The prior blogs in this series, listed at the bottom, have discussed the various regulations affecting CIOs and their IT organizations. The purpose of this plan was to understand the application and complexity of these regulations as they apply to technologies, so that we can evaluate technologies used to help teams satisfy these requirements. The purpose of this blog is to discuss a few ways in which tooling and automation capabilities can be used to satisfy the asset management requirements of the FFIEC Operations Guide.
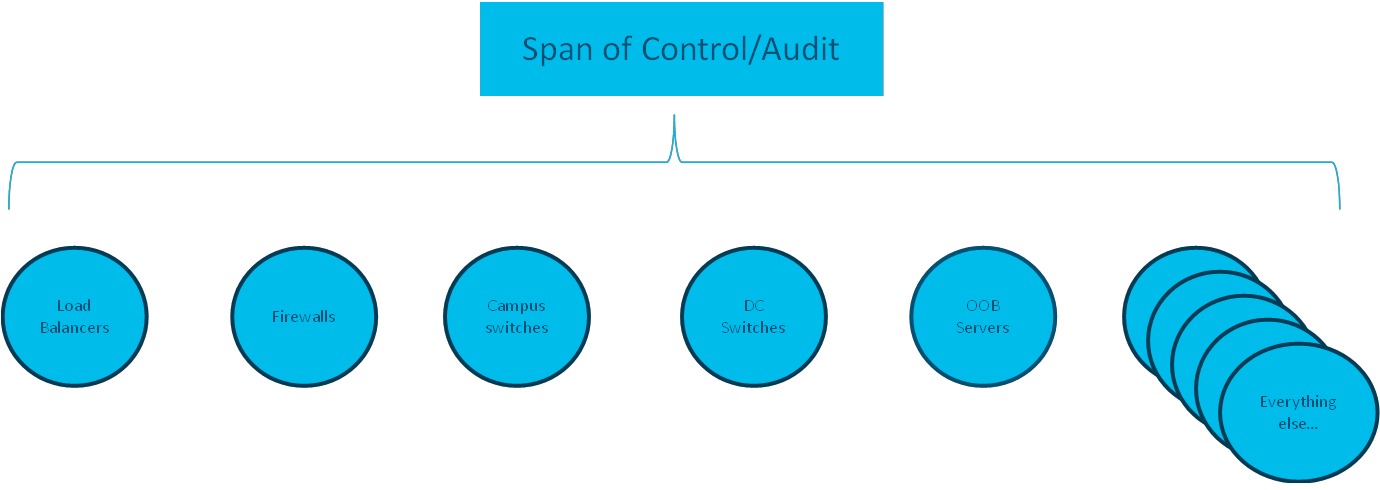
Financial institutions are regulated to be able to manage, secure, and audit their IT assets. They cover multiple product sets with different operating systems by nature, and are tasked to create a cohesive asset management framework. At Cisco, we work with these different groups, and their deployments of best in class technologies. However when we are dealing at the regulatory level, we need to step back from our traditional way of doing business and consider the bigger picture.
From the regulators perspective, they don’t care about how you manage and patch your data center switches.
And they don’t care how you manage and patch your campus switches.
Or the load balancers.
Or virtual machines.
The regulatory bodies and senior leadership care about ALL of it. From the physical to the virtual, from the endpoint to the cloud. Thus a framework to be able to merge together different systems is fundamental to the role.
The IT Administrators and their leadership are tasked with knowing, patching, and securing all of their network.
Here are two different approaches that help manage the assets across the breadth of the estate.
- An enterprise-ready, multi-vendor cross-architecture solution that is built on over a decade of doing this for Service providers.
- A functional code example of how existing Cisco controller solutions can be pulled together at the API level to create a framework (from which other vendors can be included), to be able to ensure your knowledge of your span of control is up to date and can be assessed.
