Background
The SUNBURST trojan and backdoor, as dubbed by FireEye researchers, that has compromised multiple U.S. Government systems recently, highlights the complexity and connectedness of the modern enterprise IT environment as a security weakness. Recent reporting makes clear that the adversary took advantage of software complexity to deliver a highly refined attack affecting thousands of organizations. Even with many top-tier security controls in place, the attack was able to go unobserved for months.
This blog is not to tell you deploy one product and job is done, you never need to worry about this class of threats again. It will never be that easy. Creating an enterprise software architecture that has defense-in-depth baked in through multiple layers of fortification including lateral movement control and least privilege, on the other hand, is a proven, repeatable, realistic, and implementable strategy.
In these attacks, there is always a chain of events, and the goal is to try cut at least one of those links to protect your organization. Apply least privilege and zero trust segmentation controls to break as many links as possible in your application environment. The trick is to do this without bringing any services down, requiring infrastructure changes, or frustrating application owners.
We will define actionable zero trust segmentation controls that can be applied by Cisco Secure Workload with immediate effect to protect your enterprise from the “SUNBURST” trojan and backdoor. We will also present advice on zero trust segmentation and least privilege models to help protect you on an on-going basis, as applying restrictions only to SolarWinds machines and their communication is not enough. If already exploited, the adversary has now moved laterally and the problem then becomes not only what SolarWinds can or cannot talk to, but how all application workloads communicate.
In your own environment, run a thought experiment and compute the possible ‘hops’ from a management or monitoring tool like SolarWinds Orion, to a monitored workload, to your most critical data. Chances are, without proper lateral movement control, the number will be uncomfortably low. Use Cisco Secure Workload to raise it.
Cisco Secure Workload Recommendations
In line with Cisco Talos recommendations, all organizations that use the SolarWinds Orion IT monitoring and management software are urged to follow the guidance from DHS and CISA along with the related guidance from SolarWinds to further secure these environments.
As highlighted above, initial steps involve:
- Identification of compromised/affected assets
- Applying primary mitigations including restricting network traffic to least privilege
Cisco Secure Workload can directly support both initial steps to assist in the identification of compromised assets and the application of network restrictions to control network traffic through central automation of distributed firewalls at the workload level. This flexible approach means a consistent firewall policy can be quickly applied to control inbound and outbound traffic at each workload without the need to re-architect the network or modify IP addressing and is compatible with any on-premises infrastructure or public cloud provider.
Identification of Compromised Assets
Cisco Secure Workload can identify compromised assets via three methods:
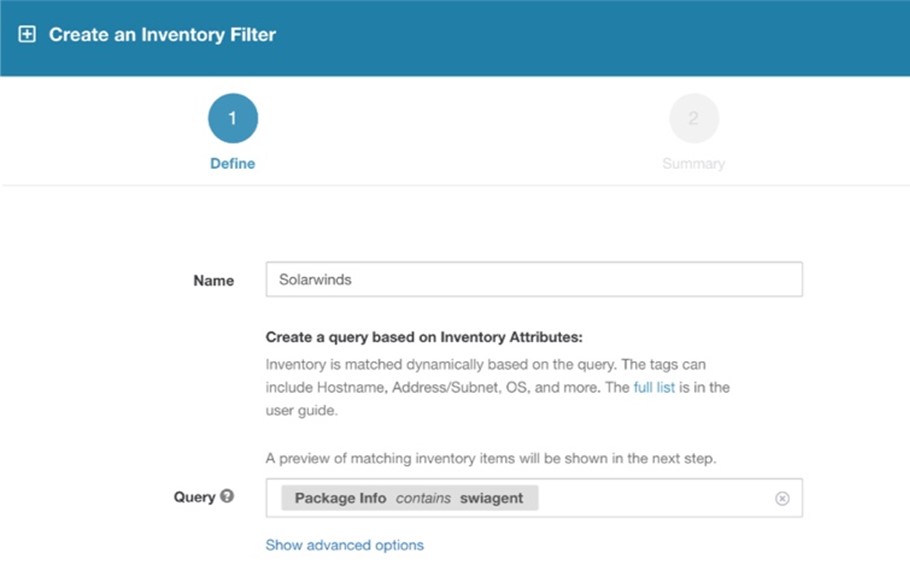
- Presence of installed package
