With the growing threat landscape, it is imperative for product designers to build integrated security. This means that the security must be total and go across the board from procurement to deployment. This total security allows customers to establish trust. Often the introduction of this security paradigm overlooks and compromises simplicity, which can result in significant loss of valuable operational time thus resulting in poor customer satisfaction and even worse success metrics.
To address this two-fold security and simplicity challenge to establish trust, Cisco commissioned Miercom, an independent testing lab, to comprehensively evaluate and test Cisco Digital Network Architecture and Huawei’s Agile Solution. The detailed report of Miercom’s analysis is already published for download.
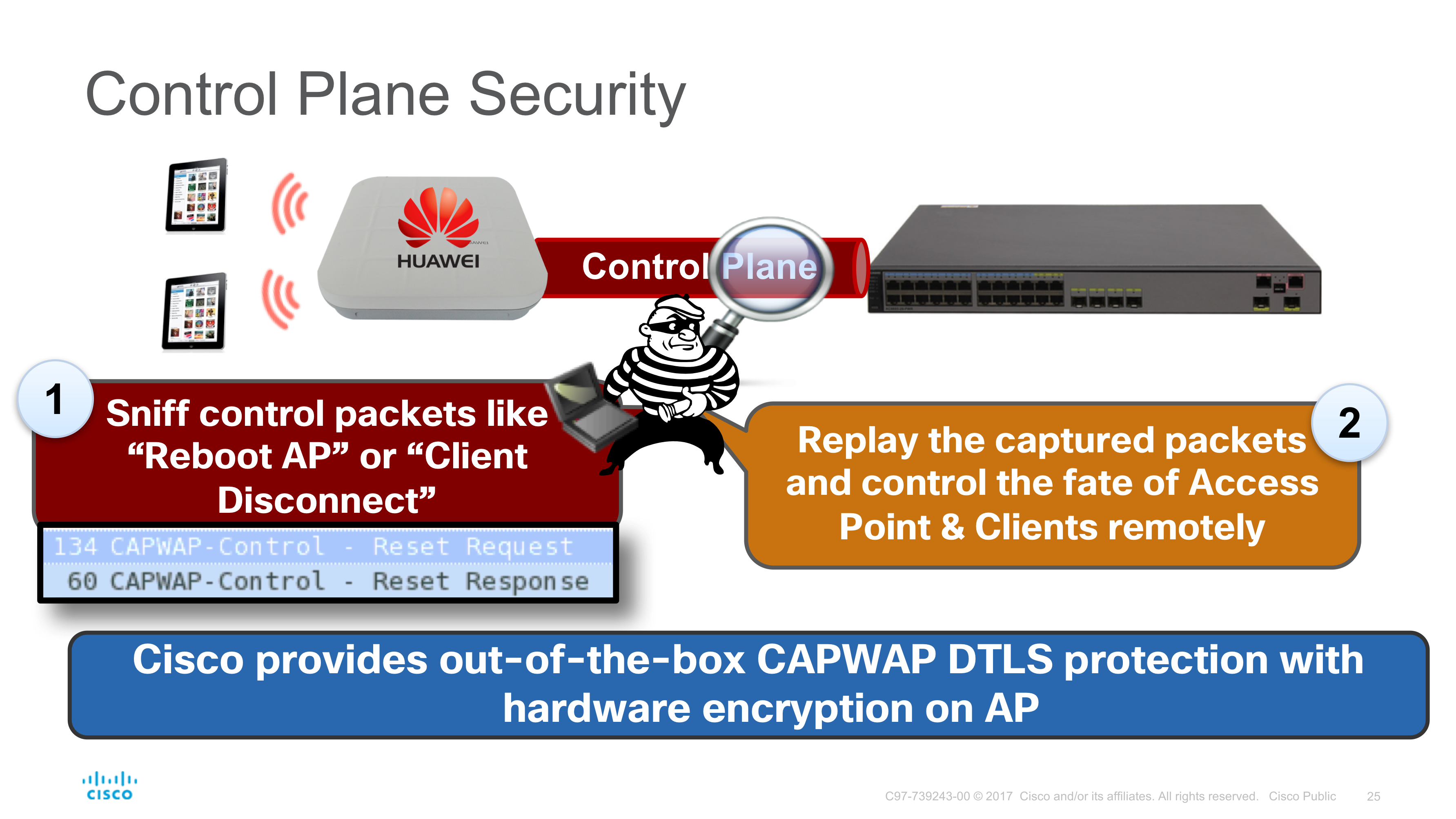
We will dive deep into the test case to evaluate “Control Plane Security”, a communication protocol between the Access Points and the Wireless LAN Controller (WLC) that allows for secure exchange of configurations and wireless client information.
