Networks are more business critical than ever, and segmentation is becoming the key to ensuring their security. Segmentation allows users and things access to the right applications and data, while preventing lateral movement of threats. It needs to work across all network domains, from wherever the endpoint is to wherever application or data resides. It requires us to cross both technology domains and organizational domain boundaries.
The technology to do this is ready now, and I’ve spoken with many customers who have also broken down organizational silos to benefit from these innovations. I’d like to hear from you about how else technology and IT orgs need to evolve to enable policy-based access across domains.
Intent-based networking and technology silos
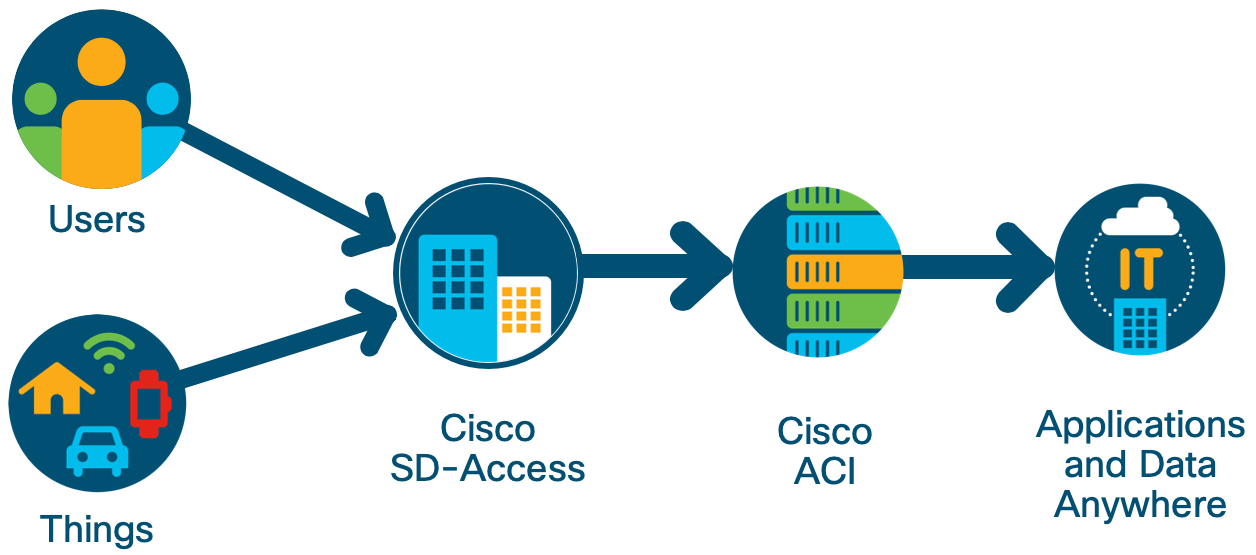
In the enterprise campus, IT managers can use Cisco Software Defined Access (SD-Access) solutions to segment campus and branch users and devices. Cisco SD-Access can also be extended to industrial environments through integration with our ruggedized IoT portfolio. In the data center, applications and data get segmented through Cisco Application Centric Infrastructure (ACI). And with Cisco Cisco SD-WAN, traffic between users, applications in the data center, and the public cloud can be managed and secured in new and flexible ways. These solutions, in combination, provide end-to-end control of who gets on a business’ network, what data and applications they have access to, and what quality of service they experience.
Cisco is advancing intent-based networking (IBN) to manage segmentation policies in the campus, branch, WAN, data center, and cloud. IBN helps organizations achieve greater coherence between business needs and networks. Cisco SD-Access, SD-WAN, and ACI solutions have changed how organizations define policies for segmentation, using intent. With IBN, policies are translated and applied automatically to network infrastructure. And to make sure that the intent is really achieved, context-based analytics provides assurance and recommends necessary course corrections.
We know that large and medium-sized organizations need to adopt a holistic network strategy to cope with the unique performance, security, and management challenges of highly distributed applications and architectures. Legacy approaches that have relied on manual processes to manage and secure data and applications are no longer adequate or sustainable.
We need an intent-based networking architecture across all domains.
Policy integrations provide the bridge across domains
You might ask, why not have the enterprise run on a single fabric? In the real world, each network domain has a unique set of requirements and is purpose-built to address them. The campus has to handle wired and wireless clients with high mobility demands and varying identity mechanisms. The data center has to deliver high east-west bandwidth and control, integrating with virtual machine and container environments. Customers also construct networks and fabrics to manage failure domains and separation based on administration domains. Many network fabrics help solve these requirements, but we still need to connect these fabrics seamlessly.
The integration of policy between domains is the best way to preserve domain uniqueness and still provide essential consistency and management. With policy integration, each domain, while functioning independently, can collaborate with others for the benefit of the entire network.
Cisco is taking steps to apply policy and assurance integration across network domains, to allow IT and business intent to be expressed in one domain and then exchanged, enforced, and monitored across all of them.
We are introducing the first integrations today. We will empower IT managers, for the first time, to provide consistent performance, compliance and security enforcement across campus and data center.
Policy integration between enterprise network domains.
Cisco ACI and Cisco SD-Access
In enterprise networks, Cisco’s SD-Access solution has replaced the need for IP-address-based access control, and its associated manual configurations, with management by identity-based groups in which users and devices are assigned to groups. In the data center, Cisco ACI uses a similar grouping method for applications. Both SD-Access and ACI associate security policies with these groups. With the new integration, SD-Access will transmit information to ACI about the user and device groups it creates and will, in turn, learn of the groups ACI creates for applications. This exchange will allow SD-Access and ACI to learn and enforce each other’s policies in their respective networks, leveraging Cisco Identity Services Engine (ISE) as the common broker.
For example, let’s say a hospital hosts health and billing applications in its datacenter. Hospital employees are segmented into separate user groups. By mapping the groups between datacenter and campus, end-to-end policy can be enforced automatically so that only the health provider group (doctors and nurses) has access to the health application, and only the finance department employees and executives have access to the billing application, regardless of their location. End-to-end policy greatly reduces the risk of a breach of sensitive financial data and patient health records.
Look forward to more
The policy integrations we are announcing today are just the beginning. We are committed to helping our customers manage and orchestrate enterprise-wide networks — as they take advantage of the new opportunities that today’s technologies open for them. We will be with them in this journey.
For more on this topic, please see:
- Read: The Cisco Data Center goes anywhere your data is
- Watch: “Tech Field Day” on policy integration
- Learn: Getting started with SD-Access
- Learn: Seamless user-to-application segmentation with ACI and Cisco DNA and ISE






Nice articulation of "Why" seamless integration for policy and assurance between the Access and Datacenter domains/fabrics is needed vs. creating a single fabric/domain.
I like the demo contained in more on this topic." Seamless user-to-application segmentation with ACI and Cisco DNA and ISE"
Sounds it's a good solution to separate different function groups from business level. Always we also been required to grant different access in same business group. May be only technical activity of implementing it. So good to learn this product.
À Nice posting. We will be graceful if you can post some practical aspects of those new technologies. I mean technical aspects.
Thanks a lot for your all your contributions.
Would be great to get specific details. Conceptually it sounds great, but ultimately the solution has to be deployed, managed and be functional.
A little bit or significant substance needs to be attached to the write-up.