure access to the critical applications which power the business.
From those early mainframe applications being accessed from hard-wired dumb terminals to the modern cloud-based application architectures of today, accessible to any user, from anywhere, on any device, we’ve witnessed the changing technology landscape deliver monumental gains in user productivity and flexibility. With today’s workforce being increasingly remote, the delivery of secure, remote access to corporate IT resources and applications is more important than ever.
Although the remote access VPN has been dutifully providing secure, remote access for many years now, the advantages of centrally administering and securing the user desktop through Virtual Desktop Infrastructure (VDI) are driving rapid growth in adoption. With options including hosting of the virtual desktop directly in the data center as VDI or in the public cloud as Desktop-as-a-Service (DaaS), organizations can quickly scale the environment to meet business demand in a rapidly changing world.
Allowing users to access a managed desktop instance from any personal laptop or mobile device, with direct access to their applications provides cost efficiencies and great flexibility with lower bandwidth consumption…. and it’s more secure, right? Well, not so fast!
Considering the Risks
Although addressing some of the key challenges in enabling a remote workforce, VDI introduces a whole new set of considerations for IT security. After all, we’ve spent years keeping users OUT of the data center…. and now with VDI, the user desktop itself now resides on a virtual machine, hosted directly inside the data center or cloud, right inside the perimeter security which is there to protect the organization’s most critical assets. The data!
This raises some important questions around how we can secure these environments and address some of these new risks.
- Who is connecting remotely to the virtual desktop?
- Which applications are being accessed from the virtual desktops?
- Can virtual desktops communicate with each other?
- What else can the virtual desktop gain access to outside of traditional apps?
- Can the virtual desktop in any way open a reverse tunnel or proxy out to the Internet?
- What is the security posture of the remote user device?
- If the remote device is infected by virus or malware, is there any possible way that might infect the virtual desktop?
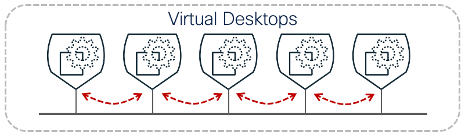
- If the virtual desktop itself is infected by virus or malware, could an attacker access or infect other desktops, application servers, databases etc. Are you sure?
With VDI solutions today ranging from traditional on-premises solutions from Citrix and VMware to cloud offered services with Windows Virtual Desktop from Azure and Amazon Workspaces from AWS, there are differing approaches to the delivery of a common foundation for secure authentication, transport and endpoint control. What is lacking however, is the ability to address some of the key fundamentals for a Zero Trust approach to user and application security across the multiple environments and vendors that make up most IT landscapes today.
How can Cisco Secure Workload (Tetration) help?
Cisco Secure Workload (Tetration) provides zero trust segmentation for VDI endpoints AND applications. Founded on a least-privilege access model, this allows the administrator to centrally define and enforce a dynamic segmentation policy to each and every desktop instance and application workload. Requiring no infrastructure changes and supporting any data center or cloud environment, this allows for a more flexible, scalable approach to address critical security concerns, today!
Establishing Control for Virtual Desktops
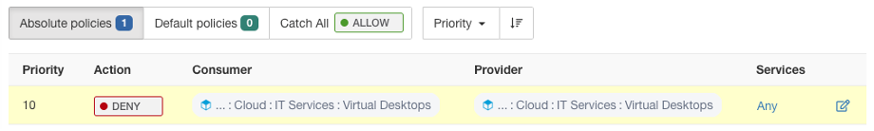
With Secure Workload, administrators can enforce a dynamic allow-list policy which allows users to access a defined set of applications and resources, while restricting any other connectivity. Virtual desktops are typically connected to a shared virtual network, leaving a wide-open attack surface for lateral movement or malware propagation so this policy provides an immediate benefit in restriction of desktop to desktop communication.
This flexible policy allows rules to be defined based on context, whether identifying a specific desktop group/pool, application workloads or vulnerable machines, providing simplicity in administration and the flexibility to adapt to a changing environment without further modification.
- Do your VDI instances really need to communicate with one another?
With a single policy rule, Secure Workload can enforce a desktop isolation policy to restrict communication between desktop instances without impacting critical services and application access. This simple step will immediately block malware propagation and restrict visibility and lateral movement between desktops.
- Want to permit only a specific user group access to your highly sensitive HR application?
Secure Workload will identify the desktop instances and application workloads by context, continuously refreshing the allow-list policy rules to permit this communication as users log in and out of their virtual desktops and as the application workloads evolve.
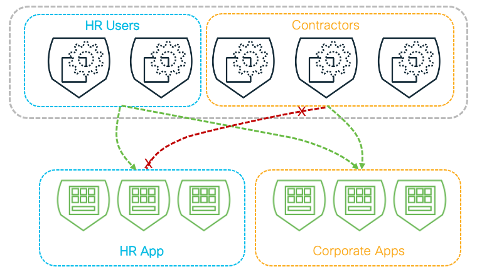
- Need full visibility of which applications are being accessed, how and when?
Tetration not only enforces the allow-list policy to protect your assets, but also records flow data from every communication, ensuring continuous near-real-time compliance monitoring of traffic to identify malicious or anomalous behaviors.
- Need to meet segmentation requirements for regulatory compliance?
Natural language policy definition based on dynamic labels and annotations ensures traffic complies with regulatory policy constraints from one well-defined policy intent.
- Require the ability to automatically quarantine vulnerable virtual desktops or application workloads to protect against exploit?
Tetration natively detects vulnerable software packages to apply automated policy controls which only apply until remediation.
All offered from SaaS, this can be achieved without any change to existing infrastructure, with distributed enforcement at scale from virtual desktops to application workloads for end to end protection.
Ready to get started? Find out more about Cisco Secure Workload





