Co-authored by Tejas Sheth, Sr. Security Specialist, Amazon Web Services – AISPL.
Risk-based Vulnerability Management (RBVM) represents a strategic approach to cyber security that focuses on identifying and prioritizing vulnerabilities based on the potential risk they pose to an organization. This approach builds upon traditional vulnerability management, which often involves scanning for and patching all vulnerabilities without considering their actual impact on the business. In RBVM, vulnerabilities are evaluated based on factors like the criticality of the affected system, the sensitivity of the data involved, and the likelihood of exploitation by threat actors. In doing so, organizations can more effectively prioritize vulnerabilities to focus on the risk the matters most in their environments.
In this blog, we’ll show you how you can ingest your cloud-specific vulnerability findings from Amazon Inspector into Cisco Vulnerability Management for a consolidated, risk-based approach to effectively address vulnerabilities.
First, let’s introduce you to both solutions and the value they bring.
Amazon Inspector
Amazon Inspector is a security assessment service designed to help AWS customers improve the security and compliance of their applications deployed on AWS. It automatically assesses applications for vulnerabilities or deviations from best practices. After performing an assessment, Amazon Inspector produces a detailed list of security findings prioritized by level of severity. These findings can be integrated with other services for in-depth vulnerability analysis and management, enabling AWS users to take actionable steps towards remedying potential security issues.
Amazon Inspector calculates its unique Inspector Score based on a variety of factors beyond the Common Vulnerability Scoring System (CVSS). This includes assessing whether the network is reachable from the internet, the CVSS score itself, and other proprietary parameters. which provides a numerical score reflecting the severity of a vulnerability based on its intrinsic qualities, the Inspector Score also considers the context of the AWS environment to prioritize issues more effectively.
Details provided by Amazon Inspector include:
- Mapping of findings to MITRE ATT&CK techniques (TTPs),
- Evidence details,
- Information on known malware,
- References to CISA advisories,
- Resources affected,
- Remediation steps, and
- Affected packages.
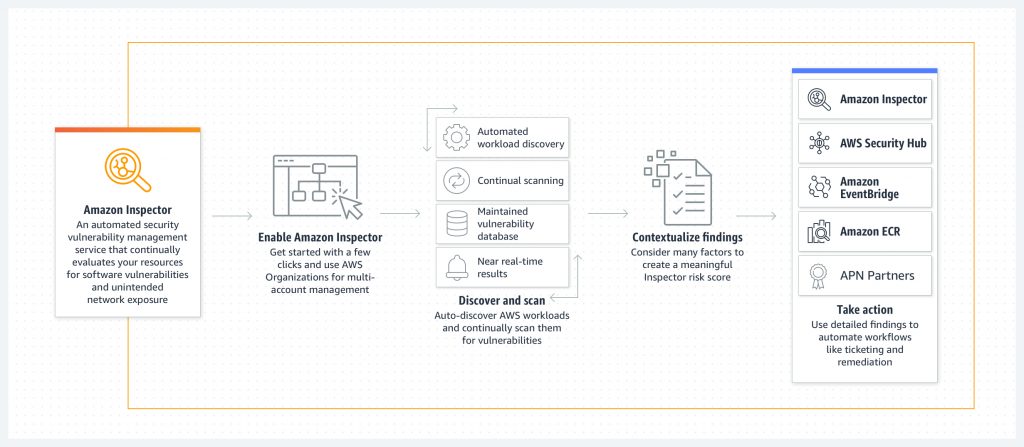
Amazon Inspector also supports the export of Software Bill of Materials (SBOM), CIS (Center for Internet Security) benchmark scanning for EC2 instances, and offers scanning capabilities for AWS Lambda, container images in Amazon Elastic Container Registry (ECR), and Amazon EC2 instances without the need for agent installation or manual intervention, enhancing the security posture with minimal overhead.
Cisco Vulnerability Management
Cisco Vulnerability Management, a risk-based vulnerability management SaaS solution, prioritizes vulnerabilities that pose a real risk, enabling Security and IT teams to focus their limited resources on what matters most for efficient remediation and risk reduction. With risk scoring powered by data science—machine learning and patented approaches to predictive modeling—Cisco’s prioritization evaluates both enterprise data and a wealth of data on real-world exploit activity and then translates that context into actionable intelligence to guide remediation decisions and resource allocation. Data from tools like Amazon Inspector can be easily ingested into Cisco Vulnerability Management for a holistic approach to risk-based prioritization.
