Macro malware is a good example of malware writers and distributors using old tricks that most users have forgotten to spread malware. Unlike earlier macro malware, these macros don’t infect other documents but download password stealing trojans and install them on targets. Macro malware typically arrives via email with an attachment that contains a macro-based phishing attack in the form of an MS Office document (usually Word or Excel). The malicious code is written using the older Visual Basic for Applications (VBA) scripting language.
What makes the current versions of macro malware particularly dangerous is that the code is often heavily obfuscated, making detection difficult. Furthermore, once the document is opened and macros are enabled, the malware installs and begins to monitor Internet Explorer, Chrome, and Firefox browser activities with the capability of grabbing screenshots and logging keystrokes. The attacker’s ultimate goal is stealing these login credentials that give access to corporate and financial data.
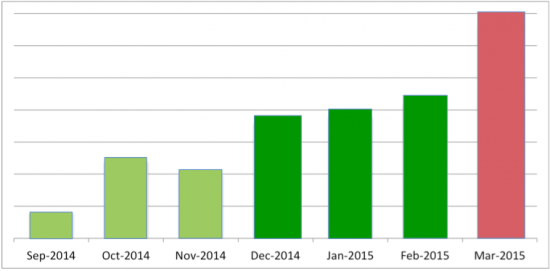
Distribution of malware by email using malicious Word and Excel files containing macros is on the rise. Popular malware used by cyber criminals including Dridex, Vawtrack, Betabot, and Rovnix have been distributed using this tactic. Based on data analyzed by Cisco Managed Threat Defense Team, email attacks where macros are the method of infection are up 50% from February and have more than doubled since October of last year.
Email Attacks per Month
Cisco Managed Threat Defense (MTD) analyzes thousands of email attachments each day in order to protect customers and gather new threat intelligence.
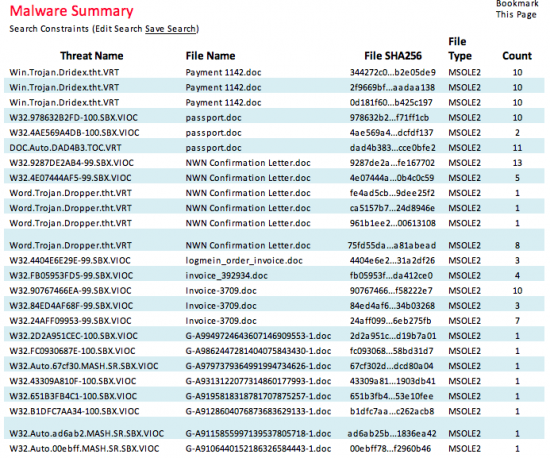
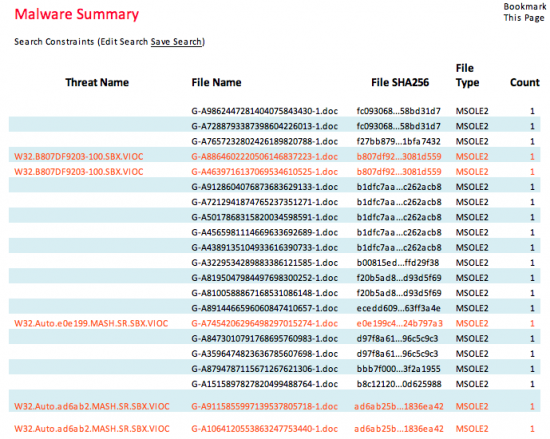
Our investigators use search criteria based on past attacks and current threat intelligence to find email attachments of size, type, and name that are likely to be malicious.
Analysts look for groups of files with the same or similar names and certain types of documents known to be used for delivering malware. These customized “hunts” based on threat intelligence from past attacks, attacks on other customers, Cisco Threat Intelligence Platform (TIP), and Information Sharing and Analysis Center (ISAC) organizations identify new attacks like those shown below:
These files with similar names and sizes arriving around the same time turned out to be messages with malicious attachments being sent out using a spambot.
