Financial institutions have to be vigilant in the face of a continually evolving cybersecurity threat landscape. As these have attacks have evolved, regulatory bodies have updated their regulations to account for the increasing threat of cyber risk. In 2015, following a significant increase in nation state and hacktivist attacks on U.S. financial institutions, the FFIEC released new guidance and a Cybersecurity Assessment Tool for institutions to self assess their risks and determine their cybersecurity maturity. This was revised in 2017, and this consistent framework is intended to be able to help leadership and the board assess their preparedness and risk over time. This framework is especially relevant given the recent FFIEC Architecture and Operations update and the Executive Order on Cybersecurity from 2021.
The purpose of this blog is to assist our IT based customers and partners with a concise and high level understanding of the FFIEC Cybersecurity Assessment Tool and derivative impacts on their current and future day to day operations. It is part of a multipart blog series on financial regulations and how to manage them architecturally, geared towards IT leadership.
The Cybersecurity Assessment Tool is fairly intuitive to use and the exercise should not be arduous for an organization to complete. The assessment applies principles of the FFIEC IT Handbook and the NIST Cybersecurity Framework. The intention here was to be complimentary to existing frameworks and supportive of existing audit criteria. The FFIEC has released a mapping of the Cybersecurity Assessment Tool and the NIST Cybersecurity Framework to the FFIEC IT Handbook.
How the Assessment works:
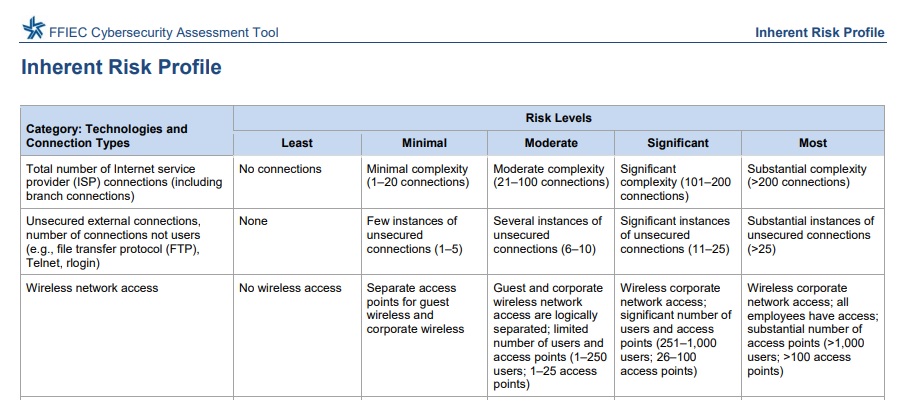
The assessment itself involves two primary components: an institution first creates an inherent risk profile based upon the nature of their business, and determining cybersecurity maturity. The inherent risk profile is an institution’s analysis of its key technologies and operations. These are mapped into categories and include:
- Technologies and Connection Types
- Delivery Channels
- Online Mobile Products and Technology Services
- Organizational Characteristics
- External Threats
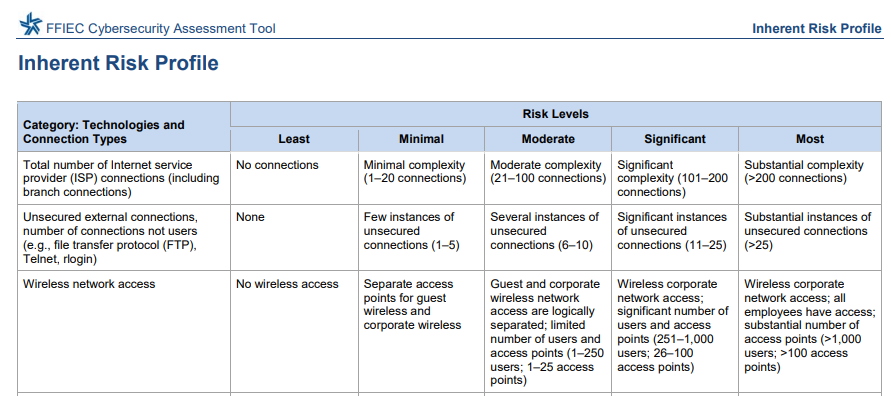
The tool itself provides guidance on criteria to sell assess risk based on the different characteristics of an organization, which simplifies completion as well as consistency. By having explicit guidance on how to self assess into different risk categories, the leadership for the institution can ensure they have a consistent understanding of what the risk entails.
