Today, host-based security mechanisms and cloud-based security services are our primary means to secure endpoints. However, these methods alone will fall short for meeting the security challenges in the emerging Internet of Things, where we must support a significantly larger number of endpoints, many of which are highly resource-constrained.
To succeed in securing the increasing population and widening range of endpoints, and enable innovations never imagined, we need to address a list of new concerns. For instance:
• Reducing the processing load on resource-constrained endpoints
• Meeting the stringent latency requirements for security-related processing in mission-critical systems such as industrial control systems and connected vehicles
• Enabling trustworthy temporary local connectivity to allow, for example, maintenance personnel to connect their tools to a machinery for diagnosis and repair
• Overcoming the bandwidth constraints for cloud-based security services
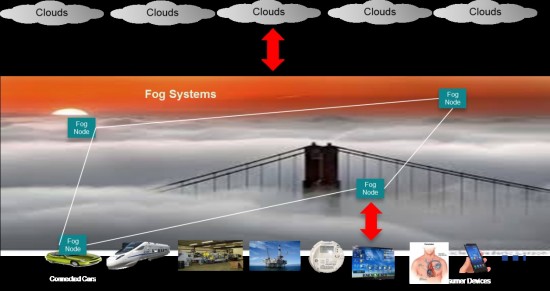
Fog computing—which distributes resources and services of computing, data storage, and smart networking close to end users—can provide a range of new services to help address some of these challenges.
Some of these fog-based services include:
 Updating Security Credentials and Software for Endpoints
Updating Security Credentials and Software for Endpoints
Keeping the security credentials (such as security keys and certificates) and software on a large number of devices up to date is a growing challenge. Requiring every endpoint to connect to remote servers to update its security credentials and software often proves impractical.
Fog computing makes a promising solution. Fog nodes, functional nodes deployed close to or even diffused onto the endpoints, can assist the endpoints in updating their security credentials and software. They can, for example, automatically acquire security keys, credentials, and software updates on behalf of the endpoints and then use simpler protocols and processes to distribute the updates to the endpoints locally.
As a result, there’s no need for every endpoint, especially the resource-constrained endpoints, to run complex procedures and protocols to automatically acquire and update security credentials directly from remote clouds.
For example, each electronic control unit (ECU) on a car will no longer need to directly communicate with off-board security systems to acquire and update its security keys and certificates. Instead, a fog node (in the form of a software client or a security gateway) onboard the vehicle can obtain the credentials and then distribute them to the ECUs locally.
Authenticating Endpoints
Fog computing can also assist in the authentication of resource-constrained endpoints, so that each individual endpoint no longer has to authenticate directly with remote security servers.
This brings us back to cars. It’s overly complex and impractical to have every ECU in a car authenticate directly with off-board servers. Onboard fog-based authentication resolves this issue, while preventing compromised, rogue, or otherwise unauthorized ECUs from being installed onto connected vehicles.
Protecting Endpoints
Many security functions that are traditionally implemented on endpoints in today’s Internet can be moved to fog systems. This eliminates the need for installing, managing, and updating complex security software and hardware (such as comprehensive malware detection and protection mechanisms) on a large number of endpoints. (More about this is my next blog.)
Establishing Trusted Transient Local Connections
There’s an increasing need for devices to establish transient (temporary) connections with other nearby devices. For example, a technician connecting to manufacturing machines to perform repairs and maintenance or an emergency responder connecting to a patient’s embedded pacemaker. Fog systems can assist in authenticating these devices and in establishing transient trustworthy connectivity.
Monitoring and Reporting Endpoint Security Status
Because its closer proximity to the endpoints, a fog system can monitor the security status of local systems and report only the necessary information to remote security management centers.
These are just a few of the benefits of fog in helping to secure IoT. In my next post, I’ll delve more deeply into how a fog system can perform malware detection for endpoints.
Want to catch up? Read my last blog post here.
@Tao_Zhang1




