Anyone who has been involved with compliance knows that simplifying complexity is the key to maintaining a secure and compliant organization. It’s become quite apparent that sustaining compliance is a marathon, and the journey must be travelled with vigilance. This is not something that is an endpoint or a task, that once accomplished, can be shelved and forgotten; therefore, it is very helpful for merchants, who wish to become compliant or maintain compliance, to purchase solutions that are “certified.”
The fact that you are purchasing a product that’s already been validated as secure and “capable” of being compliant reduces the complexity and uncertainty associated with big-ticket items. Adding new credit card readers or a payment application in your stores is expensive, and knowing that these products are validated by the Payment Card Industry (PCI) Council gives merchants confidence that they’re making a wise and secure decision. 
![]() But certification within the realm of payment compliance exists only within two of the three branches of PCI. Both the Payment Application Data Security Standard (PA-DSS) and PIN Transaction Security (PTS), such as credit card readers, have lab certifications that must be attained in order to be sold into a compliant environment. What about the rest of the infrastructure? When it comes to the majority of the technology specified within PCI, there is no certification. If there is no certification for infrastructure technology such as firewalls, intrusion systems, wireless access, routers, switches, and load balancers, how are merchants able to ascertain that they’re making equally wise and secure decisions when purchasing products that must be capable of enforcing the PCI Data Security Standard?
But certification within the realm of payment compliance exists only within two of the three branches of PCI. Both the Payment Application Data Security Standard (PA-DSS) and PIN Transaction Security (PTS), such as credit card readers, have lab certifications that must be attained in order to be sold into a compliant environment. What about the rest of the infrastructure? When it comes to the majority of the technology specified within PCI, there is no certification. If there is no certification for infrastructure technology such as firewalls, intrusion systems, wireless access, routers, switches, and load balancers, how are merchants able to ascertain that they’re making equally wise and secure decisions when purchasing products that must be capable of enforcing the PCI Data Security Standard?
What are the security capabilities required to measure these products?
Sound complicated? It’s not.
Cisco has done it for you!
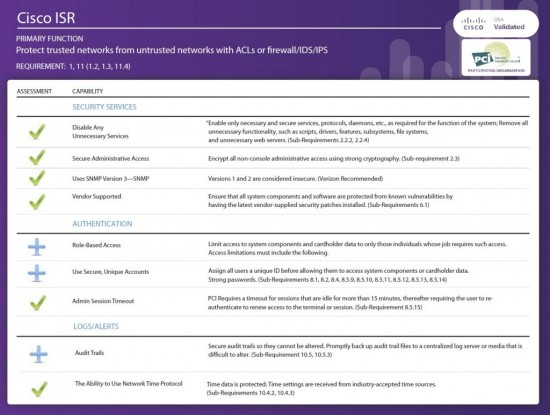
The Cisco Compliance Solutions team has worked with a global qualified security assessor, Verizon Business/Cybertrust, to develop a simple metric for reducing the complexity around the capabilities needed to support PCI. This capability metric also helps vendors like Cisco develop secure products that maintain compliance. The logic was pretty simple, actually. The process involved analyzing every sub-requirement within the standard that stated a service capability. For example, PCI DSS Requirement 8 talks about the need for unique IDs for administrator accounts. PCI states that you can’t use general administrator accounts because it would be unclear who executed a command that resulted in a breach. Okay. So each piece of technology that is in scope has the capability requirement of using unique IDs. PCI DSS Requirement 10 states that technology must have time synchronization using Network Time Protocol (NTP). Okay. So each piece of technology must be able to use NTP. Get the idea? All of these requirements are grouped into logical buckets for simplification. The result is following:
Each of the capabilities listed on our “scorecard” can now be applied to any piece of DSS technology that you want to deploy. In fact, this is the very method that is used in the Cisco Compliance Solution for PCI DSS 2.0 for all Cisco and partner products. For more details on the scorecard capabilities, see Chapter 5 of the Cisco Compliance Solution for PCI DSS 2.0 Design and Implementation Guide. This guide can be used to ensure that any product you purchase for your PCI environment meets these criteria.
Happy Compliance Journeys!