Below is a snippet of the inherent risk profile, of note is the intuitive and consistent guidance on how to classify risk within each domain.
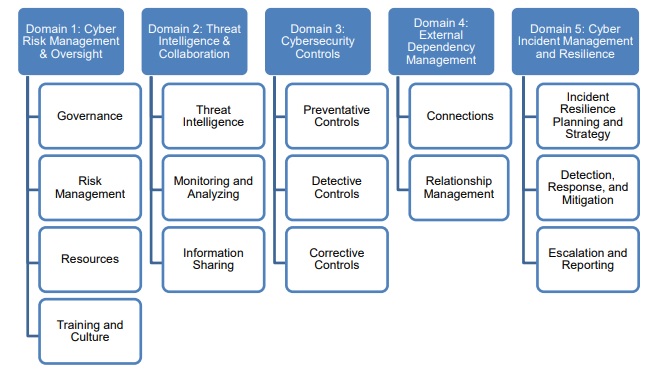
The second aspect of the assessment is understanding cybersecurity maturity. This section can help leadership understand the risk and appropriate controls which have been put into place. It creates five levels of maturity, from baseline to innovative, and we use these to measure preparedness of the processes and controls for five risk domains:
- Cyber Risk Management and Oversight
- Threat Intelligence and Collaboration
- Cybersecurity Controls
- External Dependency Management
- Cyber Incident Management and resilience.
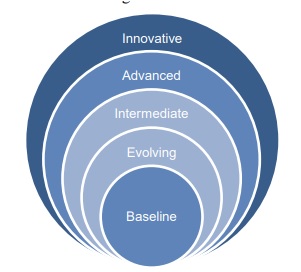
The five domains include assessment factors and declarative statements to help management measure their level of controls in place. What this means is there are statements within each assessment factor that describe a state. If those descriptive statements matches a financial systems controls, then they can claim that level of cybersecurity maturity. Of important note however, as in the picture above, the levels are additive, like a hierarchy of needs. What this means is that if there is a statement in innovative that matches some of your organizations controls, but you haven’t satisfied the statements in the “advanced” guidance, you can not measure your institution as innovative in that domain. Likewise, an intermediate level of maturity assumes that all criteria in the evolving level, have been met.
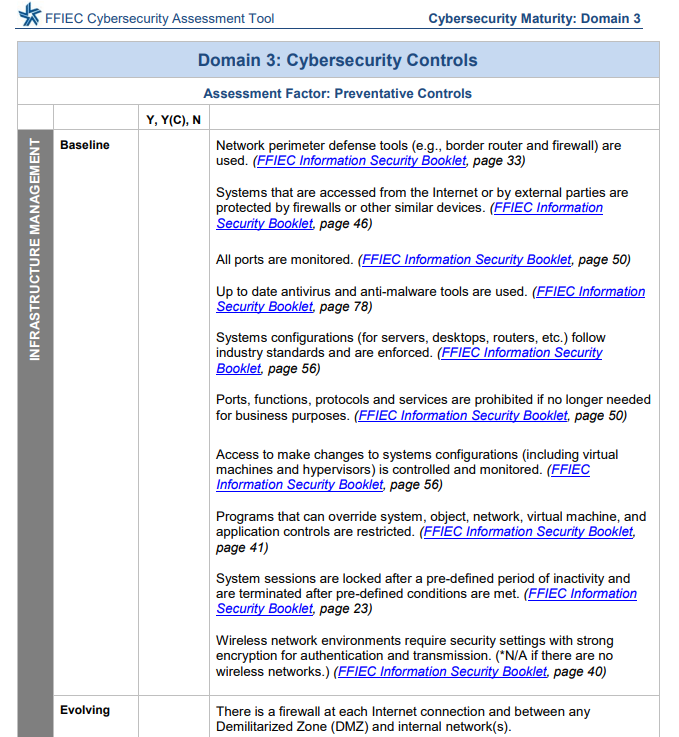
The five domains each have various assessment factors. For example, in cybersecurity controls there are assessment factors for preventative, detective, and also corrective controls. Each of these assessment factors will have contributing components which are then measured. An example of this is within the preventative controls assessment factor, there is components such as “infrastructure management” and “access and data management”.