* Filenames in red were detected as malicious at the time they were delivered
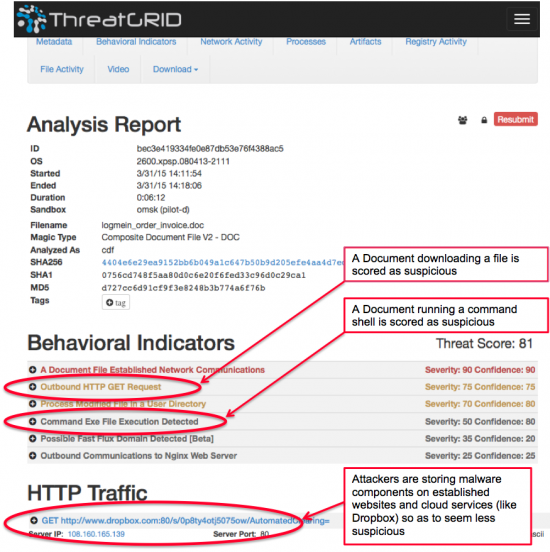
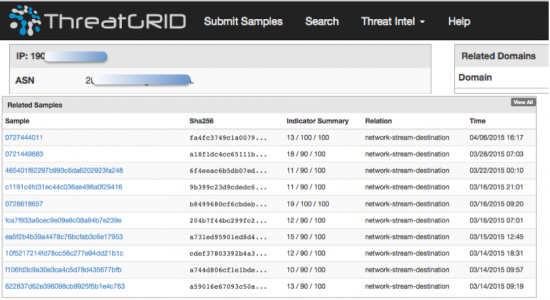
At the time of delivery, detection of malware in the email messages is low. MTD analyzes samples from each campaign to determine if they are malicious. Investigators use Cisco ThreatGrid and FireAMP malware analysis technology to determine file activity, network activity, and Windows registry activity of each sample.
Activities determined to be malicious are scored and a total threat score is computed. Cisco ThreatGrid also compares the current sample with similar samples already analyzed and compares the network activity and file activity with those that have already been analyzed. This allows analysts to connect similar attacks or attacks where similar network activity occurs when the malware runs. MTD has found some malware components on compromised legitimate websites and cloud services such as Dropbox or Google Drive. Attackers are using these sites because connections to them won’t seem suspicious and are unlikely to get blocked by a domain.
Multiple malware samples using the same IP address for communication
Cisco ThreatGrid allows analyzing new malware and new threats even if antivirus does not detect them at all. MTD finds new command and control servers and malware download sites with each email investigation. MTD customers are notified of IPs to block or domains to sinkhole so that infections are prevented even if antivirus doesn’t detect the malware variant. Blocking malware download sites prevents infection even if the email is opened days after it is first delivered.
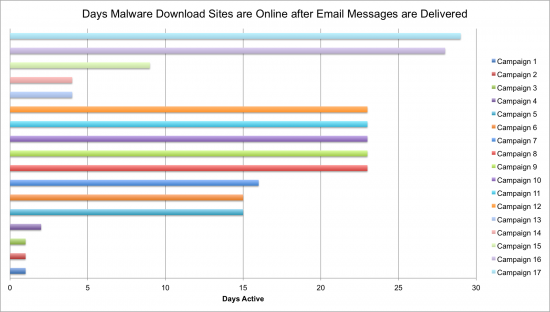
Malware download sites used by macros can be active for 29 days or more
While some sites hosting malware payloads are taken down quickly, a surprising number are not. MTD research found that some malware stays online for 29 days or more and malicious payloads stay online for an average of 14 days after the malicious email using them was delivered. This means a user could still get infected if they opened an old email attachment containing a malicious macro 29 days after it was delivered.
The chart above is based on malware sites used in malicious macro attacks in the last 30 days. For the most part, each campaign uses new domains and IPs for the payload download and the malware callbacks. MTD research found that 5% of the time, a domain or IP was re-used across multiple attacks.
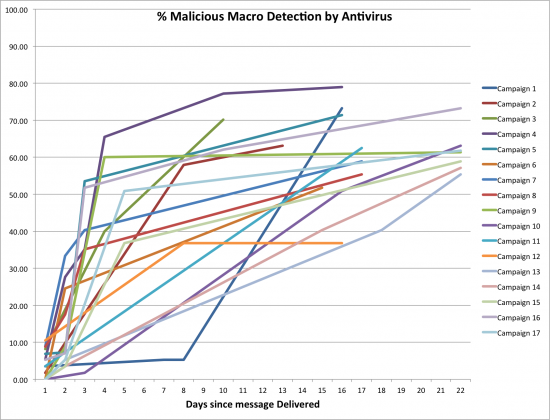
At the time the emails are delivered, detection of malicious attachments by antivirus ranges from 0 to 35% with the average being 8%.
