I’ve finally had a chance to stop and smell the roses. The roses being Cisco ISE 1.3 that is. It’s been a much anticipated update to Cisco’s core TrustSec component and there are a number of improvements, many dealing with Guest users. So what has Cisco done to improve? Let’s look at 5 areas related to Guest access:
1. End-User Web Portals
2. Notifications
3. Guest Portals
4. Sponsor Portals
5. Non-Guest Portals
End-User Web Portals
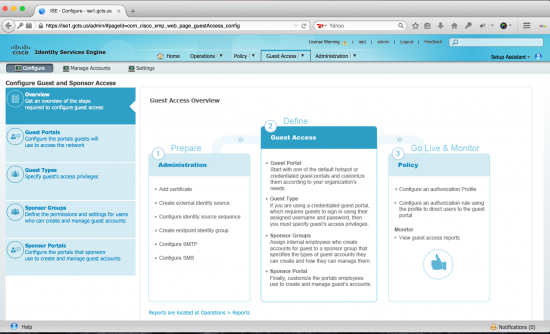
One of the new features that I really like is how the interface has been modified to centralize the portal configuration tasks and customization into a single location. The first thing you notice when you navigate to Configure Guest Access and Sponsor Access is that the interface is designed to make life easy. Three steps to Guest Access are overviewed and each step is clearly identified. We don’t usually find this information in the user interface. Normally we’re looking for this in an End User Guide or a Lab Guide for one of the courses I teach. So, in my opinion, this is a fresh new approach to making a complex device like ISE much easier to use.
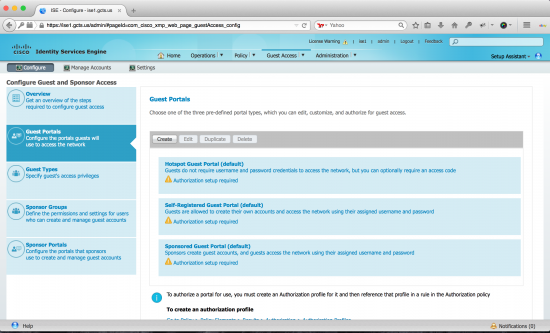
Upon creating a Guest portal you are prompted to create on of three types of portals:
• Sponsored-Guest Portal
• Self-Registered Guest Portal
• Hotspot Guest Portal
From here you define the behavior of your portal. The look and feel is similar to what ISE looked like in the past, but minus the flow graphic. You can also see to the right of the description that there is a new portal test feature.
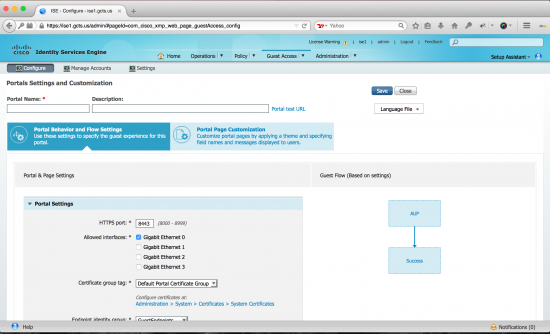
Using the test link presents the portal. This is nice for customizations. In the past the Guest access had to be tested by a guest because the URL redirect included the common session ID and you couldn’t just create that on the fly.
There’s also a number of links to direct you to places where you need to do things outside the work center. Again, this lends itself to the overall ease of administration that this update provided. Configuration instructions are found in the Cisco documentation here.
Notifications
Part of the process of providing guest access could make use of a Sponsor. A sponsor is someone who can create a guest account and provide the guest with credentials. There have been enhancements to how a sponsor can provide these credentials to a guest. One way is that we can send the credentials via SMS to the guest. There is now a list of major SMS gateway providers we can use making it easier to configure this feature. Certain locations I’ve been at don’t have strong enough cellular data connections to get the credentials that were emailed to me. however I could still get text messages. With this feature I can SMS the guest credentials to a user if I need to. And when the guest account is going to expire we can now send expiration notifications. On one occasion I was teaching a class and our guest accounts expired half way through Friday. It would have been beneficial to have notification that the account was going to expire. This is another welcomed enhancement to the feature-set of Cisco ISE. Configuration instructions are found in the Cisco documentation here.