It becomes easier to envision when evaluating the assessment document and the corresponding components. As can be seen in the below cybersecurity guidance, there are a number of explicit statements that describe maturity at a particular level and mapping to regulatory requirements. Through satisfying these statements you can appropriately match your institution to its level of cybersecurity maturity.
The Next Step
Following completion of an inherent risk profile and cybersecurity maturity an organization can determine if they have the appropriate controls in place to address their inherent risk. As inherent risk increases, obviously a higher level of security controls should be positioned to provide a level of control around that risk. A conceptual guidance on how risk should map to maturity is outlined below. Where this becomes important is not only in determining a point in time deficiency, but understanding that as new projects, acquisitions, or the threat environment changes, leadership can understand whether increases in security controls need to be applied to adequately address a material change in risk level.
Derivative Impacts on Infrastructure and Security Teams
The Cybersecurity Assessment is a useful tool for financial institutions to consistently provide leadership a synopsis of the state of the institution. But how this translates downstream to day to day operations of architects may not be explicit. There are a number of areas in the Cybersecurity Maturity section where explicit guidance is given which we have seen undertaken as projects at our customers, as well as across the industry. Below are a few themes we have seen gain in prominence since the publishing of the assessment. These weren’t generated by the assessment itself, but are common themes across the industry. Through this blog, the intent is more to provide a high level synopsis of how these projects influence, and are influenced by, and measured through, the regulatory bodies.
- Segmentation is explicitly called out with guidance given on how to measure. We have seen this translated across the industry as both Macro and Micro segmentation approaches, and both of these are complimentary. These have driven technologies such as SD-Wan, SD-Access, ACI, and VXLan based segmentation.
- Managing infrastructure and lifecycle hardware and software versions are measured. This practice isn’t specific to just this assessment and it has become a common theme to be able to keep devices in patch management. It is a shift from some institutions “sweating their assets” to a proactive model for managing. What had been observed was “hackers love sweaty assets”, with most exploits targeting known vulnerabilities. This should translate into any new technology investment having a lifecycle that can ensure the full depreciation of the asset while maintaining patch management.
- Analytics and telemetry have driven significant investments in cybersecurity operations team’s ability to understand and act upon emerging threats in real time. Leveraging existing assets as sensors or sources of meaningful telemetry is important as deploying dedicated appliances to the larger attack surfaces of campuses, branches, and wireless nd can be prohibitively expensive plus operationally unsupportable.
The above is just a few of the many derivative impacts that affect our infrastructure and security teams. With increasing nation state guidance on security and privacy, to include the U.S. Executive order on Cybersecurity, additional tightening of conformance to address evolving security risks is happening. A lot of the increased focus aligns to areas which occur within existing domains that are included in existing frameworks. The FFIEC Cybersecurity Maturity Assessment is a simplified tool that can help a board member understand which security controls should be addressed first.
The Cybersecurity Assessment Tool and corresponding information are great sources to keep your institution’s cybersecurity threat on target.