Why is detection so difficult?
First of all, the attachments are Office documents, which are unlikely to be blocked by filetype at the email gateway. Zip file attachments are used to deliver executable files and may be blocked by policy, but it would be unusual for .DOC and .XLS files to be blocked. Thus, antivirus software or some other security control must be used to detect malicious macro downloaders. Macro downloaders have been evolving since they reappeared in the wild mid-October 2014. A simple measure of the macro obfuscation is the number of lines in the macro. The first samples seen had an average length of 150 lines. The malicious macro downloaders seen in the wild in March 2015 have an average length of 1500 lines. The first samples seen had random strings throughout in comments. It was easy for attackers to vary the comments and keep the macro script the same. This was done to evade detection using the file hash.
The latest macros have randomness in the comments as well as other methods for avoiding detection such as:
- Malicious macro email attachments may detect virtualization and exit
- Malicious macro email attachments may detect sandbox analysis and exit
- Malicious macro code obfuscation is increasingly complex and now includes:
- Random strings in variables that are never used
- Randomly named functions that are never called
- Malicious macro code now uses basic encryption techniques to hide the shell commands such as:
- Character string substitution such as replacing all T’s with Z’s
- Character transforms such as reversing a string
- XOR encryption using a key stored in sections in the macro
The sandbox detection and evasion is fairly basic, but effective in many cases. Example detection methods include running the macro downloader when a document is closed (using auto_close) rather than when it is opened (using auto_open). If a malicious macro using auto_close() is opened in an automated sandbox for analysis, it would not be closed and the malicious parts of the downloader would never run, be analyzed, or detected.
The newer macros make use of Powershell or other scripting languages to check Windows components such as the services list. By enumerating the service names and looking for VMWare, Vbox or Virtual in the service names, a macro can determine it is running in a virtual environment and exit. Macros can detect sandboxes by checking the serial number of the system drive, the Windows Product ID or the date when Windows was installed. Just before this post was made, a new tactic was observed where malicious .DOC files were placed inside other documents and attached to an email. For example a .DOC inside an .XLS spreadsheet or a .DOC inside a PDF. These embedded documents contain the malicious macros and present a challenge to analysis by traditional sandboxes.
Early macro malware displayed a blank page when opened and this would seem suspicious to the wary user opening an email attachment. In January 2015, attackers started using decoy documents. These documents are displayed while the infection routine runs in the background leading the user to think the document opened normally and was not malware. The decoy documents seen so far are spam ads leading the user to think they opened annoying but harmless spam when in fact their computer is getting infected.
These threats are stealthy and use social engineering rather than exploits to trick users into thinking they are safe since they appear to be data documents. Attackers are staying away from known spammy messages such as pharmaceuticals or casino spam to avoid being blocked by spam filters. Instead, the messages are business related: fake invoices, fake receipts, fake fax or voicemail messages, fake reports, or fake purchase orders.
Lessons Learned:
- Because Office documents are seen as data and not applications, malicious macros have once again become a delivery mechanism for malware
- There has been a 50% rise in threats delivered via email since November 2014
- Payloads of malicious macro downloaders can remain online for weeks in some cases
- Attackers are evading security controls by using scripting languages such as VBScript, Cscript, DOC batch script, and Powershell in malware downloaders
- Attackers are using legitimate sites like pastebin.com and dropbox.com to host malware, making blocking by domain difficult
Macro malware is a good example of malware authors adapting to increased security measures such as blocking .ZIP email attachments that contain .EXE files. Threat actors continue to evolve tactics, techniques, and procedures and defenders must continuously focus on threat detection and mitigation at all stages of the cyber kill chain. Obtaining actionable threat intelligence is key to maintaining a strong security posture and has been proven to prevent security incidents. By analyzing each attack as it comes in, MTD is developing threat intelligence for use in improving perimeter defenses.