By now you’ve likely heard of the benefits of Network Access Control (NAC) and specifically, Cisco Identity Services Engine (ISE). If not, it’s time to …how shall I put this… toss that clip-on pedometer in favor of a steps-capable smartwatch? Trade up that Motorola flip for a phone with an actual touch screen? Retire your Myspace account? You get the picture. 2005 has long come and gone, and in this day and age, segmenting traffic on your network should mean more than a separate voice and data VLAN. So, if you have any intention of passing a compliance audit that requires you prove your HVAC system is unable communicate with your point of sale terminals, then you need to implement a NAC solution. A NAC solution like Cisco ISE allows you to implement least-privilege on your network. It allows people and devices to do only what’s required for their job role or function, nothing more.
At its core, Cisco ISE is an access control server, using open standards protocols to communicate with network access devices like switches, wireless LAN controllers, and VPN concentrators, to enforce network access policy. With that said, ISE does a whole lot more than provide basic NAC functionality. It plays real nice in a security ecosystem. It is that ecosystem integration capability of ISE that we will focus on in the remainder of this post.
ISE being the brains behind network access allows it to collect, use and share very rich context. That context can come from pretty much anything ISE communicates with. Endpoints, network devices, identity stores, vulnerability scanners, threat detection tools, just to name a few. But what is the plumbing behind how this data shared? It’s called platform exchange grid, or pxGrid for short. PxGrid is a message buss that allows publishers and subscribers the ability to share context based on topics of interest. ISE is essentially the pxGrid controller.
Next question you might have is how do the ecosystem partners make use of this data? ISE can participate in 1 of 4 roles in this context sharing.
- ISE sharing context it has learned with an ecosystem partner
- ISE learning context from an ecosystem partner, then using that context in policy
- ISE taking a mitigation action on behalf of an ecosystem partner
- ISE brokering context from one ecosystem partner to another
To fully comprehend the value of this, let us dig a little deeper into these four scenarios with examples:
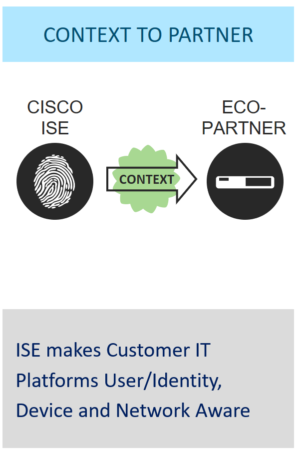
1. ISE sharing context it has learned with an ecosystem partner.
This is the most common scenario with ISE context sharing. ISE typically has most of the context, and hence it can share it with ecosystem partners allowing those systems to provide capabilities otherwise unavailable. One example of this context sharing is ISE sharing identity (username) information with Cisco Stealthwatch. This allows Stealthwatch to stitch that username with Netflow data, providing mo re useful information in its reporting and management console. Another example would be ISE sharing Scalable Group Tag (STG) information with the Cisco ASA and Firepower Next Generation Firewalls. This allows the NGFW administrators to create firewall polices based on STG instead of the traditional IP address-based rules. Which in turn allows for a magical decoupling of network addressing and access control policy. There are many 3rd party ecosystem partners such as IBM Qradar, Splunk, and Exabeam, that also make use of this endpoint contextual data.
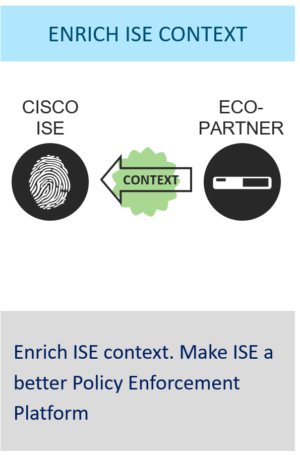
2. ISE learning context from an ecosystem partner, then using that context in policy
In this scenario, it is the ecosystem partner that is providing the context into ISE. It’s called pxGrid context-In, and it’s new with pxGrid 2.0, which was introduced in ISE 2.4. This mechanism allows ISE to consume context and enrich its policy engine, providing NAC capabilities for IoT devices. For example, ecosystem partners such as Cloudpost Networks & Medigate publish IoT asset and device information to ISE. Such is also the case with Cisco’s own IND (Industrial Network Director). Cisco IND uses pxGrid to enrich ISE endpoint database which in turn can be used to define more granular access control policy in ISE.

