From FDA (Food and Drug Administration) to FBI (Federal bureau of Investigations), they see a core issue bubbling up: The vulnerability of Healthcare systems to cyber-attacks. Both agencies have issued an advisory in this regard in the last 1 year.
FDA Advisory was focused on medical devices and hospital networks, while the FBI’s communication is focused on hackers attempting to hack personal medical records and health insurance data and even goes to calling out the gaps in resiliency to cyber-attacks as compared with other sectors such as financial and retail sectors.
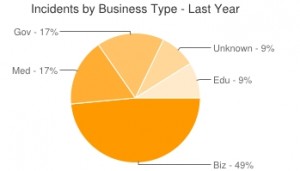
In addition, looking at statistics from datalossdb.org, Health Care sector has consistently been in the top 3 sectors that have had the most incidents.
But the question is, why now?
This is where the correlation with the Health Care IT transition time lines adds up. It’s the other side of Health Care IT transitions that we looked at in the previous part (At the security cross roads of Healthcare reforms and IoE – 6 Health Care IT Transitions) of this blog series – the threat that have emerged from open anywhere, anytime, any device access which has enabled convenience and transformational experience to patients and care teams.
Let’s see an example of the changing dynamics of some of these transitions from a Hackers perspective by analyzing one of these transitions: Transition from Paper charts to EMR and enabling anywhere anytime, any device access to my care teams and my patients.


In the old paper charts days, if someone had to access my personal record, he had to penetrate through the physical safeguards that have been enforced by the hospital including secure access to the location where the paper files are stored. In this situation, while it might be possible for an insider to breach my privacy, it is difficult for a hacker sitting across the globe. Also, if someone wanted to change the reading of one of my vital signs, he had to manually access the paper chart and manually edit the readings.
Now let’s look at the same scenario in a changed environment after the transitions. A hacker sitting across the globe has almost the same access as a patient if he can leverage one of the many attack vectors. Similarly, he has so many options to exploit to modify the data including when the data is in motion or when the data is in rest at multiple places. Once the access location is a home, it’s hard to imagine what type of device is going to be used and what level of protection is available – the 26% of PCs still running Windows XP is a classic example.
As the saying goes – “You are only as strong as your weakest link”, all it takes is such vulnerable access points for hackers to penetrate the system. The internet of things only expands this equation even further by adding more devices, connectivity points and interactions. The above slides highlight some of the security challenges that have emerged with each of these transitions.
The old methods of securing are going to fall short; new innovative methods are required to secure the data. Dynamic learning threat defense systems that perform rapid detection based on flow, signature, behavior, packet capturing techniques in addition to security policies and protection schemes are only the starting points. Visit Cisco’s security offerings, to learn more about how to enable Health Care transitions securely.
Are you prepared to handle these Health Care IT transitions securely?