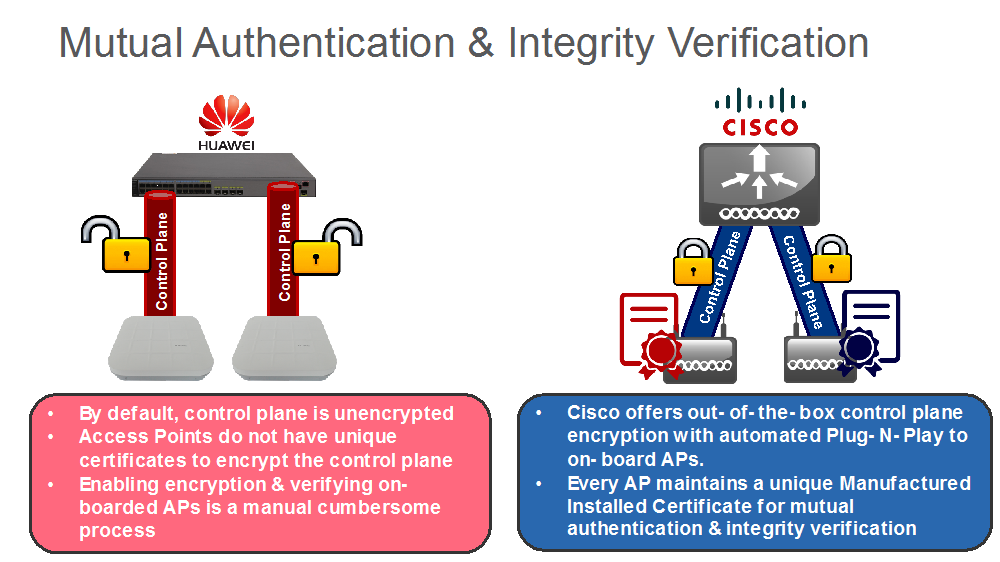
Miercom observed that Huawei does not encrypt the Control Plane tunnel by default and the data communication is readable in clear-text. On the other hand, Cisco secures the communication channel with a plug-and-play offering that saves significant deployment time while ensuring trust.
Because Huawei keeps the encryption disabled by default, on further test Miercom evaluated that the protocol is susceptible to Man-in-the-Middle attacks. It was observed that a remote attacker can:
- Simply replay the sniffed packets to command Huawei’s Access Point while pretending that it is coming from a legitimate Wireless LAN Controller.
- Hijack the legitimate wireless client session and connect the network with an un-authorized device.
If the customer deploying Huawei’s Agile Solution reads the “Warning Sign – Datagram Transport Layer Security or DTLS for Control Plane is OFF by default” and understands the implications then there is no choice but to activate it. Miercom explained about what it takes to activate DTLS encryption to measure the operational burden on customers:
- Manually create whitelist of all the Access Points MAC address on their controller.
- Configure a common “Private Secured Key” (PSK) that will be used for Control Plane DTLS encryption.
Miercom observed that the overhead of implementing PSK across the infrastructure still does not guarantee security because it is susceptible to brute-force dictionary attacks. In sharp contrast, Cisco’s DNA offers out-of-the-box mutual authentication and integrity verification. Every Cisco Access Point carries a unique Manufactured Installed Certificate (MIC) that is used for mutual authentication with the WLC and the entire process to verify the integrity of the products and does not demand any user intervention. The work is already done for the customer.
 It is also important to note that one of the key reasons Huawei shies away from activating DTLS by default is their lack of performing encryption and decryption in hardware, which directly affects their wireless performance. Click here to find out Miercom’s result on performance.
It is also important to note that one of the key reasons Huawei shies away from activating DTLS by default is their lack of performing encryption and decryption in hardware, which directly affects their wireless performance. Click here to find out Miercom’s result on performance.
Finally, Miercom evaluated Cisco’s suite of Trustworthy Systems features that offers customers insight into device integrity, run-time defenses to ensure only genuine Cisco software and hardware can operate together. Huawei’s Agile Solution fails to offer any visibility and innovation that can allow customers to build a chain of trust that ensure their investments are safe and protected.
Remember trust has be established from supply chain to production deployment with built-in simplicity.
Click here to download the full report.
Read other security resources that are evaluated by Miercom:






Great read! Provides a great rationale as to why purchasing a Cisco product over the competitor is the better choice.