Extending the alignment to include more Cisco products
Why should you care? With so many security frameworks, it can be difficult to know where to start from. While many organizations are challenged with managing and improving their cybersecurity programs against the dynamic threat landscape, it’s not easy to pick one framework over another. So where do they start from – ISACA COBIT 5? ISO27000 series? CIS CSC? NIST CSF? SABSA? Or something else? National Institute of Standards and Technology (NIST) developed the Cybersecurity Framework (CSF) exactly for this reason. It’s a simple, best-practices approach to Cybersecurity leveraging the specific standards that are widely used and already working well today.
Basics First
NIST CSF is a voluntary framework based on existing standards, guidelines and practices for reducing cyber risks. It enables organisations to discuss, address and manage cybersecurity risk.
- It is used to manage cybersecurity risks in a cost-effective way while protecting privacy
- It references the globally accepted standards (COBIT, ISO/IEC, ISA, NIST, CCS)
- It enables all organizations (large or small) to improve security and resilience
- 3 pillars – People, Process, and Technology – Each of these are important
- Only half of the CSF Categories are addressed by technology
- It emphasizes the importance of two other main pillars of Cybersecurity – People and Process
The Cybersecurity Framework consists of three main components: the Core, Implementation Tiers, and Profiles but for today’s discussion, we will focus only on Core which is a ‘set of activities and outcomes using a language that is easy to understand.
How CSF Core makes lives easier?
The CSF Core consists of four components as shown in the table below. The CSF Core provides a set of activities to achieve specific cybersecurity outcomes. It also gives guidance on how to achieve those outcomes. The table below lists each of these components with a short description and example:
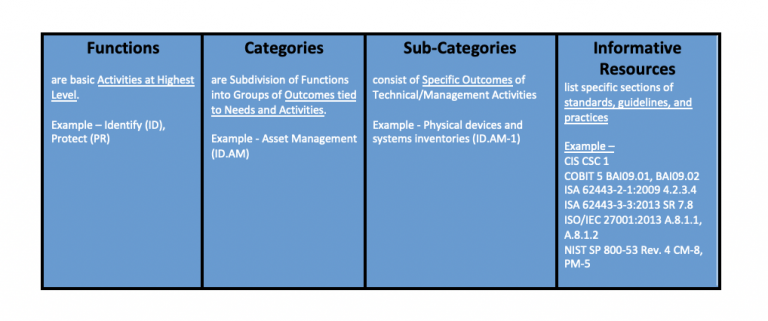
The CSF Core is comprised of five functions – Identity, Protect, Detect, Respond, and Recover. These functions when considered together, provide the lifecycle of an organization’s cybersecurity risk
How Cisco Security Products align to NIST CSF?
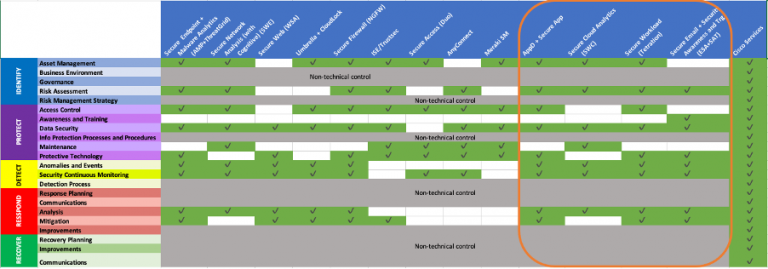
Extending the work already done with the existing whitepaper, below is the updated alignment that includes a few more products (highlighted in Orange box) and how each of these products map to different NIST CSF Categories:
So how do I use this Information?
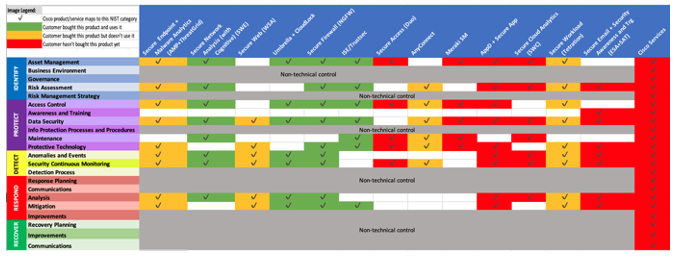
This information can be very handy while meeting a new or an existing Cisco customer. In my example below, let us assume a customer bought a few Cisco Security Products recently (as part of an Enterprise Agreement or otherwise). An image, like the one below, not only shows how each of those Cisco products map to different NIST Categories but can also illustrate where he stands with his NIST journey:
- The products he bought and uses already (Green boxes)
- The products he bought and has plans to start using soon (Amber boxes) and
- The products/services he didn’t buy and doesn’t use in this environment (Red boxes).
Resources
Cisco and the NIST Cybersecurity Framework White Paper
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels






Great blog Pranav. I’ve been looking for something like this for quite some time. It really helps us engage well with customers through the lens they look throu.gh. Thanks for sharing.
Thanks Brian!