I was at the Gartner Security and Risk Management Summit at the Gaylord National Harbor and had the opportunity to attend the session, “Finding the Sweet Spot to Balance Cyber Risk,” which Tammie Leith was facilitating.
During the session, the panel had been discussing how the senior leadership teams address the problem of putting their signatures against the risk that cyber threats pose to their organizations. Tammie Leith made a point to the effect that it is just as important for our teams to tell us why we should not accept or acknowledge those risks so that we can increase investments to mitigate those risks.
What caught my attention was that the senior management teams are beginning to question the technical teams on whether or not appropriate steps have been taken to minimize the risks to the corporation. The CxO (senior leadership team that has to put their signature on the risk disclosure documents) teams are no longer comfortable with blindly assuming the increasing risks to the business from cyber threats.
To make matters worse, the CxO teams and the IT security teams generally speak different languages in that they are both using terms with meanings relevant to their specific roles in the company. In the past, this has not been a problem because both teams were performing very critical and very different functions for the business. The CxO team is focused on revenue, expenses, margins, profits, shareholder value, and other critical business metrics to drive for success. The IT security teams, on the other hand, are worried about breaches, data loss prevention, indications of compromise, denial of services attacks and more in order to keep the cyber attackers out of the corporate network. The challenge is that both teams use the common term of risk, but in different ways. Today’s threat environment has forced the risk environment to blend. Sophisticated targeted attacks and advanced polymorphic malware affect a business’s bottom line. Theft of critical information, such as credit card numbers, health insurance records, and social security numbers, result in revenue losses, bad reputation, regulatory fines, and lawsuits. Because these teams have not typically communicated very well in the past, how can we ensure that they have a converged meaning for risk when they are speaking different “languages”?
In order to fully explore the variations to the term “risk” for the business, I wanted to understand what the Security Exchange Commission (SEC) required of corporations in reporting requirements to their shareholders. The 2013 Cybersecurity Executive Order signed by President Obama, and the release of the NIST Cyber Framework seemed to be giving the SEC a new reason to revisit the topic of cyber security with a revitalized vigor.

The SEC had already published guidance on how corporations should provide cyber security risk disclosures in the CV Disclosure Guidance: Topic No. 2 Date: October 13, 2011. However, the speech that SEC Commissioner Luis A. Aguilar gave at the “Cyber Risks and The Boardroom Conference” at the New York Stock Exchange on June 10 discussed what the “boards of directors can, and should, do to ensure that their organizations are appropriately considering and addressing cyber risks.” In proposing a strong case for the boards of directors to take action, he discussed the “threat of litigation and potential liability for failing to implement adequate steps to protect the company from cyber-threats.” He also discussed the derivative lawsuits that were brought against companies, their officers and directors relating to data breaches. What caught my attention most about the speech is when he said, “Thus, boards that chose to ignore, or minimize, the importance of cybersecurity oversight responsibility, do so at their own peril.”
Commissioner Aguilar made a strong recommendation for corporations to voluntarily adopt the NIST Cybersecurity Framework in order to begin addressing the problem with the statement, “While the Framework is voluntary guidance for any company, some commenters have already suggested that it will likely become a baseline for best practices by companies, including assessing legal or regulatory exposure to these issues or for insurance purposes.”
I am not disagreeing with Commissioner Aguilar, but in practice, this is an incredible challenge for any board of directors as they are now being asked to provide direct cyber security oversight to the internal day-to-day operations of the organization or risk “peril.”
The board of directors is forced to start challenging the CxO teams about how the company taking action in mitigating cyber threats in a similar way that Tammie Leith was proposing that the CxO teams challenge their technical teams. To make matters worse, the board of directors will be defining risk in a way that is different from the CxO team and will be different from the technical team’s definition of risk, which results in a three-way translation issue where the critical understanding of the seemingly simple term of “risk” is lost in translation.
So how do we go from the board being asked to follow the NIST Cybersecurity Framework to mitigate cyber security risk, the CxO Team asking what should they invest in order to reduce the risk to the business, and then the IT teams trying to implement the security products and technologies to prevent the attacks in the first place?
