Our mobile devices are like a second brain, remembering, reminding, and informing us throughout our daily tasks. It would be great for productivity if your “other mind” could stay continuously connected from the time you got up at home or hotel on Wi-Fi, travelled to work on cellular, and instantly connect to the local Wi-Fi as you travel deeper into office buildings, malls, and airports. No more dropping calls or message streams as the device attempts to reconnect to different Wi-Fi access points from heterogeneous access providers. As we grow ever-more dependent on our devices to work, communicate, and innovate, continuous connectivity to internet resources and business applications anytime, anywhere is the baseline expectation.
That’s why Cisco is collaborating with a federation of wireless access providers, identity platforms, and enterprises to create OpenRoaming, with the goal to provide continuous secure wireless connectivity as consistently as possible across diverse networks. Instead of frustrating device owners with multiple captive portals for selecting and logging into separate networks, devices can install one or more identity credentials that will securely and automatically permit onboarding to participating wireless networks.
What’s going on behind the scenes to make this convenience possible? Let’s examine the technology and partnerships that are making OpenRoaming possible today.
A Federation for OpenRoaming
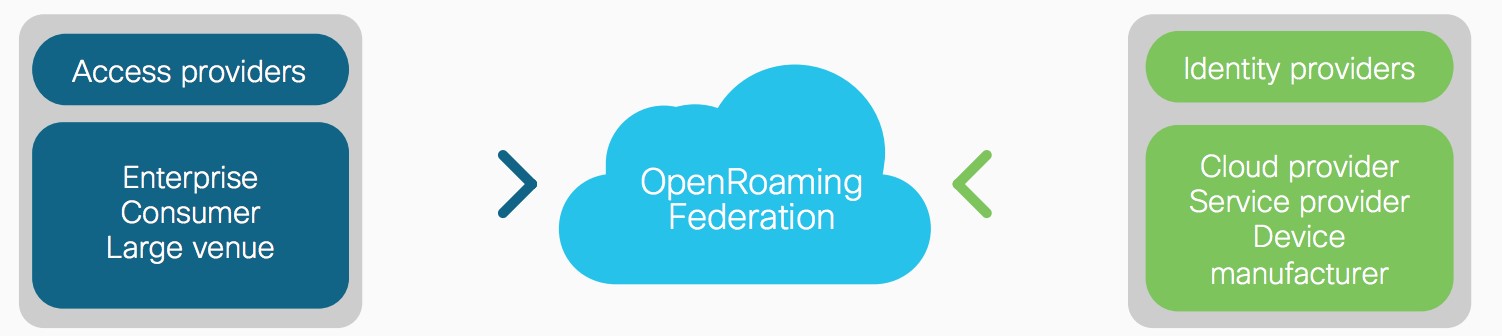
While OpenRoaming is founded on Cisco’s proven PassPoint wireless access technology, it really takes off with partnerships among access providers, identity providers, enterprise IT, and Cisco.
- Wireless access providers join the OpenRoaming Federation to offer seamless and secure access to their networks in public spaces such as airports, retail, and hospitality without the hassle of a captive portal.
- Identity providers, such as mobile and cable services, engage customers with loyalty programs and want them to be able to attach to their local wireless network as soon as they enter the property to provide alerts, associations, and personal services.
- Access, identity, and enterprise participants in OpenRoaming can also choose to accept login credentials from Google, Apple, and Facebook, with others in the queue for implementation.
- Enterprise IT can leverage enterprise identities for employees, partners, and maintenance providers to enable seamless onboarding to wireless campuses, giving each credential specific levels of access permissions to protect business data while providing access to role-appropriate applications.
Cisco is offering support and services to promote, maintain, and advance the OpenRoaming platform by providing an SDK to create apps and web pages that securely install identity credentials on devices, and tying Cisco OneID to OpenRoaming access.
OpenRoaming is the Gateway to Seamless Onboarding
Making OpenRoaming transparent to device owners is a key step that is most efficiently accomplished by the device makers themselves. Native OS support for OpenRoaming ID credentials, such as Samsung has implemented with the Note 10 generation, enables devices to detect and automatically join OpenRoaming networks with no additional screens or logins by the device owners.
For devices not yet incorporating OpenRoaming IDs natively, Cisco provides an SDK that enables enterprises, access and identity providers to easily build on ramps to OpenRoaming networks, with granular control over access privileges. Using the Cisco OpenRoaming SDK, a customer loyalty program, for example, can incorporate an identity credential into their mobile app, which in turn adds the credential to a device’s Wi-Fi access list. When a customer walks into a store or hospitality site, the device senses the Wi-Fi, checks if an installed credential is available that is associated with the network, and if so, automatically joins.
Enterprises can also use a Mobile Device Management (MDM) system to push credentials to employee devices. In situations where the provider doesn’t care to gather personal data, the credentials can be anonymous. As long as the service provider that owns the network recognizes and permits attachment with the certificate, the onboarding is immediate. Venues also get to choose not to let specific credentials attach—when a competing loyalty program is installed and not the preferred ID, for example. The flexibility of the OpenRoaming SDK provides many ways to ensure secure connectivity fits with the needs of an organization.
