The world of cybersecurity never stops changing. Every day bad actors grow bolder and more devious as they try to break your security, steal your data, and offer it back to you for ransom. They’ve become very good at what they do, and they only need one small crack in your security to wreak the most havoc. There are network sentries that guard your network, but where one solution is good—two is a much stronger option.
Luckily for you, Cisco Duo and ISE are the perfect pair to protect your network.
Why are Duo and ISE better together?

Think of Cisco Duo’s multi-factor authentication (MFA) as the added layer of security that verifies a user’s identity at the time of login, like a high-tech forcefield that only lets in the good guys through—if they have their secret passcodes. Consider Cisco ISE as the intelligent cohort, analyzing everything from users to devices. Together, they provide deep visibility into the users and devices requesting access to Virtual Private Network (VPN) and Terminal Access Controller Access Control System (TACACS+), ensuring that network access is granted only to those who successfully authenticate using Duo MFA.
This blog will cover how Cisco Duo and ISE have partnered to strengthen organizational security by making the Duo MFA integration process with ISE easier for IT admins. But you can also learn about how Cisco ISE and Duo work together with our latest At-A-Glance.
What to expect from this update?
Released in November 2023, existing customers utilizing Cisco ISE with Duo no longer need to maintain an external VM or server for the Duo Authentication Proxy, otherwise known as a Duo Auth Proxy. (Duo Auth Proxy is an on-premises software service that performs primary authentication against LDAP directory, or RADIUS and then in turn contacts Duo for secondary authentication.)
This update replaces Auth Proxy with Duo APIs to prevent unauthorized users requesting confidential access to VPN network or their network access device (TACACS+).
Here is how we are enhancing integration experience for IT admins:
Making authentication workflow simpler
Cisco ISE will now handle the primary authentication and directly transmit authentication requests to the Cisco Duo cloud for secondary authentication via APIs- Auth API and Admin API, eliminating the necessity to establish an external Duo Authentication proxy.
Natively integrating and managing MFA
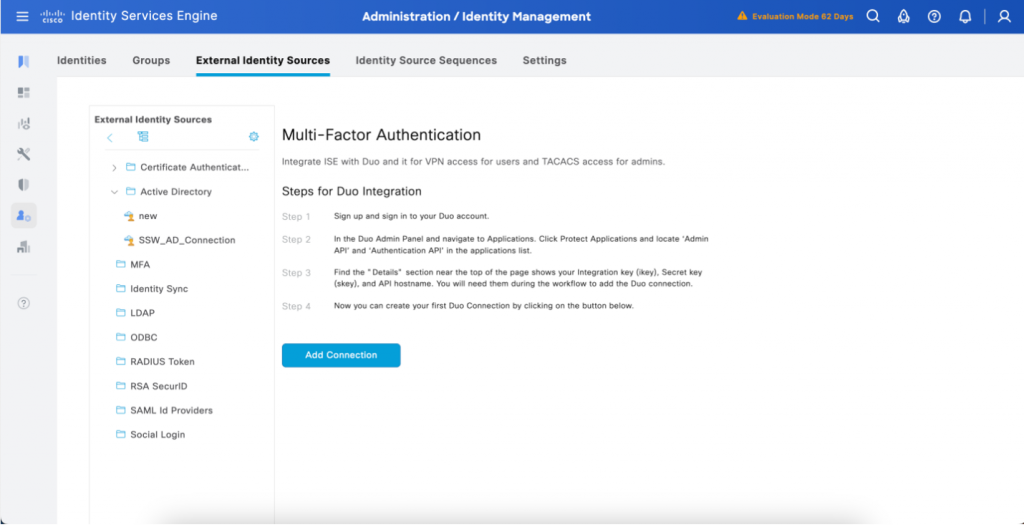
Integration Wizard: Located in the ‘External Identity Sources’ menu and under the ‘MFA’ tab.
- Now in the Cisco ISE GUI, IT admins are guided through simple step-by-step wizard to integrate ISE and Duo MFA eliminating extensive training or time required to do the task. This upgraded ISE GUI for IT admins comes without any interference to the end-user experience.
- In addition to the setup experience, directly in the ISE GUI, IT admins can also easily manage their Duo connections to re-specify which users of Active Directory groups that they would like to proceed with MFA and create policies for specific user groups.

Create your MFA Policies in the ‘Policy Sets’ Page: Located within the ISE policy tab under the sidebar
- Now in the ISE policy set page, administrators can create policies catered specifically for multi-factor authentication rules. Each rule will specify the Duo connection(s) and the conditions which must be met to proceed through the multi-factor authentication process.
Lowering IT burden and costs
A significant portion of Cisco Duo and ISE users are leveraging Duo’s MFA capabilities through the existing Duo Auth Proxy. However, as we delve into the intricacies and expansiveness of these environments, it becomes clear that many customers not only incur additional costs with deploying an appliance to host the Duo Auth Proxy but also allocate manpower to manage them. As a result of leveraging Auth and Admin APIs-
- No additional costs are incurred for external servers hosting the Duo Auth Proxy.
- IT admins can spend less time establishing, maintaining, and troubleshooting the integration and more time doing other more meaningful things.
Easier authentication workflow with Auth API and Admin API
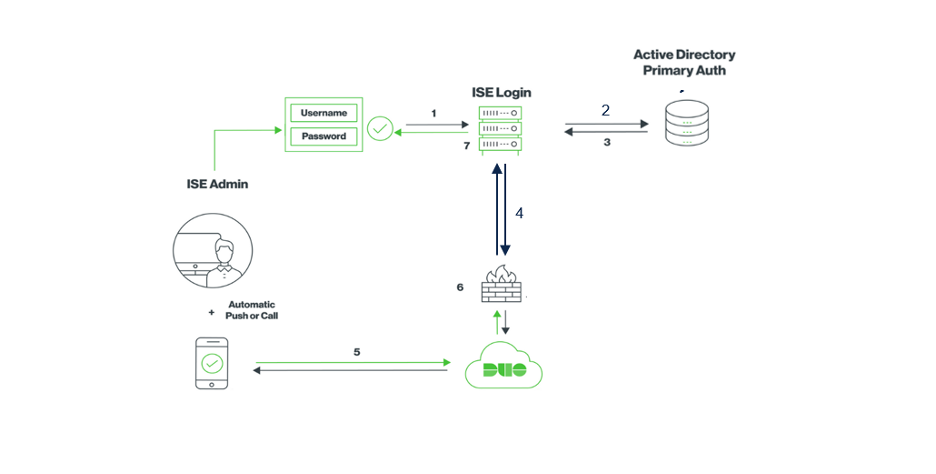
With elimination of the Duo Auth Proxy, the authentication workflow is simpler and quicker. Here is the 4 steps process for VPN and TACACS+ users:
- Admin syncs list of AD groups from ISE to Duo using the Admin API. In the case of existing groups or users, ISE only sends a list of updated ones preventing duplication.
- Cisco ISE receives a RADIUS authentication request and performs the primary authentication against configured identity source.
- Cisco ISE invokes the Auth API which allows Duo to perform the secondary authentication, or also known as MFA
- Cisco ISE upon acknowledgement from MFA acceptance from Duo grant user access to the network.
Thanks to Cisco ISE and Duo, not only can you be the leader of your network’s security solution, but also prepare your organization for authorized access with MFA, bolstering your defenses against digital threats and advancing secure authentication.
To learn more about what Cisco ISE and Duo can do together, review this At-A-Glance.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels






Fantastic information and Read!