On November 22, 2022, the Department of Defense (DoD) released its Zero Trust Strategy and Roadmap (view here). Cisco has been working alongside the DoD over the past several years to help define and integrate Zero Trust principles as an evolution of the concepts of the defense in depth mindset. Last week, the DoD published its Zero Trust Strategy and it makes note that “Zero Trust is much more than an IT Solution. Zero Trust may include certain products, but it is not a capability or a device that can be bought.”
Back in August, Randy Resnick, Director of the Zero Trust Portfolio Management Office, told the Federal News Network “No single vendor can provide all 90 activities needed for Zero Trust.” Vendors will need to work together to achieve all 90 activities, and authorizing officials must also agree, making this new Zero Trust push align closely with the Risk Management Framework (RMF).[1]
The DoD Zero Trust Strategy notes that the “journey to Zero Trust requires all DoD Components to adopt and integrate Zero Trust capabilities, technologies, solutions, and processes across their architectures, systems, and within their budget and execution plans.” The defense.gov website notes that both the Defense Information Systems Agency (DISA) and the National Security Agency provided development of the Zero Trust Strategy and Roadmap as well as United States (US) Cyber Command and all the branches of the US Military.
The timelines defined in the strategy document also reiterates the importance of implementing a Zero Trust architecture, with a 5-year plan that needs to be executed starting in FY2023 to FY2027 and beyond.
A path to achieve Zero Trust
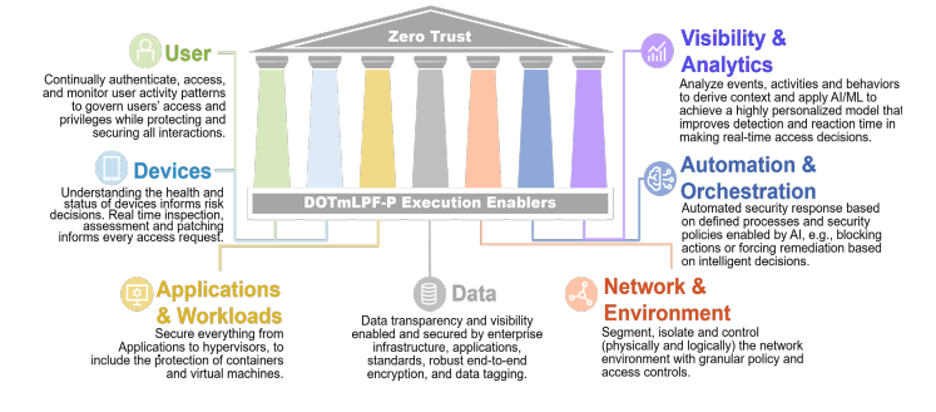
The DoD Zero Trust Strategy puts forth a clear path so that it can be achieved and provides a road map via seven DoD Zero Trust Pillars (providing a capabilities-based execution plan) across their Non-classified Internet Protocol Router Network (NIPRNet) and Secret Internet Protocol Router Network (SIPRNet). It is a major cultural change and a philosophy shift from legacy authentication and security mechanisms allowing effective data sharing in partnered environments.
“The Framework outlines an official blueprint to modernize cybersecurity for the DODIN NIPRNet and SIPRNet.”
The strategy has DoD enterprises secured by a “fully implemented” Zero Trust cybersecurity framework by Fiscal Year 2027, reducing the overall attack surface, and quickly containing and remediating bad actors’ activities. The strategy does not mandate or prescribe specific technologies or potential solutions. It does, however, describe all the Zero Trust capabilities needed that must be implemented.
The strategic goals and corresponding objectives define what the DoD will do to achieve Zero Trust.
- Zero Trust Cultural Adoption: A Zero Trust security framework and mindset that guides the design, development, integration, and deployment of information technology across the DoD Zero Trust Ecosystem.
- DoD Information Systems Secured and Defended: DoD cybersecurity practices incorporate and operationalize Zero Trust to achieve enterprise resilience in DoD information systems.
- Technology Acceleration: Zero Trust-based technologies deploy at a pace equal to or exceeding industry advancements to remain ahead of the changing threat environment.
- Zero Trust Enablement: DoD Zero Trust execution integrates with Department-level and Component-level processes resulting in seamless and coordinated Zero Trust execution.