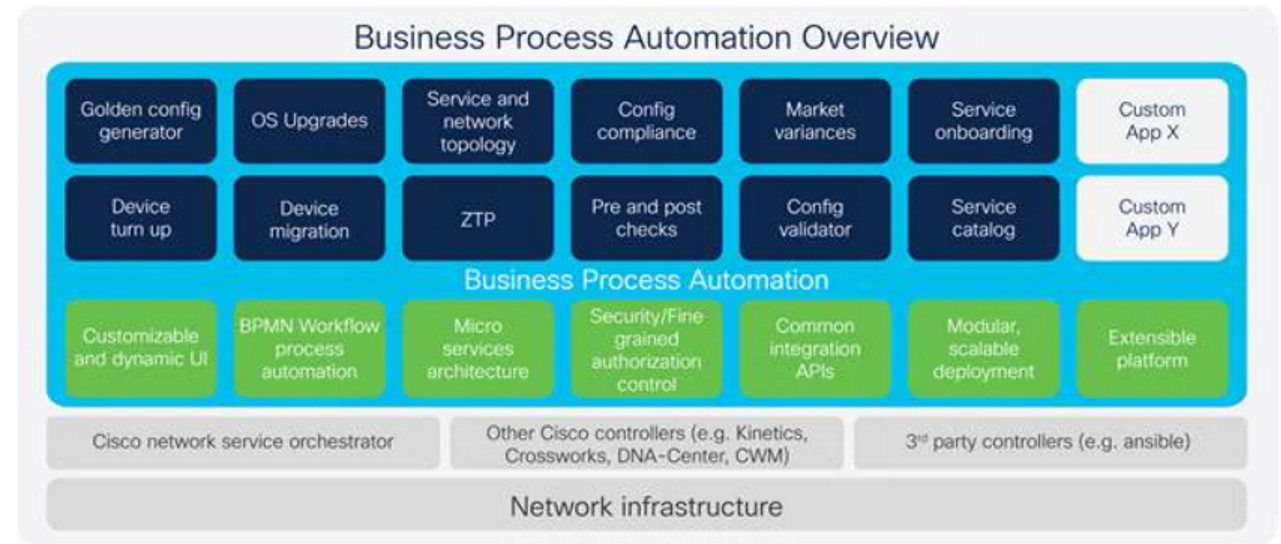
Using Cisco Business Process Automation
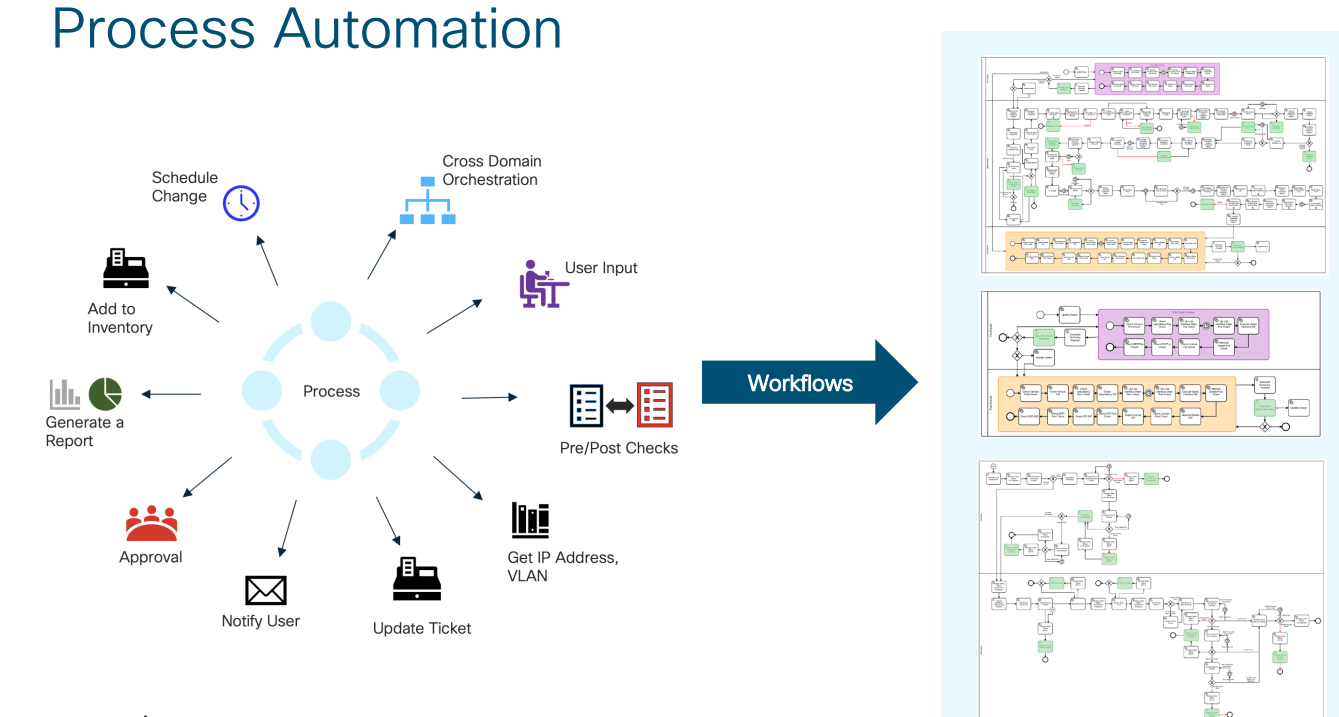
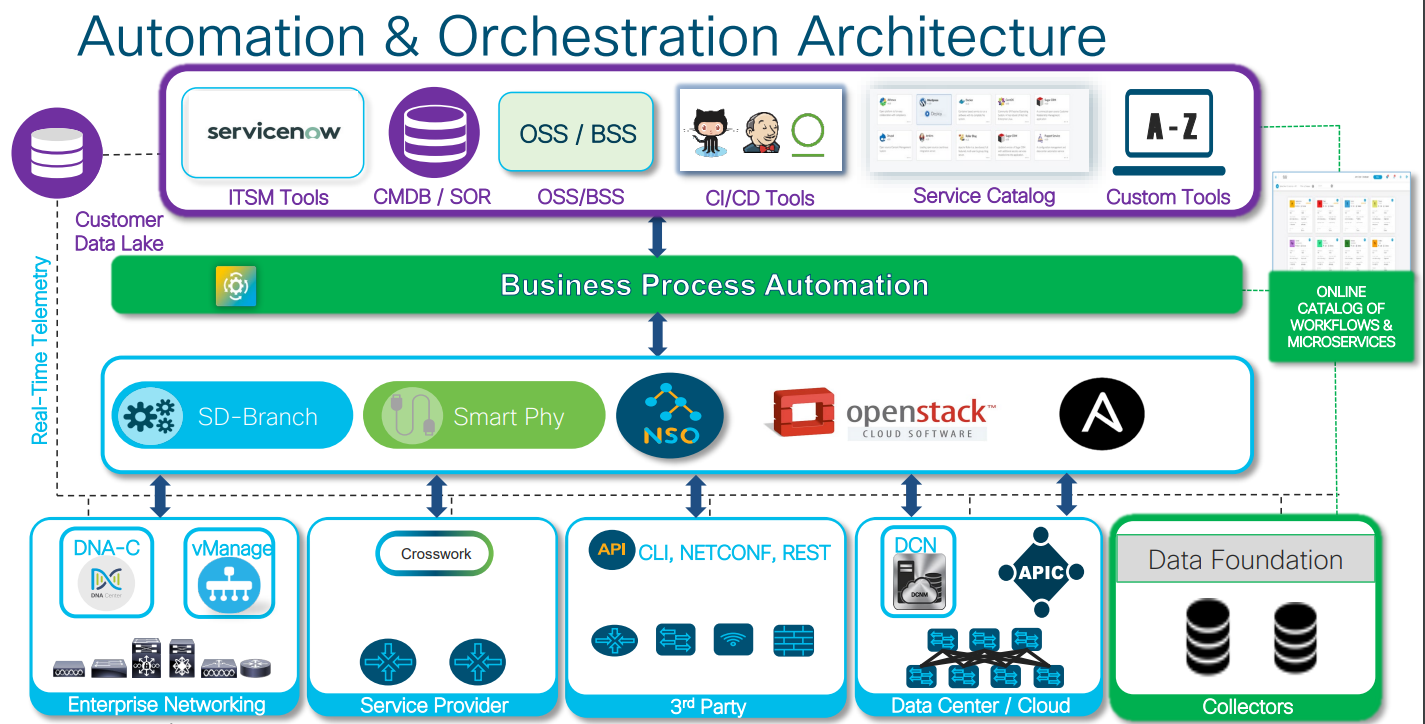
The first solution is Cisco’s Business Process Automation. This is a scalable, microservices based platform that is vendor AND controller agnostic. It is pre-integrated with Cisco NSO and Ansible and is capable of working with other Cisco and third party orchestrators. It provides the ability to automate and monitor operating system automation and configuration compliance with golden images.
The benefit of this approach is you can abstract the entirety of the span of control and work on provisioning consistent services securely. It provides an API which can allow for easy auditing of the entire breadth of the environment, from the physical to the virtual, including third parties. It supports multiple workflows to be able to manage a compliant infrastructure, from device onboarding with ztp, handling asset management, and ensuring golden software and configurations are applied and compliant.
BPA allows us to incorporate the business logic and integrate change management with inventory management, to meet the organizations requirements and move to an Infrastructure as Code mode of operation. Its inherent support for multiple controllers fits in well with the requirements financial institutions have to support their existing infrastructure, including legacy and modern constructs.
