We recently announced the release of AsyncOS 9.5 for Cisco Email Security that included the integration of AMP Threat Grid. Now if Threat Grid could talk it would sound a lot like Ron Burgundy and say “I’m not sure if you know this, but I’m kind of a big deal.” Email is consistently one of the top two threat vectors for malware because so many people out there still open an attachment that looks harmless from someone they don’t know. We all want to think we won a cruise, but that’s not how it works. It’s how malware establishes a foothold on your system. AMP Threat Grid is there to make sure this doesn’t happen.
Cisco acquired Threat Grid to not only bolster its suite of advanced threat solutions, but to also integrate the technology into its advanced malware protection (AMP) products. AMP Threat Grid goes far beyond traditional sandboxing, providing a host of analytical engines to evaluate potential malware. From static and dynamic analysis to various post-processing techniques, AMP Threat Grid evaluates malware to provide the most comprehensive report for even the most junior security analysts. This video provides a more comprehensive overview. Those familiar with Cisco’s Email Security know we already had a sandbox built in and may ask ‘Why change?’ and that’s exactly the question you want to ask. There are really three key reasons:
- Proprietary Analysis: Today’s malware authors write code to detect if their malware is being analyzed in a virtual environment, some even checking specifically to see if they are in many of the popular open-source sandboxes. If the malware detects it is inside a sandbox, it won’t run, rendering the analysis worthless. AMP Threat Grid even looks for this type of behavior:

- Outside Looking-In Approach: Most malware analysis platforms have some sort of hook inside the virtual environment that gives away their presence, whether it’s the age of the operating system or specific virtual machine properties. AMP Threat Grid lacks instrumentation inside the sandbox, thus evading detection by the malware.
- Full Ownership: We own the database and infrastructure – no relying on outside support. This means we can better serve our customers, and ensure the privacy and data protection they require. This is especially crucial to reducing the total cost of ownership (TCO) for customers.
However, what if you want to take this a step further and improve your end to end visibility? Whether as an on premises appliance or a cloud based subscription, AMP Threat Grid was designed and built to be integrated with existing security technologies and to be automatically fed with samples thanks to its powerful REST API. This makes it incredibly easy and cost effective to scale the technology from being the back end analysis engine for your email security and increase visibility from the edge to your endpoints. We’ve integrated AMP Threat Grid with solutions such as Fidelis, RSA Security Analytics, Tripwire Enterprise, Guidance Software EnCase, BlueCoat, and Tenable Security to name a few.
Ease of Use
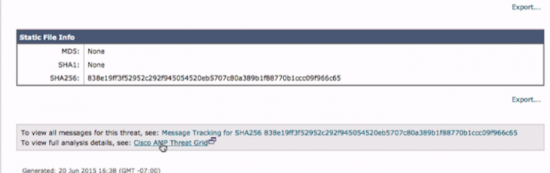
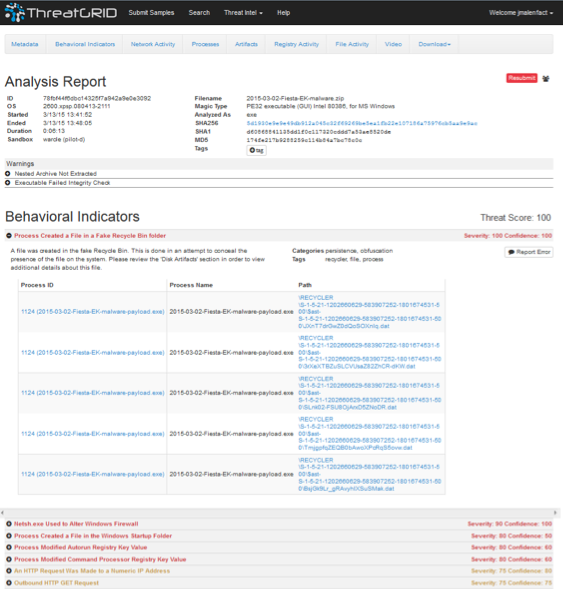
AMP Threat Grid has a clean, easy to use dashboard that empowers Tier 1 analysts, and provides the deep level of content that Tier 3 analysts look for. This may sound obvious, however, sandboxes are actually really great research tools. Unfortunately junior analysts tend not to have the experience to understand sophisticated malware. The integration of AMP Threat Grid with Cisco’s email security allows junior analysts to pivot directly from email security to the AMP Threat Grid portal, as shown here:
The AMP Threat Grid portal provides a Threat Score and easy to read behavioral indicators that very simply spell out why something is bad, helping them make more accurate decisions faster. This is where analysts can dive into the analysis, interact with the malware samples in GloveBox, find if a suspicious sample is actually communicating with known bad IPs or Domains, download the artifacts it created and submit those, and so much more!
For more information on AMP Threat Grid visit www.cisco.com/go/amptg or feel free to leave a comment below!






nice post.