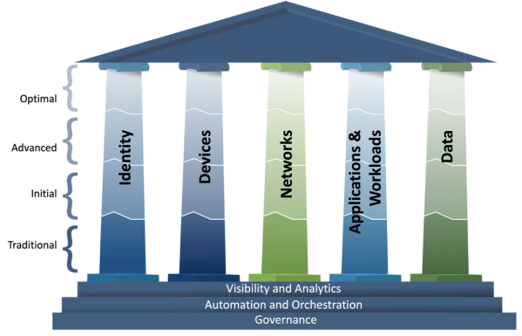
On April 2023, the Department of Homeland Security (DHS) Cybersecurity & Infrastructure Security Agency (CISA) released their Zero Trust Maturity Model Version 2.0 (ZTMM) as “one of many paths that an organization can take in designing and implementing their transition plan to zero trust architectures in accordance with Executive Order (EO) 14028 ‘Improving the Nation’s Cybersecurity’ which requires that agencies develop a plan to implement a Zero Trust Architecture (ZTA).”
What is zero trust?
Zero trust is not a product. It’s a mindset, a path toward better security that includes a set of core capabilities and an approach that emphasizes the concept of least privileged access.
A “never trust, always verify” approach means granting least privilege access based on a dynamic evaluation of the trustworthiness of users and their devices and any transaction risk before they are allowed to connect to network resources.
Step 0 – Understand the Assets and Workflows in the Environment
Before implementing an operational approach with such far-reaching and strategic effects, getting the fundamentals right is important. Don’t go to Step 1 without starting here! NIST SP 800-207 emphasizes that an enterprise cannot determine what new processes or systems need to be in place if there is no knowledge of the current state of operations. In fact, NIST emphasizes that before starting an enterprise’s journey into zero trust, having a “survey of assets, subjects, dataflows, and workflows” remains a necessity. Further, NIST reminds us that “developing access policies around acceptable risk to the designated mission or business process” is crucial to any zero trust deployment.
Likewise, the CISA ZTMM emphasizes “alignment with NIST’s steps for transitioning to zero trust” and that “agencies should assess their current enterprise systems, resources, infrastructure, personnel, and processes before investing in zero trust capabilities.” Additionally, the CISA guide makes reference to NIST CSWP 20: “Planning for a Zero Trust Architecture: A Planning Guide for Federal Administrators” which describes the importance of following the deliberate steps of the Risk Management Framework to help an enterprise discuss, develop, and implement a ZTA. Suffice it to say, focusing on the fundamentals of knowing your environment and applying a risk-informed approach to developing policy remains critical before starting your journey to zero trust.
How the Logical Components and Pillars Work Together
Policies can be developed and deployed by the Policy Decision Point (PDP) to enable granular, least privilege access controls that are enforced in the most optimal Policy Enforcement Point (PEP). Policies are calculated with input from as many sources and with as much context as possible to inform the policy engine. A risk-informed understanding of the appropriate workflows and data flows is critical to developing these policies. All network activity must be visible, understood, continuously inspected, and logged. Any indications of compromise or variations in behavior changes between users and devices, and resources must be investigated, validated, and responded to immediately to mitigate additional risks (Figure 1).
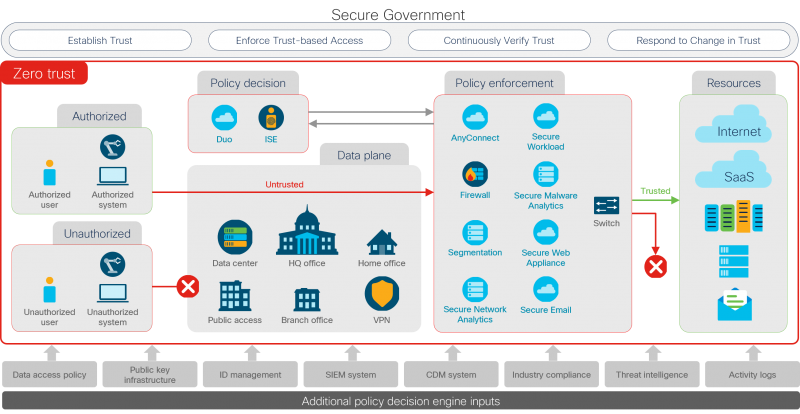
The CISA ZTMM uses a maturity model to describe the necessary capabilities allocated across several pillars. Underpinning the “core five pillars,” the visibility & analytics capabilities support all the capabilities in the pillars of identity, devices, networks, applications & workloads, and data. Likewise, automation & orchestration support, economize, and harmonize all zero trust capabilities and operations across the pillar. To realize the zero trust logical working model from Figure 1, it is important to note that the capabilities must work across pillars wholistically—not by themselves in a pillar or “silo.”
Cisco’s open standards-based integrated capabilities enable government enterprises to take a 4-step cross-pillar approach to help government organizations to deliver secure mission outcomes with zero trust.
How to Apply a Zero Trust Operational Model in 4 Steps
A practical approach for realizing a zero trust journey can be encapsulated in an operational, four-step, cyclical approach:
- Establish trust levels for users and devices, IoT, and/or workloads – visibility and analytics are key to understanding subjects, assets, their state of compliance, and workflows.
- Enforce trust-based access using logical segmentation to control network access (applying macro-segmentation and micro-segmentation) and SD-perimeters to control application access – automation and orchestration work at the speed of the network to enforce policy.
- Continuously verify trust with visibility & analytics – collecting and analyzing telemetry across all five “core pillars,” monitoring user behavior, alerting on potential IOCs, and identifying vulnerabilities – working with automation and orchestration to quarantine devices and isolate potential threats.
- Respond to changes in trust powered by visibility & analytics, working closely with automation & orchestration to enable prioritized incident response and remediation.
Continuously applying these steps helps drive security resilience for your organization and can help you to strengthen your security posture with the power to understand risk exposure, spring back from disruption, and limit the impact of incidents. Cisco solutions integrate with your existing network and the capabilities you already have. They deliver visibility and analytics to know and control what connects to your network. And they provide capabilities from automatic threat updates to machine learning to behavioral modeling that will help you outsmart emerging threats. All of it made easier to manage and more efficient by integrated, automated orchestration through a resilient platform.
Learn more
Go deeper into how Cisco can help you frustrate attackers, not users, and how Cisco enables zero trust security.
Check out the resources and videos on Security Resilience for Government and explore use cases for government at Portfolio Explorer for Government.






It’s really important the comments