Using Controllers and API based Solutions
The second approach is to leverage a home grown solution where a framework is created to be able to extract and monitor compliance of an entire estate in a multi-controller and multi-vendor world. This can be useful for organizations that already have in house tooling or capabilities, and seek to manage their controllers at the API level
We intend to show how this can be done practically using diverse Cisco hardware and software, and the framework would bolt in to any other third party and provide functional, easy to use code, that can create a single asset management table for products in the Cisco portfolio.
We do this by integrating the below controller solutions into a single table which can be cross referenced and then pushed, into ServiceNow:
- ACI
- Multiple DNAC instances
- Meraki
- Intersight
- Cisco SD-Wan
As of December 2022 it is done in cloud-based devnet sandboxes. There is also a reference on how this can be reconciled and pushed into ServiceNow (so that the system of record can be updated following software changes, or reconciled). The code to be able to do this is all functional, with the only exception being you will need to provision a ServiceNow account or developer instance (and modify the authentication/URL).
This is functional code, which is easy to run against real sandbox environments, and can be validated and repurposed for your environment.
While we cannot control third-party products and how they integrate, the framework would allow for other equipment which support REST API to create a state table for inventory asset management. The framework is rather straightforward, capture inventory from diverse systems using REST API, and normalize to a consistent list of all assets in those systems. From there, you can update ServiceNow or another system of record.
This process is discussed in greater detail in this blog, but the highlight is it uses an easy to run (so easy a barista with no programming experience can do it!), and uses our cloud infrastructure to show the functional code and framework: Cross Domain Inventory Demo
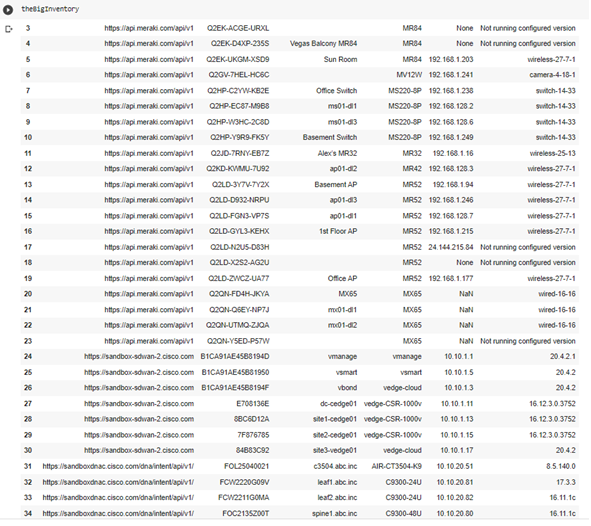
The end result is a cross domain inventory of multiple Cisco products and a framework for adding other vendors, into a consistent table of network state, which can be used to validate compliance. This can then be used to update your system of record (ServiceNow) with your system of truth, to ensure your documented state is up to date with your operational state.
Secondarily, the script uses an example of pushing in ServiceNow to show how to compare of a system versus a system of record. In my example it uses ServiceNow as a system of record, and gets the current documented state from ServiceNow. It then does a Pandas SQL join to show the difference between the system and the system of record, and allows you to update the system of record (ServiceNow).
The same mechanics apply to comparing the system versus a list of golden images, validating software across all systems versus the golden images required.
Comparing current state versus ServiceNow
InventoryNotInSvcnow_df=theBigInventory.merge(svcnow_inventory_df, how = ‘outer’ ,indicator=True,left_on=[“Hostname”,”IP Address”,”Model”,”Version”], right_on=[“name”,”ip_address”,”model_number”,”firmware_version”]).loc[lambda x : x[‘_merge’]==’left_only’]
Comparing current state versus list of standard images (what is versus what we expect)
InventoryNonConformant_df=theBigInventory.merge(GoldenImages, how = ‘outer’ ,indicator=True,left_on=[“Model”,”Version”], right_on=[“Model”,”firmware_version”]).loc[lambda x : x[‘_merge’]==’left_only’]
There are multiple ways to leverage Cisco products in a holistic method to meet FFIEC asset management requirements, via either the base API or through a complete turnkey solution (and different options in between). The next blog will cover how to use the different controller based products to meet other areas of the regulatory requirements.
Prior Blogs
Introduction to Understanding FFIEC Regulations
FFIEC Cybersecurity Maturity Tool
The FFIEC’s Architecture, Infrastructure, and Operations Book