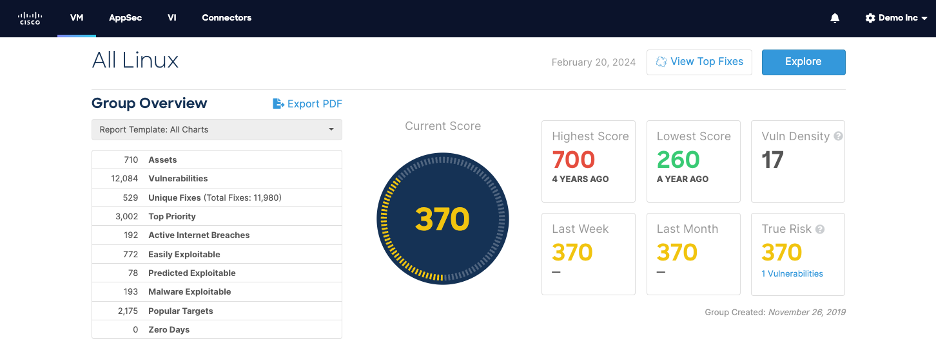
Cisco Vulnerability Management uses threat and exploit intelligence from 19+ feeds, including Cisco Talos, and uses the only dataset on volume and velocity of exploitation in the wild. These data sources build a machine learning model for vulnerability risk. This model is then combined with asset criticality that can be pulled automatically from a CMDB or manually inputted by a user, the asset’s position in the network, and the patch level aggregation to provide recommendations, risk assessments, and measure risk over time on the vulnerability, asset, and group of assets level.
Using the Amazon Inspector Toolkit Connector for Cisco Vulnerability Management
When Amazon Inspector asset and vulnerability data is ingested into Cisco Vulnerability Management, it enhances the vulnerability management process by integrating cloud-specific security insights into a broader vulnerability management strategy. Through this integration, organizations can take advantage of:
- Data Aggregation: Amazon Inspector’s findings, which include identified vulnerabilities and their details, are imported into Cisco Vulnerability Management. This process consolidates data from various sources, including cloud environments, providing a unified view of security vulnerabilities across the organization’s infrastructure.
- Risk Analysis and Prioritization: Cisco Vulnerability Management applies its risk-based vulnerability prioritization approach to the ingested data from Amazon Inspector and other sources. This means it assesses and prioritizes vulnerabilities based on various factors such as the severity of the vulnerability, the exploitability, the criticality of the affected asset, and the presence of known exploits in the wild. This prioritization helps in focusing remediation efforts where they are most needed.
- Actionable Insights and Remediation Guidance: Cisco Vulnerability Management offers actionable insights and guidance on how to remediate identified vulnerabilities. It provides context and intelligence that helps security teams understand the potential impact on each vulnerability and the best steps to mitigate them.
Guided Steps on Configuring the Integration
The Amazon Inspector toolkit is a set of functions for data and API scripts you can use with the Cisco Vulnerability Management platform. It’s organized into tasks—units of functionality that can be called and used from the command line.
Step 1
Pull the latest image available on Docker Hub. See Running The Latest Image section for exact set of commands to perform this task.
Step 2
