The eagerly anticipated Cisco Vulnerability Management (formerly Kenna.VM) integration with Cisco Secure Endpoint is officially available! As of today, vulnerability assessment can be conducted with Cisco Secure Endpoint and ingested into Cisco Vulnerability Management for analysis, prioritization, and management.
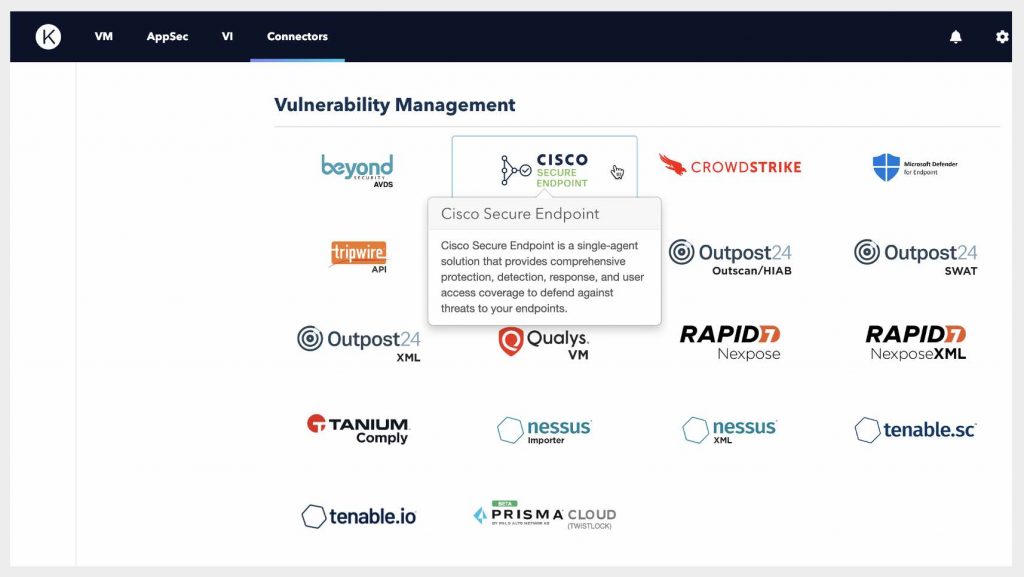
Our team builds a lot of integrations (we have 55+ native integrations) but this one sure gets us excited. This integration opens the door to new opportunities for Cisco Secure Endpoint customers, Cisco Vulnerability Management customers, and prospects of both solutions. Generally, it’s a boon for any security team looking for a way to move their vulnerability management program to a risk-based approach.
What does this integration do?
As a Cisco Vulnerability Management and Cisco Secure Endpoint customer, you will do the initial integration set up, schedule your integration runs, and then you’re off. Asset and vulnerability data from Cisco Secure Endpoint will be ingested directly into Cisco Vulnerability Management, where you will see standard vulnerability information—our Risk Scoring, descriptions and characteristics, fix information, and much more.
What is the benefit for me, the customer?
In a nutshell, this integration lets you turn on risk-based vulnerability management. If you’re a Secure Endpoint customer, you may know that some of Cisco Vulnerability Management’s vulnerability intelligence is already visible in Secure Endpoint. Right now, this intelligence gives a glimpse into what Cisco Vulnerability Management can do.
Cisco Vulnerability Management is a platform designed for risk-based vulnerability management. Not only can you bring in Cisco Secure Endpoint data, but you can also connect any additional vulnerability data sources in your environment (like a network vulnerability scanner). All of this data is centralized in one view and available for you to manage via Risk Meters (or asset groups that meet specific criteria). And of course, in Cisco Vulnerability Management, our risk scoring is front and center—you’ll see scoring for vulnerabilities, assets, Risk Meters, and the organization as a whole.
Why does risk scoring matter?
Ultimately, the risk scoring your team leverages determines what you remediate and when. This impacts both your overall risk posture, as well as the efficiency of your resources. Cisco Vulnerability Management uses data science to analyze both your internal security data as well as a wealth of external exploit and threat intelligence to understand the true risk profile of vulnerabilities within your environment. The resulting scores ultimately help customers and prioritize the vulnerabilities that pose a real risk (those that are both observed in enterprises and exploited in the wild).
Our scoring, on every level, gives security and IT teams a measurement backed by evidence and supported by an array of purpose-built features to help streamline the remediation process, including fix recommendations, ticketing integrations, and reporting. And if you’re a security practitioner looking to take the next step and level-up vulnerability management, this is a natural and easy next addition to your Cisco Secure technology suite.
Endpoint security and vulnerability management – a unified outcome
If you’re familiar with Cisco Vulnerability Management, you may know that this isn’t our first integration with an endpoint security tool—but we do feel it’s the most exciting one. With vulnerabilities proliferating within endpoints, it’s critical for security teams to stay on top of vulnerability risk emerging via this vector. Vulnerability management has become an endpoint security necessity, so much so that endpoint security vendors are increasingly incorporating vulnerability prioritization and management capabilities we’d usually only see in traditional vulnerability management solutions. And for most of those vendors, the vulnerability management story stops there. But not for Cisco Secure.
Cisco Secure now gives customers a clear line of sight from their endpoints to the risk postures, along with the means to assess, prioritize, manage, and orchestrate remediation. And whether you’re a Cisco Secure Endpoint customer looking to advance your vulnerability management, or a Cisco Vulnerability Management customer with an active interest in endpoint security, this new integration paves the way to the ideal destination: a state of more efficient, optimized risk management.
The Cisco Vulnerability Management integration with Secure Endpoint is available today. Customers of the Cisco Secure Endpoint Advantage or Premier tiers are eligible for the integration, as well as some Essentials customers.
Interested in learning more? Request a demo or your sales representative to discuss how Cisco Secure can meet your security needs.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels