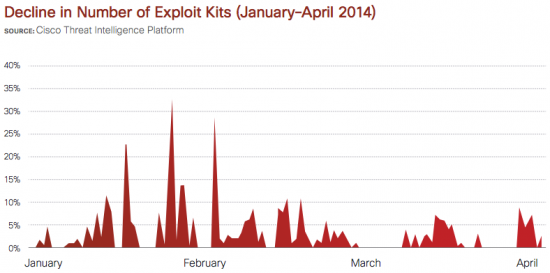
Even in the world of cybercrime, when a top “vendor” drops out of the market, competitors will scurry to fill the void with their own products. As reported in the Cisco 2014 Midyear Security Report, when Paunch—the alleged creator and distributor of the Blackhole exploit kit—was arrested in Russia in late 2013, other malware creators wanted to fill the gap.
“Blackhole” and its more expensive brother “Cool” were the most widely used and well-maintained exploit kits. After Paunch’s takedown, we observed that many other exploit kits, including Fiesta and Neutrino, became more active in the market. However, a clear leader has yet to emerge.
While there’s more competition in the exploit kit market, it’s not translating to a greater number of deployed kits, as Cisco research shows. In fact, the total number of active exploit kits has dropped dramatically—by 87 percent—since Paunch’s arrest.
Our researchers also have seen a growing number of attackers using exploit kits aimed at specific users or industries. This is in line with the trend Cisco has observed in recent years in many areas of malware development, where adversaries are seeing greater rewards by targeting their malware.
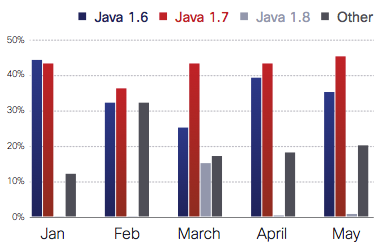
As we discuss in the 2014 Midyear Security Report, exploits involving Java remain popular. In the Cisco 2014 Annual Security Report, we noted that Java exploits represented 91 percent of indicators of compromise (IOCs) in November 2013; these Java-related IOCs rose to 93 percent, as of May 2014.
Exploit creators seem to favor older versions of Java, particularly Java 6 and 7. Cisco researchers saw a surge in web malware encounters with Java 8 in March 2014, which is when the new version of the programming language was released. However, encounters for Java 8 dropped off noticeably in April and remained very low through May. We are now seeing a shift to an increase in exploit kits that rely on non-Java vectors, such as Microsoft Silverlight, and our security researchers predict that we may see a shift away from Java 8—which has stronger security controls—to other software that can be exploited more easily.