For the board, they will need to identify a trusted partner such as a top-tier business management consulting firm such as Ernst & Young and others. One that has established cyber security practices and understands how to guide the board in managing and reporting the cyber security risk exposure to the business. A top-tier firm can ensure that the business is conducting the proper cyber security management programs and demonstrate that the board has implemented the proper cyber security oversight as suggested by SEC Commissioner Aguilar. A good resource document in this area is Ernst & Young’s “Technology risk management in a cyber world.”
The CxO team will need to drive their security organization to implement a cyber management frame like the NIST Cybersecurity Framework. There are other methodologies that can be followed, but it will take the CxO team to commit to implementing new business processes.
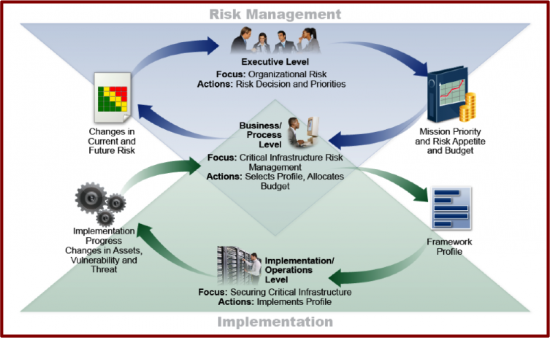
Source: NIST Framework for Improving Critical Infrastructure Cybersecurity
While these frameworks provide for a comprehensive approach to managing the cyber threats, they do not ensure that the proper threat management capabilities have been put in place to enable their IT security teams to have a “real life” response to today’s cyber attacks. When organizations implement these frameworks without a focus on implementing capabilities, they leave the organization exposed.
A great place to start for the IT security team is to download the Cisco Secure Data Center for the Enterprise Solution Portfolio that is designed to protect the data center, which is the “Fort Knox” of the corporation’s valuable data assets and is one of the primary targets for the cyber attackers.
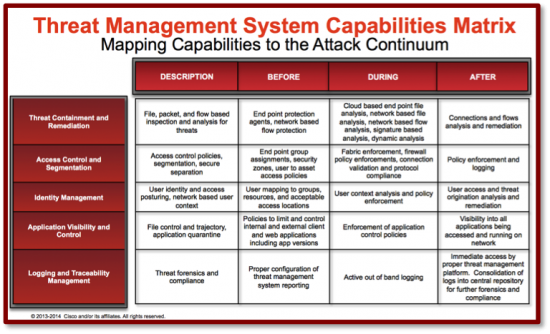
The Cisco Secure Data Center for the Enterprise Solution Portfolio provides a “Threat Management Systems Capabilities Matrix” to give the IT Security teams a way to map threat management capabilities to Cisco’s Before, During, and After Security Model, which can be applied across the entire organization. By leveraging these design guides, the IT Security Teams will build a solid foundation for the NIST Cybersecurity Framework. Without the solid foundation built with capabilities, the effectiveness of the entire threat management program will be reduced and as a result, the risk assumed by the CxO teams and the Board will be significantly increased.
References:
Gartner Security & Risk Management Summit
http://www.gartner.com/technology/summits/na/security/
New York Stock Exchange: Cyber Risk and The Boardroom
http://www.cvent.com/events/cyber-risks-and-the-boardroom/event-summary-5a0527d4f58a4e4c9969719262e12933.aspx
SEC Biography: Commissioner Luis A. Aguilar
https://www.sec.gov/about/commissioner/aguilar.htm#.U63LU6ibQY0
Boards of Directors, Corporate Governance and Cyber Risks: Sharpening the Focus
http://www.sec.gov/News/Speech/Detail/Speech/1370542057946#.U7wPqKibTzG
Framework for Improving Critical Infrastructure Cybersecurity
http://www.nist.gov/cyberframework/upload/cybersecurity-framework-021214-final.pdf
Federal Register, Feb. 19, 2013
Executive Order 13636 – Improving Critical Security Infrastructure Cybersecurity
http://www.gpo.gov/fdsys/pkg/FR-2013-02-19/pdf/2013-03915.pdf