Guest Portals
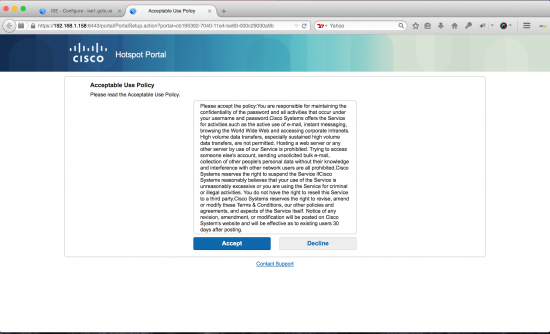
A Guest Portal is what an end user sees when they access your guest network. For example. a guest user would associate with the guest-wifi. This triggers a series of events. The user MAC address is sent to ISE, it’s not found in the local endpoint database so it continues on to authorization policy. None of the authorization policies match since we don’t have any information about the end user, so the default rule instructs ISE to send a URL redirect back to the wireless controller. The URL redirect is forwaded to the client browser and the guest sees a guest portal where they can provide credentials, accept an AUP, or even register themselves as a guest.
There have been some significant updates to the guest portals in ISE 1.3. Cisco has really done a nice job here with making it easier than ever to deploy a guest portal. Smart defaults are now available for guest portals and flows, guest types, and sponsor groups. This cuts down a lot of the work we would normally have to do on the back end. The less time we can spend putting the pieces together the better.
Additionally when a user hits the guest portal we can now require the use of a passcodes. This can be a simple passcode that is used in combination with usernames and passwords adding an extra element of control. And in terms of the actual portal process, you can require a guest account that has self-registered to obtain approval from a sponsor before they are given access. This will cut down the work that a sponsor has to deal with, allowing the guest to register on their own, and then letting a sponsor simply approve the registration. Again, this is another feature lending itself to the overall ease-of-use that seems to be the focus of this new update.
Finally, once the guest has authenticated they would typically see a message in the browser that instructs them to go ahead and access the URL they were originally trying to go to. In ISE 1.3 the guest can be redirected to the original URL or a static URL of your choose after they successfully authenticate. This is a nice enhancement in my opinion as end users often were confused after initial login.
Guest portal configuration instructions can be found in the Cisco documentation here.
Sponsor Portals
There were not a lot of modifications to the sponsor portals but the one enhancements here that improves the end-user experience is that we can now provide the guest with the SSID they should be connecting to. Why is this a nice feature? Have you ever been at a location with more than 20 SSID’s available to you? Which one should you use? In multi-tenant buildings this can be a pain. I’ve seen more than one “Guest” network being offered and so having the name of the network just makes life easier. It’s subtle, but it’s beneficial.
Sponsor portal configuration instructions can be found in the Cisco documentation here.
Non-Guest Portals
There are a few additions to the non-guest portals but I’ll just talk about two of them here. Part of the process of registering a BYOD device is capturing the MAC address of the device and adding it to the internal endpoints database. Users can then access a “My Devices” portal and manage the devices they have registered. This helps them to mark the device as lost of stolen and so on. Part of our back-end configuration was to device a simple URL that users could navigate to in order to manage their devices. In version 1.2 this was a single URL that everyone accessed. In ISE 1.3 we now have “per-portal” URLs for the My Device Portal as well as for the sponsor portals. Since there are now multiple URLs that can be specified it’s obvious that there are now multiple ““My Devices”” portals with different default endpoint identity groups that can be set up, so that registered devices can be assigned to different endpoint identity groups.
Instructions for creating a “My Device” portal can be found in the Cisco documentation here and here.
Wrapping It Up
What I’ve discussed here are just a few of the many enhancements in Cisco ISE 1.3. As mentioned in the onset, much of what Cisco has done focuses on the ease if use for an administrator of ISE as well as the overall enhancement of the end-user experience. After doing many ISE installs it amazes me how much you can do with Cisco ISE and how it is really an integral part of a network these days. There are many more features and enhancements in ISE 1.3 and you can read about them in the release notes found here. If you have a Cisco account with download privileges you can also get a trial of ISE 1.3 that can be deployed as an OVA making it easy to get in and mess around with the new features. And if you’ve already been working with ISE 1.3 I’d welcome your comments on what your favorite new features are.




