Is Lowest Price/Technically Acceptable (LPTA) an impediment to Secure IT solutions?
While many hypothesize that meeting LPTA mandates and also acquiring security “built in” is as rare as the mythological unicorn, I suggest that a reasoned path to both exists.
That path requires a walk through “Value Chain” security. In the public sector, where technology supports government operations at the federal, state and local level, it is vital for government procurers of technology to:
- Embrace the breadth of the IT Value Chain;
- Understand the key threats to the IT Value Chain and the exposures to which those threats correlate; and
- Ensure they procure from trusted vendors who have a comprehensive approach to security across their end to end Value Chain.
What is the IT Value Chain?
The Value Chain is the comprehensive IT lifecycle. Cisco identifies the key stages, or nodes, of our Value Chain as follows:

What Are the Threats and Exposures?
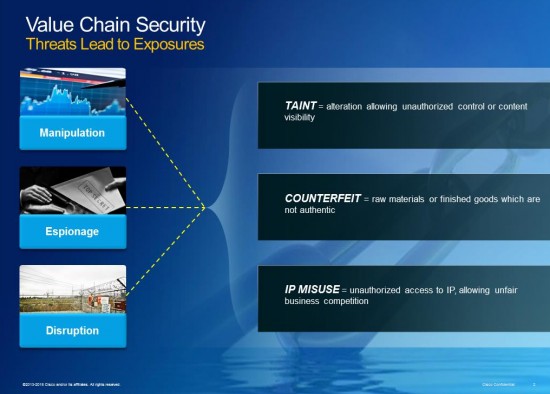
The three main threats to security in the Value Chain, including the supply chain, are manipulation, disruption and espionage. These threats manifest in three fundamental exposures shown below:
How Does Cisco Comprehensively Address These Security Challenges?
Cisco strives every day to be a company worthy of our customers’ trust. We focus on three fundamental principles to build that kind of relationship with customers: being trustworthy, transparent and accountable. We publish these principles at https://trust.cisco.com and practice them every day.
We are specifically embracing the challenge in our Value Chain by using a three-dimensional approach. We attack threats across our Value Chain by layering security technology, physical security techniques and rule-based logical security. This enables us to protect against, detect and mitigate the exposures facing our Value Chain.
Today’s challenge is to balance operating in an LPTA environment without compromising Value Chain security. Government procurers have the power to accept and conquer that challenge. Incorporating concepts of Value Chain security within “ technical acceptability” can provide government procurers a means to gain security and meet LPTA mandates.
At Cisco we will continue to work to earn your trust every day.
Click here for more information on how Cisco is helping to keep our entire Value Chain secure.





