In my previous blog, I shared the importance of ubiquitous malware defense. Specifically, it’s critical as the Internet of Things (IoT) continues to proliferate, connecting a larger number of devices with vastly diverse capabilities. The answer is fog computing, because fog nodes bring more computing capabilities closer to the end devices and can work together to collectively detect whether a file is infected by malware—and respond as needed.
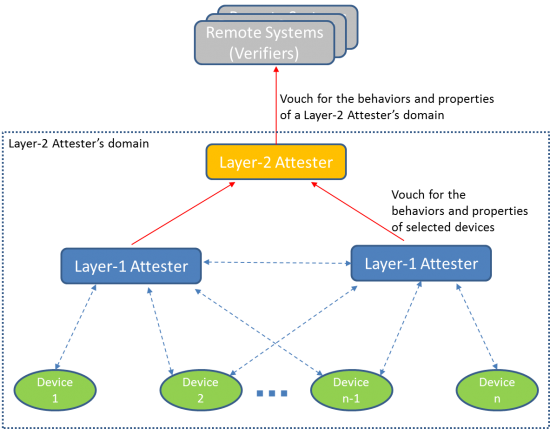
But what about massive scaling? Consider the crucial question: How can we determine the trustworthiness of the many distributed and remote devices and systems in the IoT? Secure scaling to a large number and many types of devices is possible with what we call Crowd Attestation. This is a new approach that enables a system to attest to its trustworthiness—without requiring every individual device to attest to its own trustworthiness.
This can be accomplished in the fog by allowing a subset of devices in a system to act as attesters. Each attester attests to its own trustworthiness, while also monitoring, evaluating, and vouching for the trustworthiness of selected other devices. The set of attesters collectively cover all devices in the system. In other words, every device, including every attester, is monitored and attested to by at least one attester.
The attesters can treat the monitored devices as:
Black Boxes
The attester is assumed to have no knowledge about the internal characteristics and status of the monitored device and can’t rely on the monitored device’s help for monitoring. Instead, the attester will rely on the monitored device’s externally observable behaviors and characteristics to detect any abnormality.
Gray Boxes
The attester is assumed to be able to obtain measurements of some internal characteristics of the monitored device. Such characteristics may include, for example, profiles of authorized program files, device temperature change patterns, electric current patterns, RAM access and usage patterns, and RF signal patterns.
Flexible Boxes
The attester is assumed to be able to probe the monitored device and cause it to react in ways that can help reveal potential compromises to the device.
The Black Box approach is the most conventional approach. It analyzes a device’s externally observable behaviors and characteristics in the:
- Cyber domain (e.g., patterns of network traffic to and from the device)
- Physical domain (e.g., video surveillance)
- Both cyber and physical domains
Black-box monitoring requires no changes to the monitored devices. However, a compromised device could fake its external behaviors in the cyber domain, physical domain, or both.
The Gray Box approach can also leverage help provided by a monitored device. For example, an agent inside a monitored device can measure a selected set of internal properties of the monitored device and report the results to the attester.
However, a compromised device could falsify such measurements by altering the measurements sent to the attester directly, compromising the agent itself, or falsifying the input to the agent on the monitored device.
The good news is, in many real-world scenarios, an attester can challenge a monitored device in ways that will make it difficult for a compromised device to correctly answer the challenges. This is what we call Flexible-Box monitoring.
Multiple attesters can further collaborate with each other to jointly determine how trustworthy a monitored device is by correlating their observations on different aspects of the monitored device’s behaviors.
As more and more things come online, security continues to be a pivotal concern. Crowd Attestation uses fog computing to provide security services to resource-constrained devices and systems. And is a step in the right direction as we enter a world limited only by our imagination.
In my next blog, I’ll share my thoughts on Dynamic Risk-Proportional Protection with Adaptive Immune Security.