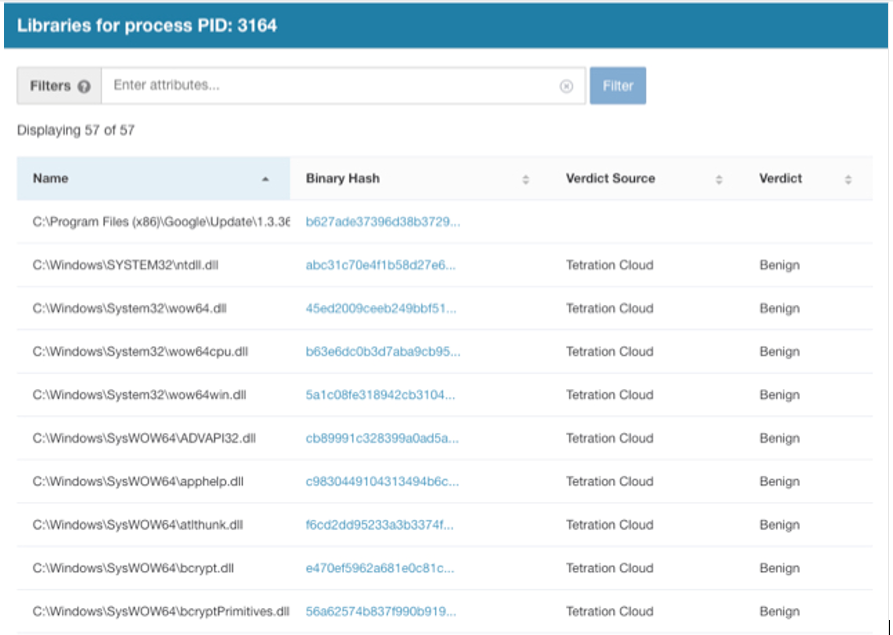
- Presence of running process (either name or hash)
- Presence of loaded libraries (DLLs)
As operator, you may choose to identify based on one or more indicators. Cisco Secure Workload will dynamically compute a list of all assets that meet the criteria defined. The list will be kept up to date and refreshed every 60 seconds to account for changes in your environment.
Fig 1 – identifying workloads with affected SolarWinds processes based on published process hash signatures
Fig 2- identifying workloads with affected SolarWinds processes based on published DLL hash signatures
Fig 3 – Identifying workloads with affected SolarWinds package installed, regardless of whether it is running in memory or not
Least Privilege Network Restriction
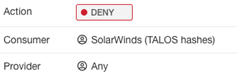
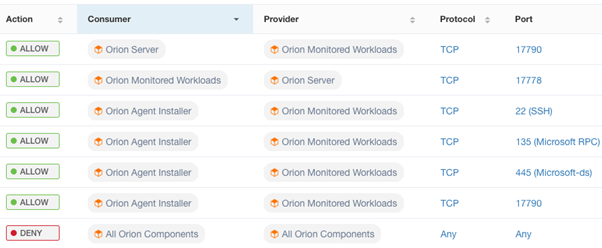
Once compromised assets have been collated, network traffic can be restricted based on a least privilege model. As operator, you may decide how much privilege to grant. In the current situation, it may be advised to provide zero privileges to all identified Orion Platform assets. In the future, as patched versions of Orion are deployed, privileges may be slightly increased, but only to cover the exact communications Orion requires for operation, and nothing more.
Fig 4 – A Cisco Secure Workload policy includes a dynamic set of source and destinations, defined here by workloads that have been detected to have SolarWinds software and an action, which in this case is to restrict any network traffic.
Fig 5 – More surgical restrictions on trust can be applied, such as removing access to the internet, users, or critical assets.
Fig 6 – The most secure state is when zero trust policies are enacted that define the expected and allowed communication patterns of an application and block all else. Communication patterns can either be ingested as published by the vendor or discovered via machine learning analysis on historical network traffic performed by Cisco Secure Workload if not available.
In the past, we were lucky to be able to conceptualize and wrangle with the complexity of our systems, but those days are gone. The complexity of modern infrastructures, and the blind spots that creates, provides opportunity for adversaries to deliver silent and sophisticated threats. For enterprises, the need for more – more agility, more features, more integrations, more value – has left us with an interwoven web of systems that are highly connected to each other, to the point that the attack surface of any one application becomes the attack surface of all, unless we are segmenting.
The above steps will help protect your organization from the SUNBURST trojan and backdoor, but don’t stop there. The most consistent guidelines and hardening measures published by government agencies and independent research bodies that is re-iterated in almost any attack – whether ransomware or supply-chain related – to help mitigate the threat, restrict the attacker, and limit propagation is to apply zero trust segmentation controls. In addition to the many benefits of implementing a zero trust segmentation control, Cisco Secure offers Cisco SecureX, a cloud-native, built in platform experience. With the Cisco Secure platform approach, you will be able to provide greater visibility, faster response and more efficient security operations. The time to act is now.