DoD Zero Trust Pillars
The seven pillars of Zero Trust are depicted below and include Users, Devices, Applications & Workloads, Data, Network & Environment, Automation & Orchestration, Visibility & Analytics.
The National Institute of Standards and Technology (NIST) Special Publication (SP) 800-207, Zero Trust Architecture provides the underpinnings for the DoD Zero Trust Security Model and the DoD Zero Trust Architecture, with seven key tenets for an ideal Zero Trust implementation. These seven tenets of Zero Trust are:
- All data sources and computing services are considered resources.
- All communication is secured regardless of network location.
- Access to individual enterprise resources is granted on a per-session basis.
- Access to resources is determined by dynamic policy.
- The enterprise monitors and measures the integrity and security posture of all owned and associated assets.
- All resource authentication and authorization are dynamic and strictly enforced before access is allowed.
- The enterprise collects as much information as possible about the current state of assets, network infrastructure, and communications and uses it to improve its security posture.
Within the seven pillars, the DoD has broken down a subset of 45 separate capabilities. Each capability breaks down into a series of associated activities to provide further guidance around the DoD Zero Trust implementation. DoD Strategy has also stated that components must achieve Zero Trust “Target Level” as soon as possible (FY2023 and no later than FY2027) and work towards an “Advanced” Zero Trust Level after that.
It is important to note that the DoD Strategy states that “reaching an advanced state does not mean an end to maturing Zero Trust; instead, protection of attack surfaces will continue to adapt and refine as the malicious events methods advance and mature.” Implementing a Zero Trust architecture is not a “one-and-done” initiative, but a continuous journey towards better security.
DoD Zero Trust capabilities
The DoD Zero Trust Capabilities are listed below and will be mapped to our Cisco Secure products in an upcoming Blog:
1. User
1.1 User Inventory
1.2 Conditional User Access
1.3 Multi-Factor Authentication
1.4 Privileged Access Management
1.5 Identity Federation user Credentialing
1.6 Behavioral, Contextual ID, and Biometrics
1.7 Least Privileged Access
1.8 Continuous Authentication
1.9 Integrated ICAM Platform
2. Device
2.1 Device Inventory
2.2 Device Detection and Compliance
2.3 Device Authorization with Real Time Inspection
2.4 Remote Access
2.5 Partially & Fully Automated Asset, Vulnerability and Patch Management
2.6 Unified Endpoint Management (UEM) & Mobile Device Management (MDM)
2.7 Endpoint & Extended Detection & Response EDR & XDR)
3. Application & Workload
3.1 Application Inventory
3.2 Secure Software Development and Integration
3.3 Software Risk Management
3.4 Resource Authorization & Integration
3.5 Continuous Monitoring and Ongoing Authorizations
4. Data
4.1 Data Catalog Risk Assessment
4.2 DoD Enterprise Data Governance
4.3 Data Labeling and Tagging
4.4 Data Monitoring and Sensing
4.5 Data Encryption & Rights Management
4.6 Data Loss Prevention (DLP)
4.7 Data Access Control
5. Network and Environment
5.1 Data Flow Mapping
5.2 Software Defined Networking (SDN)
5.3 Macro Segmentation
5.4 Micro Segmentation
6. Automation & Orchestration
6.1 Policy Decision Point (PDP) & Policy Orchestration
6.2 Critical Process Automation
6.3 Machine Learning
6.4 Artificial Intelligence
6.5 Security Orchestration Automation & Response (SOAR)
6.6 API Standardization
6.7 Security Operations Center (SOC) & Incident Response (IR)
7. Visibility & Analytics
7.1 Log All Traffic (Network, Data, Apps, Users)
7.2 Security Information and Event Management (SIEM)
7.3 Common Security and Risk Analytics
7.4 User and Entity Behavior Analytics
7.5 Threat Intelligence Integration
7.6 Automated Dynamic Policies
In Part 2, we will go deeper into the model and how Cisco capabilities can support any Federal organization’s Zero Trust journey. Cisco is looking forward to continuing our partnership with the DoD to make Zero Trust a reality for our nation’s warfighters.
Learn More
- Department of Defense Press Release for Zero Trust Strategy and Roadmap
- DoD Zero Trust Strategy
- Cisco Zero Trust Frameworks Architecture Guide
[1] https://federalnewsnetwork.com/defense-main/2022/08/dod-to-release-start-implementing-new-zero-trust-strategy-by-oct-1/





