Considering the spate of cyber threats faced by customers, the need to more easily prioritize these threats, understand the scope and veracity of the attacks, and subsequently automate the responses, has never been more critical. While many security vendors exist to address some challenges, no single technology or vendor provides the complete security customers require. Therefore, providing this extended protection often requires a collaborative ecosystem of security vendors.
Cybersecurity technology partnerships, at their core, are designed to deliver maximum value to customers by exploiting the innovative excellence of each partnering company. And this is where the Cisco-IBM collaboration becomes beneficial to customers in providing the most complete and effective security possible.
In May 2017, Cisco and IBM announced Security Partnership to address this growing global threat of cybercrime. One of our key announcements was focused on deep product integrations between our two companies. Cisco began building a new set of apps to integrate Cisco Firepower, ThreatGrid, Identity Services Engine (ISE), and Cloud Security (Umbrella and Cloud Lock) into IBM’s QRadar SIEM platform. Through these custom-built apps, QRadar would consume security information collected from the network, endpoints and cloud environments, then classify and prioritize the threats, helping security teams understand and more rapidly respond to advanced threats.
What We’ve Accomplished
In November 2017, we delivered the first app for QRadar, integrating the capabilities of Cisco Firepower into the QRadar SIEM console. Together, the QRadar + Firepower app integration delivers more streamlined and effective security to today’s digital businesses. Available via IBM’s Security App Exchange, the integration of the two provides valuable security threat information, providing a consolidated view of security events across the entire enterprise without requiring additional tools.
The Cisco Firepower App + IBM QRadar integration provides two key capabilities:
- Presents metrics and trends about the data collected buy QRadar, then displays this on the QRadar security event dashboard. Security analysts can drill down into the detailed event data for faster, more accurate threat detection and response.
- QRadar collects and parses security data into its database for analysis, allowing security teams to search, correlate, and analyze Firepower events. These events are prioritized and organized by impact flag, malware events, connection and firewall events, discovery events, and file and user events.
Delivering Outcomes
Security analysts are overwhelmed with an ever-expanding threat landscape, and limited capabilities to identify attacks in real-time. This can adversely impact their ability to escalate and prioritize the most critical threats for further action. This time-consuming task of understanding and classifying threats makes threat remediation an extremely daunting effort for even the most skilled Incident Responders.
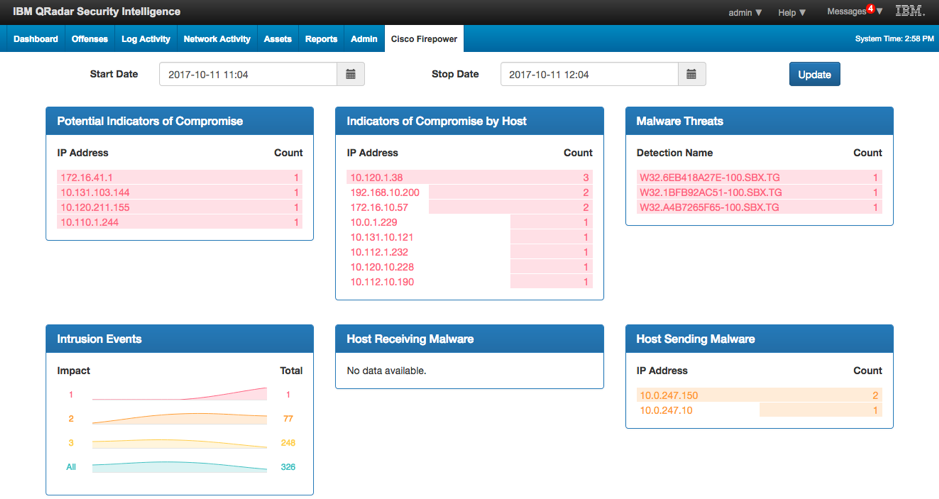
This is where the Cisco-IBM technology collaboration delivers powerful capabilities to customers. The Firepower App for QRadar streamlines investigations into critical security event information. The new Firepower app dashboard contains 6 components, as depicted in figure 1, that are all drillable to enable analysts to access the underlying data sets within a single QRadar event summary dashboard. This provides a consolidated view of all available details Indicators of Compromise (IoCs) and hosts responsible for sending or receiving the malware.
The QRadar SIEM consumes and analyzes tremendous amounts of Cisco threat data (logs, network flows) and uses analytics and context to transform it into useful, actionable information, enabling the analyst to quickly see the who, what and where behind the offense and quickly determine if it’s a legitimate threat or a false positive.
QRadar is effective at event-correlation, and threat detection and analysis as it leverages a broad range of data and applies context for greater classification. This input is ultimately integrated into a single prioritized list of offenses for further action.
This integration between Cisco Security and IBM Security enables a more extensive security architecture for greater speed and efficiency in identifying, investigating, and remediating threats. Together, we deliver the intelligence, automation and analytics required to provide data and insights that today’s security practitioners require.
What’s Up Next?
Next up, we will deliver the ThreatGrid app for QRadar to enable analysts to quickly categorize the threat level of potential malicious files that have been submitted to ThreatGrid inside their environment. Analysts can rapidly drill down from QRadar into the ThreatGrid malware analysis and threat intelligence platform for deeper analysis. This integration expedites the threat investigation process, with a dashboard view into the highest priority threats, delivered directly through QRadar versus having to pivot through disparate tools and interfaces.
Additionally, we are working to extend the reach of QRadar into our Identity Services Engine (ISE), Cisco Umbrella and Cloud Lock. This integration will provide joint customers deeper analysis to more efficiently identify anomalous threats that could indicate a security risk.
This partnership of two strong security companies will enable customers to secure their business outcomes with the most comprehensive security possible. For more information, please download our FAQ and visit our Cisco-IBM site.