3. ISE taking a mitigation action on behalf of an ecosystem context from an ecosystem partner
Here is where we really start to see the value of these integrations. ISE can integrate with threat detection products and take action to mitigate a threat if detected. What this allows you to do is alter (quarantine) the network access level of an endpoint even after it successfully authenticated to the network. It’s called Rapid Threat Containment, and it works with several 3rd party and Cisco threat detection products, such as Cisco’s Firepower Management Center & Cisco Stealthwatch. Another threat mitigation flow is Threat-Centric NAC (TC-NAC). TC-NAC allows ISE to integrate with vulnerability scanning products like Qualys, Tenable, Rapid7, or threat intelligence feeds from Cisco AMP for Endpoints, and Cisco Cognitive Threat Analytics. These products will share with ISE allowing ISE to apply additional threat-related context into its existing condition library to make policy decisions. It is worth noting that TC-NAC currently does not rely on pxGrid. Rather it uses industry standard threat-sharing formats such as Structured Threat Information Expression (STIX) and Trusted Automated Exchange of Indicator Information (TAXII).
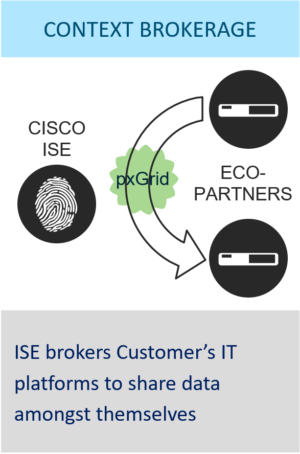
4. ISE brokering context from one ecosystem partner to another
ISE can play the role of a broker of context from one ecosystem partner to another, allowing bi-directional context sharing between ecosystem partners. Ecosystem partners can publish specific information (context) as dynamic topics. This allows other ecosystem partners that are interested in this information to subscribe to these topics. One example of such an integration is with Infoblox IP Address Management product. Infoblox publishes its IPAM table and DHCP information to pxGrid, allowing other ecosystem consumers to subscribe to that topic.
But wait, there’s more!
The pxGrid messaging framework is not the only means by which ISE can to play nice in a security ecosystem. ISE also provides a rich set of traditional REST APIs. The ISE ‘External RESTful Services’ (or ERS for short), allows for ecosystem partner integrations with or without pxGrid. These APIs are typically used for configuration and management of ISE. One example of an integration would be the with the Envoy visitor management system. A company that uses Envoy for visitor management can easily integrate it with ISE to automatically create and manage internet guest access accounts with ISE.
Lastly, ISE can consume and subsequently share identity information from an external identity source. It’s called ISE Passive ID. With ISE Passive ID, ISE gathers authentication data from numerous sources such as Active Directory, network SPAN port, syslog or even custom APIs. This data is typically a username to IP mapping. ISE then turns around and shares that context to its subscribers of the session directory pxGrid message topic. Cisco Stealthwatch and Firepower are examples of consumers of this passive identity, allowing those products to apply identity-based policy, from a consistent source
Now you’re probably wondering, where can I find out more about these ISE ecosystem partner integrations? The ISE public communities page has you covered. Simply use the short URL: http://cs.co/ise-guides to land on the ISE communities page that describes all the existing published ISE ecosystem integrations. Here is a snapshot preview of the vast set of integration guides you will find there:
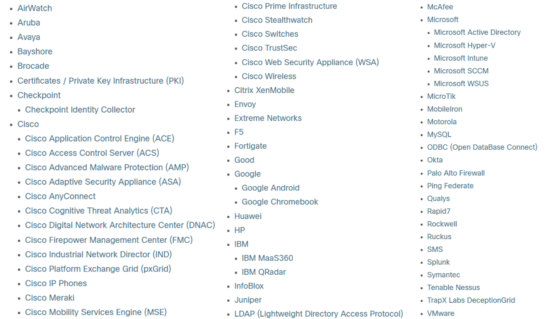
That list comprises only ISE ecosystem integrations. If you are interested in ecosystem partners for all Cisco security products, visit the Cisco Security Technology Alliance (CSTA) page. There are over 100 security ecosystem partners listed there. In addition, the Cisco Marketplace Catalog offers a search tool for searching Cisco integration for all technology architectures.
To wrap things up here I’d like to emphasize the point that Cisco ISE is more than just a NAC solution. It is a comprehensive identity management & access solution that plays very nice in the security ecosystem, allowing its user base to take advantage of many 3rd party integrations.
Credits: I’d like to thank John Eppich for his support in reviewing this post and his help providing some details around some of the 3rd party ecosystem examples.





