By Timothy D. Harmon, M.S., CCNA R&S, Security+CE, Cisco Champion
Cyber security is a high priority of companies, small and big, as cyber attacks have been on the rise in recent years. In response to these attacks, security professionals and college students have been through rigorous training as how hackers are able to get into the companies and how to defend against them. One way of cyber security training is through a cyber security capture the flag (CTF) event. A cyber security CTF is a competition between security professionals and/or students learning about cyber security. This competition is used as a learning tool for everyone that is interested in cyber security and it can help sharpen the tools they have learned during their training.

The very first cyber security CTF developed and hosted was in 1996 at DEFCON in Las Vegas, Nevada. DEFCON is the largest cyber security conference in the United States and it was officially started in 1993 by Jeff Moss. DEFCON had become a platform for a skills competition and as the Internet grew, both DEFCON and the CTF competitions did as well. CTF competitions have become global as they did not have any borders and can be done via the Internet. International teams were competing for different types of prizes and bragging rights. There are two formats of the cyber security CTF: attack-defend and Jeopardy-style.
The attack-defend CTF is where each team attacks the other team’s system, as well as defend their own system. Usually, there are two rounds of game play in which one team is the attacking team and the other team is the defending team in the first round and then they switch for the second round. There are flags (text files, folders, images, etc.) in the defending machines that the attacking team attempts to find as they compromise the machines. The attacking team is able to use different hacking tools in order to compromise the defending machines but there are rules in place to ensure that the teams are not at an advantage over the other. The defending team can do anything within the rules to defend their machines against the attacking team. They are not allowed to disable any network connections or turn off the machines. If there is any rule violation, the team will incur a penalty or be disqualified.
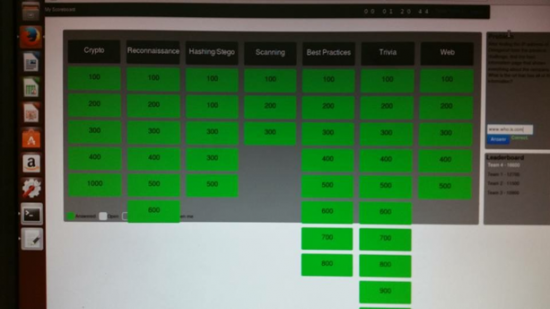
The Jeopardy-style CTF is similar to the actual Jeopardy game as the scoreboard looks like a Jeopardy board with different categories and point values. There can be more than two teams as the teams are not trying to attack each other. Some of the categories can include Cryptography, Steganography, Physical Security and Scanning. There are several other categories that can be used. Some of the challenges can be done against a main server that was developed for the CTF and the flag is inputted into the CTF scoreboard to get points for the team. A timer is used to start and stop the CTF and once the timer finishes, the game is over. The team with the most points at the end wins.
As mentioned before, CTFs are now global and can be online or in the same geographical area. Open Web Application Security Project (OWASP) San Diego would usually do a Jeopardy-style CTF once a year that participants are able to learn how to pick locks and use other tools to complete the CTF competition. The National Cyber League (NCL) is another CTF that is for students and faculty of universities and the NCL can be used as a curriculum in order to teach the students about cyber security. There are several other CTFs that are available and can be found on the CTFTime website.
I have participated in the 2015 OWASP San Diego CTF and the 2015 National Cyber League’s Fall Season. Both of these CTFs have given me more insight and practice with the tools associated with the cyber security field. I have also participated in two CTFs at National University as the cohort before and the cohort after mine had developed a cyber security CTF for their capstone project. The first CTF was the attack-defend style as the second one was the Jeopardy-style. The first CTF at National University gave me the idea to develop and host a CTF for my capstone project for my Masters in Cyber Security and Information Assurance (MSCSIA) program at National University and the OWASP San Diego CTF helped me to develop challenges for my capstone project.

My capstone project for the MSCSIA became a cyber security CTF in which it is a training tool for school and businesses to ensure cyber security awareness among students and employees. My group consisted of three people from my cohort, including myself. My team had a big challenge trying to find information on cyber security CTFs as there was not a single book out there that talks about the CTFs, let alone how to develop one. We found information via the Internet and got experience with one at the OWASP San Diego CTF held a few weeks before ours. We learned a lot from hosting the CTF as it was successful but there were things that went wrong.
The original plan was to have two teams and do a hybrid attack-defend and Jeopardy-style CTF. However, as the competition day drew closer, we had a lot of problems and had to go through the IT department due to us using Coleman University’s campus and equipment. Since we ran into these problems, we decided to just do a Jeopardy-style CTF and had to quickly develop challenges. Each of us divided up the categories and developed the challenges for those categories. The categories included: Reconnaissance, Cryptography, Steganography/Hashing, Scanning, Trivia and Best Practices. The teams went from two to four and it worked out as there were 11 participants for the CTF.
I had received some free stuff from Cisco Live 2015 San Diego to give away to the teams as prizes for the CTF. Everyone who participated received a Certificate of Participation and the professors that helped us out received a Certificate of Appreciation. Overall, all of the participants had learned a lot from the CTF and the judges of our Capstone Project presentation were impressed. Cyber Security CTF competitions are a way to help maintain awareness and for employees and students to gain more knowledge regarding cyber security.
If you are interested in participating in a cyber security CTF, please check out CTFTime.org, UCSB’s iCTF, and search the Internet for other CTFs that may be in your area. The NCL is accepting registration for its 2016 Fall Season until October 3rd for the Regular Season and it costs $25 per person. The need for more qualified security professionals is extremely high and participating in these CTFs will help reduce the skills gap.





Thank you very much for the post. playing CTF is a great way to hone security skills.
I wanted to ask, Is Cisco Cyber range considered a type of CTF or it altogether different type of competition?
I believe it’s an entirely different competition. I am wanting to develop and host a CTF at Cisco Live US. It would be a great way to get some of the attendees a chance to hone their skills.
Great post. There is no better tool to improve skills than competition after a hard professional preparation at any level, any time, any place. Thanks for sharing your insights.
Gulf gate hotel security waste