Real-World OpenRoaming Results
At our recent Cisco IMPACT event, in Las Vegas, to connect over 18,000 Cisco employees, the IT event team deployed OpenRoaming credentials to 14,000+ iPhones through a Mobile Device Management system, 446 Android devices via a custom Cisco mobile app, and 1,200+ Samsung devices through an automatic update directly from Samsung. All these devices automatically connected to the event’s Wi-Fi through 2,600 access points distributed throughout the venue and adjacent hotels. It was a dramatic demonstration of the usability and robustness of OpenRoaming where most attendees didn’t even notice they had been automatically attached to the venue’s wireless network. In addition, as people moved from conference center to nearby hotels where OpenRoaming networks were also available, the switch from Wi-Fi to cellular to Wi-Fi was seamless. A similar implementation was also available at the last Cisco Live in San Diego.
Advantages of OpenRoaming with Cisco DNA Spaces
What’s better than enabling customers, guests, and employees to automatically join wireless networks as they enter a site, securely, without passwords? The ability to identify the current location, in real-time, of customers, guests, and employees in order to provide them with a personalized experience. Integrating OpenRoaming with Cisco DNA Spaces provides a real-time window into activities occurring around each access point (AP). Mapping the locations of APs onto the layout of spaces, such as retail stores, conference centers, and office spaces, provides detailed analytics for device types, movements, bottlenecks, dwell times, and other statistics that help manage the flow of people through a site.
Why is OpenRoaming key to obtaining a detailed view of business traffic patterns in digital spaces? By facilitating immediate attachment to the local Wi-Fi, more data is gathered for analysis. Relying on people visiting a space to take the time to join through a captive portal inhibits the attachment rate. Visitors are also reluctant to join open networks if they do not know if the connection is secure.
When the goal is to welcome visitors and provide value-added services such as wayfaring and personalized promotions, then the onboarding process must be seamless—indeed, nearly invisible—to the customers. Note that the first time a device attaches to a network through OpenRoaming, a message can appear on the device explaining what is happening and that the connection is secure, as indicated by the device’s Wi-Fi settings.
OpenRoaming and Cisco DNA Spaces provides valuable data for businesses by using the Wi-Fi that is already installed for location tracking, instead of requiring the installation of additional beacons and an overlay network fabric. When a wireless network is managed with Cisco DNA Center, IT can take advantage of Cisco Assurance to monitor and diagnose RF interference, lags in onboarding, high-density areas, and hard to pinpoint anomalies that randomly pop up in a busy network.
Privacy Regulations Designed Into Cisco DNA Spaces
With strict privacy regulations taking effect around the world, data privacy is a key consideration for designing and deploying Cisco DNA Spaces. Collecting personal data needs to be securely managed. When creating OpenRoaming apps to work with Cisco DNA Spaces, users of the app must be able to opt-in with clear instructions on how data is being collected, stored, and analyzed to help improve their experience, along with a simple opt-out method. OpenRoaming will not share any personally identifiable information with the owner of the Wi-Fi network unless individuals explicitly allow it. Any stats and analytics collected through Cisco DNA Spaces are anonymized and stored in clouds that abide by regional privacy rules in the EU, USA, and China. As privacy regulations evolve, Cisco will adapt the Cisco DNA Spaces ecosystem and cloud storage rules to ensure compliance.
OpenRoaming: No Passwords, Secure, and Seamless—It Just Works
For more information, visit the OpenRoaming web page on Cisco.com.
When we set out to make OpenRoaming a Wi-Fi standard with industry consensus, the goal was to attain three attributes: no passwords, secure, and seamless. We want to create a new experience of onboarding for the vast majority of mobile devices that people use throughout the day for work, play, and communication. Connecting to public-facing wireless networks should be as easy as roaming with LTE or in the carpeted-spaces of enterprise campuses. Once that problem is solved, we predict there will be a cascade of use cases to bring new services to a wider range of venues. There will, in fact, be a “delight” in the ability to stay connected with high quality of experience.
While the technical foundation of OpenRoaming is proven and readily available, it’s still in the early stages of deployment. You can play a role in making it more ubiquitous by joining the OpenRoaming Federation and by starting to put the technology to work in Cisco DNA Spaces within your own enterprise. Starting in December, Cisco will be accepting applications to join the OpenRoaming Beta Program. Customers using Cisco DNA Spaces will see a new application card for OpenRoaming in their dashboard and be able to test OpenRoaming capabilities with DNA Spaces in their own organization. Become part of the next wave of Wi-Fi applications and services and bring the delight of constant connectivity and digital spaces to benefit your organization. We’re excited to see how you will use this new solution.
Read about The Canary Wharf Group and Cisco’s trial deployment of #OpenRoaming, that provides 290,000 weekly visitors easy access to secure public #WiFi anywhere within London’s Canary Wharf, without logging in with usernames and passwords.






Amazing