Tim Harmon is a Cisco Champion, an elite group of technical experts who are passionate about IT and enjoy sharing their knowledge, expertise, and thoughts across the social web and with Cisco. The program has been running for over five years and has earned two industry awards as an industry best practice. Learn more about the program at http://cs.co/ciscochampion.
=============================================
Welcome to Part 3 of the Cyber Security Capture the Flag (CTF) Series. So far in the series, we have discussed how to design/plan the CTF event and how to develop the event (Part 1, Part 2). This part will discuss the implementation phase in which the CTF event is actually taking place with the participants.
The day for the CTF event has come and the team will need to power up all machines being used in the event. It is best for the team to be at the venue at least one to three hours before the participants are expected to arrive. This will give the team enough time to check to make sure that everything will go well with connecting to the server and scoreboard, doing the challenges, and inputting the answers into the scoreboard. Realistically, there is a good chance that something will go wrong at some point during the event. When it happens, the team needs to relax and figure out the solution as fast as possible. The team will need to make a rules sheet that has all of the rules the participants need to follow and then send it out to the participants in order for them to read the rules before the event.

The best way to start the event is to have a little presentation introducing the team and giving the what, why and how of the event. This can be done using PowerPoint or some other presentation software. It is recommended that the team teach the participants some of the basics on how to go about solving the challenges. For example, one team member can demo a cryptography challenge (preferably one that is not a part of the event) to show what a participant can do to figure out the solution. It is highly recommended that every participant to have access to the Internet, unless the event is strictly an attack/defend competition. My team realized this while going through our CTF event because it just doesn’t work to have one (1) computer per team that has Internet access in a four (4) hour event.
Once the presentation and demo has concluded, the participants will be either grouped into teams or individuals (depending on the administration team). There should be a timer in order for the participants to know how much longer they have to complete as many challenges as possible, if not all of them. The participants will then start working on the challenges. The admin team will be going around answering questions the participants may have but will not be giving out the answers to the challenges. They can give out hints on how to go about figuring out the answers. Depending on how long the CTF event is to go on, there can be breaks and possibly a lunch break. If a lunch break is scheduled during the event, the admin team must be able to provide food and drinks to the participants and make sure that all of them are taken care of when you have people with special diets (i.e. diabetes, vegetarian, etc.).

After the lunch break, the teams will continue to work on the challenges, or switch places if it is an attack/defend event where each team attacks the other and finds the flags to be submitted. When the timer for the game is done, the admin team will look at the final scores and congratulate the top teams. It is recommended that all participants receive at least a Certificate of Participation as it may help some of the participants to receive Continuing Education Units (CEUs) for their certifications or other requirements. Also, teachers that have some of their students participating in the CTF event may get assignment credit or extra credit for participating but it all depends on the teacher and institution. It is recommended that the team provide prizes for the top 3 to 5 individuals/teams as it would be a token of appreciation for those participants as they had worked hard to get the scores they did. Below is a picture of the final scores and prizes my team gave out to the participants of our CTF event for our capstone project, a part of the Master of Science in Cyber Security and Information Assurance program at National University.
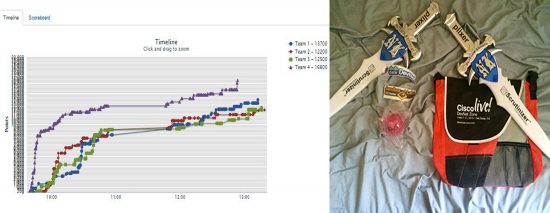
The bags were given to the top two teams and the plixer swords were given to the top two MVPs (one from each of the 2 top teams). These prizes were gathered at the 2015 Cisco Live conference in San Diego, CA. After all prizes are given out and the event is done, the team will need to clean up and they can either discuss the outcome of the event before they leave for the day, or schedule a different day to meet for discussion. This discussion will help the team to figure out what worked and what didn’t. It will also help the team to come up with some other ideas for the next CTF event. The team should give a big thank you to the people in charge of the venue that the event was held and any vendors that may have sponsored the event.

The picture above is the CTF event my team did for our capstone project and it was a success. When you implement your planned CTF event the way you are expecting to do it, then you can almost guarantee that it will become a success. Implementation makes all of the planning, designing and developing to come together into a magnificent piece of work, if done correctly. Sometimes things will go haywire but it can still be recovered and be successful. In the next part (Part 4: Monitoring), I will discuss the importance of monitoring in the CTF events and how you can implement it.