To bring in asset and vulnerability data from Amazon Inspector, start by running the Docker image with AWS Inspector as task and providing the correct AWS authentication method. This integration supports several kinds of authentication methods provided by AWS SDK. You can find the list of supported authentication methods under AWS Authentication.
The below command is an example of running the Docker image with task as AWS_inspector2 and using IAM roles for authentication:
docker run -v ~/.aws:/root/.aws –env AWS_REGION=us-east-1 –env AWS_PROFILE=inspector_test –rm -it toolkit:latest
task=aws_inspector2 aws_role_arn=”\”arn:aws:iam::123456789012:role/Inspectorv2ReadOnly\””
Step 3
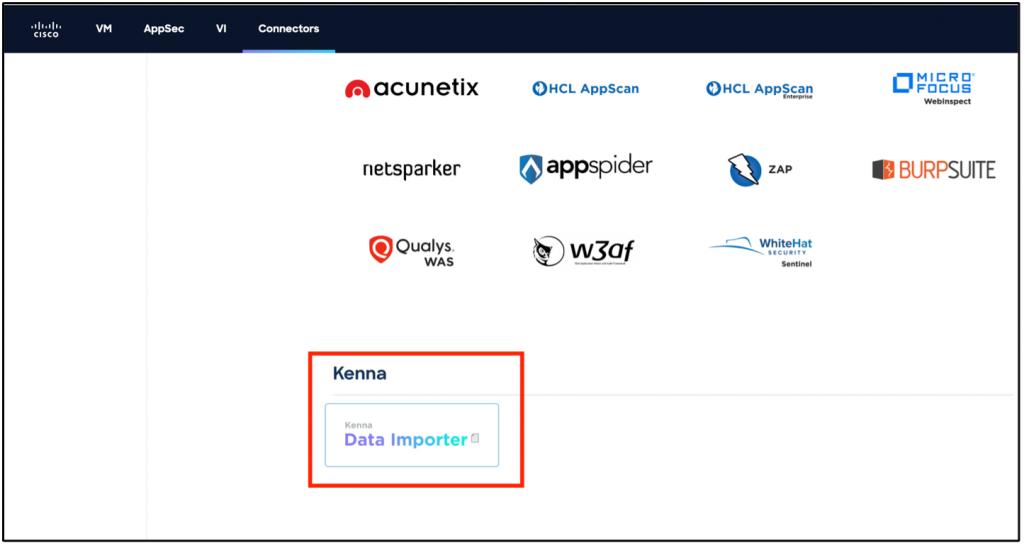
Click the Data Importer connector under the Connectors tab in Cisco Vulnerability Management:
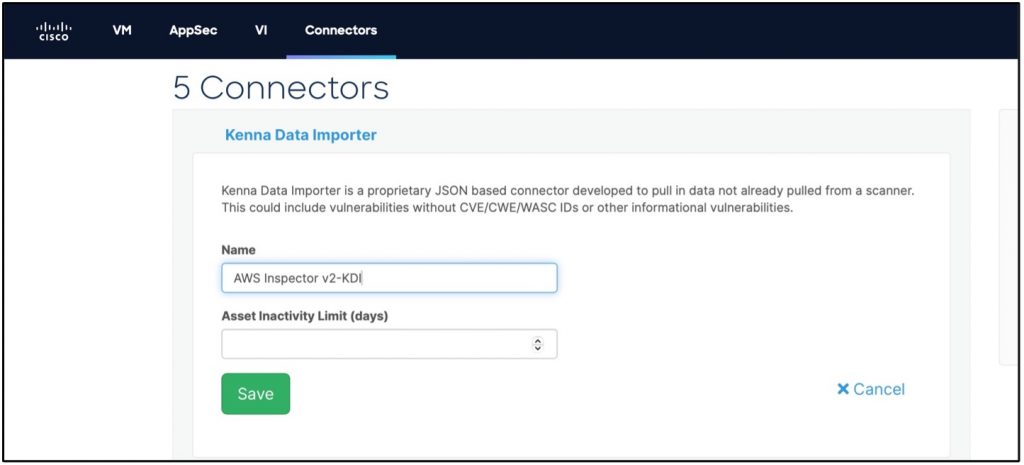
Create the connector by adding a Name and Asset Inactivity Limit and click Save:
Step 4
If you leave off the Cisco Vulnerability Management (formerly Kenna) API Key and Connector ID in step 2, the task will create a JSON file in the default or specified output directory. You can upload the JSON file manually to the connector created on the UI in Step 3 to verify the resulting data and diagnose any issues with the JSON file.
Step 5
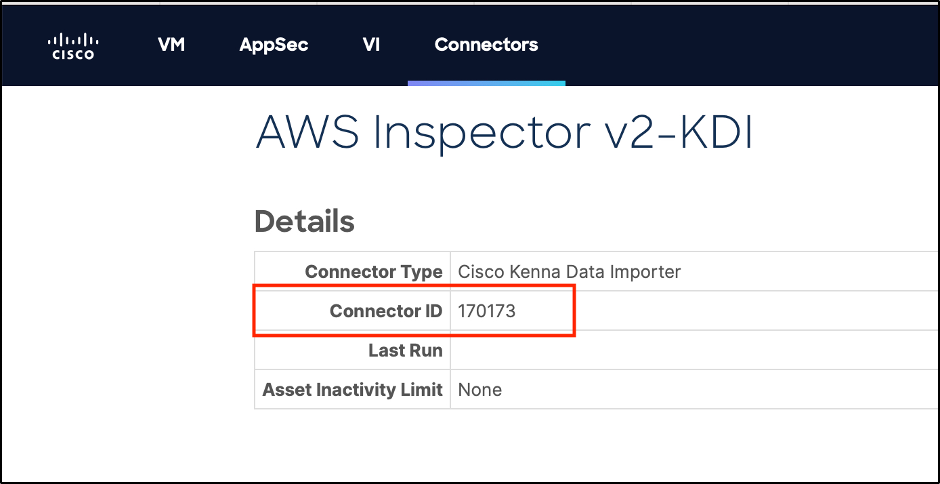
Click into the newly created Connector and record the Connector ID (this Connector ID is needed for Step 7):
Step 6
In previous steps, we manually uploaded the JSON file on Cisco Vulnerability Management. Now, we can automate this process through the Command line using Cisco Vulnerability Management API Key and Connector ID. To generate an API Key, follow these steps.
Step 7
Run the task with your Cisco Vulnerability Management (formerly Kenna) API Key & Connector ID (IAM role authentication is used in the command below).
docker run -v ~/.aws:/root/.aws –env AWS_REGION=us-east-1 –env AWS_PROFILE=inspector_test –rm -it toolkit:latest
task=aws_inspector2 kenna_api_key=$KENNA_API_KEY kenna_connector_id=12345 aws_role_arn=”\”arn:aws:iam::123456789012:role/Inspectorv2ReadOnly\””
For more details, check out this connector task on GitHub. Note: The task currently only handles package vulnerabilities, not code vulnerabilities (in AWS Lambda) or network reachability findings. Suppressed findings in Amazon Inspector don’t exactly map to “risk accepted” or “false positive” in Cisco Vulnerability Management, so they are treated as open vulnerabilities.
Ready to get started?
Reach out to your Cisco representative today to learn more about ingesting data from Amazon Inspector into Cisco Vulnerability Management for a consolidated view of risk and effective prioritization.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels





